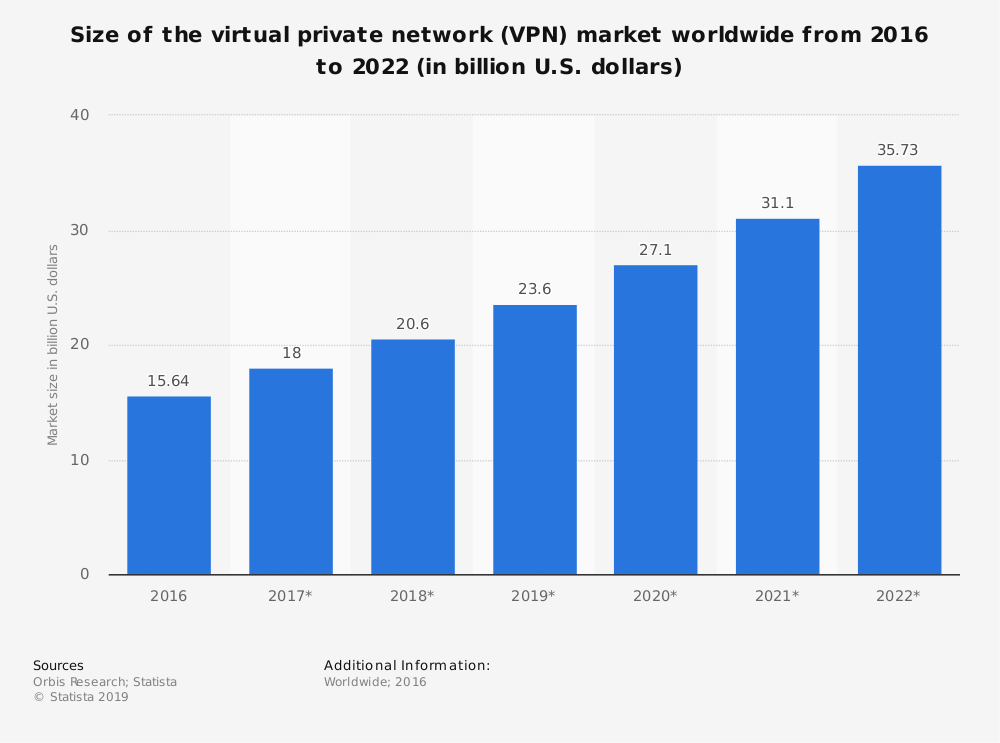
The VPN industry is steadily growing in size over the past few years. The rising trend in growth is projected to continue on in its progressive trajectory because of the prevailing high demand for VPNs.
Although there are hundreds of VPN providers in the market and this number is only likely to increase, there are only two broad types into which all VPNs fall.
In this article, we are going to see the two different types of VPNs as well as briefly introduce some of the core components of a VPN that is necessary to its function and explain their types.
But before we go ahead, you might want to see which of the brands are offering the best quality of VPN services in 2022.
Types of VPN
All VPN services can be broadly categorized into two types:
- Remote Access VPN
- Site-to-Site VPN
Remote Access VPN
Remote Access VPN is the most common type of VPNs that are deployed for personal use. In fact, almost every VPN service you can find on the web for the average consumer is a “Remote Access VPN”. You can check out some of the Best Remote Access VPNs in USA here.
This kind of VPN basically connects a home user to one of the remote servers owned by the VPN provider/administrator.
These servers can be part of a large or a small network and located across different parts of the world. A user can virtually connect to any of these server locations, which will result in a change in their IP address depending on the location with which connection is currently established.
Common motivations for connecting a server in a different location is to gain access to websites that are only accessible to people having an IP address based in said location.
The “tunneling” mechanism of these VPNs also provides excellent security through encryption to your data.
Moreover, these VPNs are usually based in countries with privacy-friendly jurisdictions. By simply connecting to these VPNs, you can route your data through the remote network where no usage logs related to you will be stored (assuming the provider follows a no-logging policy).
As such, remote access VPNs like ExpressVPN, Surfshark, NordVPN, etc. are highly effective tools for the average user seeking greater privacy and security on the web.
