VPN Leaks, sounds weird right?
What leak am I talking about? Believe it or not, no matter the level of encryption your VPN provider promises to provide, it can very well be susceptible to DNS, WebRTC and IP leaks.
Now I know you have no idea about DNS, WebRTC and IP leaks, but bear with me as I’ll discuss everything in great detail in this VPN leak test guide.
But right now, what I’m trying to say is, you can’t put your blind faith in VPN providers. According to a research, out of 150 VPN apps on Google Play Store, 25% of them suffered from DNS leaks.
IP and DNS leaks are not just limited to Android apps. A study released by Internet Measurement Conference revealed 25 out of 62 VPN providers to be leaking user’s traffic.
Based on such strong concerns, I’ve decided to conduct my own VPN test.
To conduct one of the most thorough research on the internet, I’m going to cover 55 VPN providers in the industry and see which VPNs fail to fulfill their destined purpose.
But before we begin, let’s first start by talking about VPN leaks and its types.
What is VPN Leak?
Now there’s no textbook definition of VPN leaks, but based on my VPN test, I would explain it as:
A VPN leak occurs when user’s real IP address or DNS is disclosed despite using a VPN’s encrypted private tunnel
More specifically:
- When a VPN app allows the flow of unencrypted traffic from the device
- When a VPN app exposes public IP address to third parties
- When a VPN app sends user’s DNS requests to public DNS servers other than that of the VPN provider
I bet you’ve experienced one of these leaks at least once with your own VPN service. And why not? After all, leaks are pretty common with low-end or budget VPN services. We’ve found ExpressVPN as the best VPN with DNS leak protection and provides complete security with high connectivity speeds.
Here’s a scenario for you:
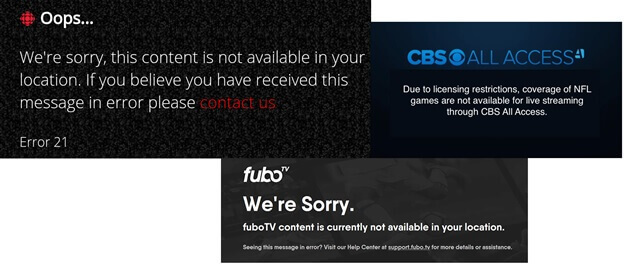
Let’s say you connect to a VPN server of your choice and try to access to a geo-blocked website. Everything seems fine and dandy, but you’re still unable to access that particular content.
The reason is simple, the service or website you are trying to access is actually tracking your true IP rather than the IP of your VPN provider. That’s a clear indication of a VPN leak.
But you can’t entirely blame your VPN provider for leaks. While VPN leaks do have a lot to do with bugs and flawed protocols (more on that later), unaddressed vulnerabilities in existing technology are the prime suspect for leaking your true identity.
What technologies am I talking about?
Browser using WebRTC, browser plugins and even operating systems on our phones and other devices are just to name a few.
Types of VPN Leaks
There are essentially three (3) different types of leaks you should be concerned about:
- IP address leaks (IPv4, IPv6, and Torrent IP leak)
- DNS leaks
- WebRTC leaks
Let’s start with IP leaks first…
IP Address Leaks
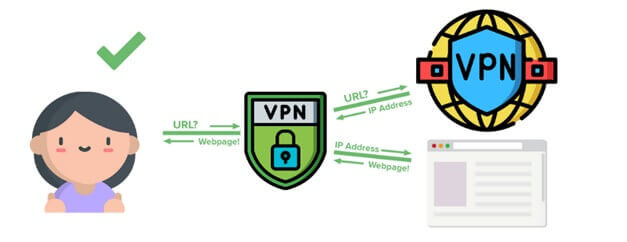
In essence, a best VPN services is meant to protect your online privacy by establishing a secure encrypted tunnel between you and the internet.
It’s meant to obscure your identity and online activities from the rest of the world, by masking your original IP address.
Since your IP address is your unique identifier, if your VPN service suffers from leaks, it can very well compromise your online privacy.
Even if someone can’t necessarily hack you using your IP, it can easily disclose a lot of information about you. Here’s what simply looking up an IP address on whatsmyip.com can reveal about someone:
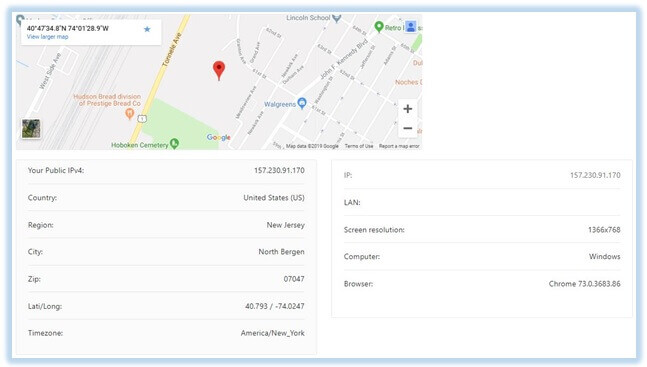
A seemingly harmless IP leak can, in fact, reveal something as sensitive as your actual geo-location down to the exact coordinates.
A leaking IP address is also the reason why you aren’t able to access geo-restricted content and services.
But it gets even worse:
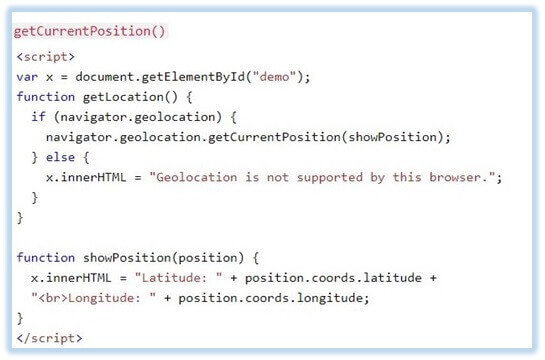
If someone really wants to settle an unfinished gripe with you, they can easily send you a link laced with HTML5 geolocation API to get your exact geo-location without you even knowing about it. [Source]
DNS Leaks
Domain name server or DNS is essentially a phone book of the internet. It’s an intermediary entity between a user’s device and the Internet.
DNS servers convert hostnames (such as www.example.com) into a computer-friendly IP address (such as 192.911.1.1).
Since we remember words better than the long combination of numbers, it would be excruciatingly difficult for us humans to memorize each and every IP address we wish to access. [Source]
Just imagine typing in 157.166.226.25 just to visit CNN. A helpful technology indeed. However, when using a VPN, this seemingly useful technology can also be the reason for your flawed privacy.
Allow me to explain…
Sometimes, even with the VPN enabled and working perfectly, your VPN app might not handle your DNS request directly. Instead, it might allow your DNS queries to pass through your IPS’s DNS servers.
This is referred to as a “DNS leak.”
In case you suffer a DNS leak, your internet service provider or the third party DNS operators that handle your queries, can see which websites you visit or which apps you use.
Since DNS is what connects web links together, DNS can adversely affect pretty much everything you do online. A double-ended sword indeed.
If a VPN provider doesn’t handle your DNS queries, this vulnerability can not only allow ISPs, but other entities to eavesdrop on your internet activities.
Now as I said earlier, you can’t blame everything on your VPN provider, as vulnerabilities in existing technology can also constitute a leak.
Take for example Microsoft’s Smart Multi-Homed Named Resolution”. Initially released with Windows 8, SMHNR has serious DNS leakage issues.
Even with the VPN in place, SMHNR sends DNS queries to all configured DNS servers instead of just using the VPN providers DNS servers. [Source]
This obviously discloses your true IP along with the sites you visit, rendering your VPN totally useless. However, it is somewhat easy to disable, if you know what you’re doing.
But Microsoft’s flaws don’t just end there, in fact, Windows 10 is even worse at handling DNS requests with a VPN.
To put this into perspective, due to Windows 10’s pathetically poor DNS handling mechanisms, CISA wing of the Department of Homeland Security issued an official alert (TA15-240A).
Yeah! That’s how bad it is.
That said, some VPNs do come with built-in DNS leak protection. This feature ensures all DNS requests are handled securely within the encrypted VPN tunnel.
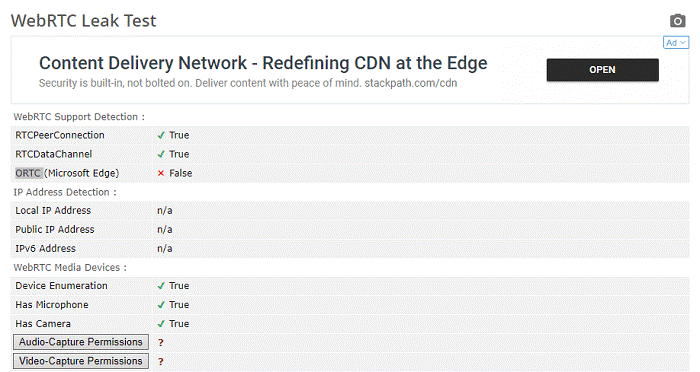
WebRTC Leaks
WebRTC or Web Real-Time Communication is a (VoIP) voice over Internet Protocol for online communications. It’s the same technology that powers super useful apps like WhatsApp and Skype
Although a revolutionary technology, it can still expose your real IP address even when you are using a VPN.