Site-to-Site VPN
A site-to-site VPN is commonly used in business settings to facilitate employees and business owners to connect to their organization’s network remotely.
In large organizations having offices spread over the different geographical region, site-to-site VPNs come in real handy by enabling employees to access the company’s systems and even work remotely in their physical absence.
Site-to-site VPNs can be either intranet based or extranet-based. An intranet-based site-to-site VPN is used to access networks of the same company from different offices.
Extranet-based VPNs, on the other hand, are private networks especially designed to allow two or more different companies to connect to each other’s network for business purposes.
You can think of site-to-site VPNs a tunnel that joins all the different remotely located offices of one or more companies through layers of strong encryption.
The utility of site-to-site VPNs isn’t simply in the accessibility it offers to employees on the go. Corporates use these VPNs to secure their networks from third parties by isolating it from the larger Internet, thus reducing the chances of a data breach and other security attacks.
For a more in-depth explanation of how VPNs really work, you can read my article “What is a VPN”?
VPN Architecture
The architecture of VPNs has very few variants that have only recently developed. For the most part, VPN providers use the traditional VPN architecture which involves a VPN client (the user’s computer/device) routing user traffic to the VPN provider’s datacenters/servers.
The VPN then transmits the user requested web pages/services through the same path until it reaches the client end.
All of the remote servers in the network of a VPN pass through a central hub/headquarters of the provider.
This traditional architecture works reasonably well for the requirements of the average user and there are no commercial VPNs using any other type of architecture.
However, a different kind of VPN architecture is capturing the interest of network experts. This is known as Dynamic Multipoint VPN.
DMVPN (Dynamic Multipoint VPN)
DMVPN is a form of network architecture that makes it possible for servers to exchange without needing to pass through the central hub/headquarter of the VPN.
In short, all VPN servers can directly communicate with each other and to the end user, eliminating the extra stage of needing the data to pass through VPN headquarters for all communication.
All the servers in the network are capable of providing access to the headquarters’ resources. In this mesh topology, the servers are referred to as “spokes”, and the configuration can be understood as a “spoke-to-spoke” deployment.
This architecture has some definite advantages over traditional architecture in the following ways:
- DMVPN reduces bandwidth requirements at the hub because all the spokes are self-sufficient
- There are fewer hops in DMVPN needed to communicate from client to VPN server, thus reducing network delays
- Superior redundancy and resilience of the whole network
- Lower cost for VPN circuits
Types of VPN Protocols
Each type of VPN can implement a variety of different VPN protocols. VPN services need protocols to communicate between the servers, clients, and also control authentication as well as encryption.
The most common VPN protocols that are implemented by service providers are:
- PPTP
- L2TP
- IPSec
- OpenVPN
- IKEv2
These protocols are listed in the order that they were developed with OpenVPN and IKEv2 being the most modern of these protocols.
For a technical detail about these concepts, read our article on VPN protocols and what differentiates these.
VPN Encryption
Encryption is a crucial aspect of VPN technology. In fact, it is encryption that gives all the security to your data packets and makes it difficult for an unknown party to execute a data breach on your system.
Cryptography is the science behind encryption and it happens to be extremely complicated for a layman to understand. Over the years, developments in this field have led to the creation of a variety of algorithms and standards, each with different levels of complexity and suitability for the purpose in question.
Within the VPN industry, providers almost entirely use the modern AES (Advanced Encryption Standard), a highly secure and one of the more modern cryptographic method.
The AES itself has many variants which arise by using different key lengths for the encryption cipher. Most VPN providers today offer AES-128 and/or AES-256 bit encryption.
This is a sufficient encryption strength for almost every case. Anything higher would be overkill since only a probabilistic miracle could break encryption with 256-bit key length.
The common types of encryption include:
- Blowfish
- 3DES
- AES-128
- IPSec
- MPPE
- Camellia
- AES-256
If you want to learn the technicalities behind these, have a look at our article What is VPN encryption?
Final Thoughts
There are hardly any differences between VPN services in terms of how they operate. The differences arise only in terms of architecture and how the client communicates with destination servers.
I hope this article helped you understand what types of VPN services there actually are and what it implies for you, the user.