WebRTC enables browser-to-browser applications such as voice calling, and video chat Platforms. So, ExpressVPN is the secure VPN for Omegle, Skype, and other VoIP Platforms.
According to an article published by TorrentFreak, the massive flaw of WebRTC technology allowed websites to see the home IP-addresses of unaware users.
TF further added that websites can use few lines of code to make requests to a STUN server that could then log users VPN IP-address, home IP-address, and even local network addresses.
Since WebRTC is essentially a browser-based technology, modern browsers are the most vulnerable.
Daniel Roesler, an independent developer was the first to disclose the WebRTC vulnerability back in 2015. He even published code on his GitHub page that allowed users to rectify whether their browsers suffered from WebRTC leaks or not.
With that being said, as nasty as WebRTC leaks sounds, it is relatively easy to patch. I’ll cover it later on in this guide.
VPNs & Unpatched Vulnerabilities
Okay, so sometimes your VPN provider might be the culprit behind your flawed privacy. Take for example the infamous Heartbleed bug of 2014.
Heartbleed bug
This Bug aids the interception of files and data protected under the SSL/TLS encryption. Heartbleed vulnerability typically affects emails, instant messaging (IM) and even some virtual private networks (VPNs).
The horrendous bug allows anyone to decrypt encrypted traffic by abusing the vulnerable versions of OpenSSL. As a result, anyone with malicious intent can potentially gain access to confidential credentials and possibly use it for eavesdropping, stealing or even impersonation.
What makes Heartbleed Bug so unique?
Well, unlike other single software bugs that get patched with new updates, the Heartbleed bug has exposed a relatively large number of private and other secret keys exposed to the Internet.
Since this bug is obnoxiously easy to exploit and leaves no trace when executed, it is one nasty Vulnerability.
Privilege Escalation Bugs
Privilege Escalation Bug is another major vulnerability that just surfaced recently. The bug was discovered by Security researcher Paul Rascagneres from Cisco Talos in two mainstream VPN clients
According to Rascagneres’s published report, he identified two privilege escalation bugs in both NordVPN (CVE-2018-3952) and ProtonVPN’s (CVE-2018-4010) Windows clients.
He further explained in his report that since both VPN providers used OpenVPN requiring administrator access, any malicious code running inside the OpenVPN configuration file could override admin rights.
Now, what does that mean?
For easy understanding, anyone gaining admin access could manipulate configuration files by inserting their own malicious codes and executing arbitrary commands with the very specific code execution parameters.
Rascagneres also added that the reason why this vulnerability even existed is because of the way OpenVPN configuration files are handled by the service.
Despite being the first to identify this vulnerability in VPN apps, Rascagneres wasn’t the first to discover the bug. In fact, Fabius Watson from the VerSprite cybersecurity and consulting firm was the first to report the bug in April of 2018.
NordVPN and ProtonVPN were quick to fix the vulnerability by implementing checks specifically on “plugin” and “script-security” parameters.
However, Rascagneres was still able to bypass this patch by enclosing the said parameters within quotation marks.
Rascagneres even posted separate vulnerability reports for both NordVPN and ProtonVPN to support his findings.
These vulnerabilities were discovered in the following versions of NordVPN and ProtonVPN:
- 14.28.0
- 5.1.
With that being said, both providers have fixed this bug by releasing updates that prevent unauthorized users from modifying OpenVPN configuration files.
If you haven’t updated your VPN client yet, what are you waiting for?
VPN Leaks and its impact on your Privacy
Although VPN leaks might not be as big of a deal as VPN providers logging user data, it still can get you in a lot of trouble.
Aside from not being able to access few streaming services, leaked DNS, for instance, can result in your data being handed over to law enforcement agencies.
Allow me to explain…
Since the DNS server you use usually belongs to your ISP, all the requests you send to those DNS servers are logged and maintained in the database.
If you get involved in something that’s considered illegal in your judicial laws, your stored logs can get you prosecuted in a court of law.
For instance, in the UK, ISPs are obligated to hand over any records to the authorities under the Investigatory Powers Bill.
Considering The United Kingdom is an active part of the 5 eyes surveillance alliance, any exposed data can get you in trouble with the authorities. That is if you do actually commit something illegal.
However, in the United States, even if you’re not doing anything illegal online, ISPs can sell leaked data to marketing companies.
Ever since FCC’s broadband privacy protections proposals got repelled by Congress, internet service providers like Comcast, AT&T, Time Warner, Verizon, and others can sell personal data like web browsing history without prior consent.
According to section (D) of the 47 U.S. Code §?222. Privacy of customer information, “Nothing in this section prohibits a telecommunications carrier from using, disclosing, or permitting access to customer proprietary network information obtained from its customers, either directly or indirectly through its agents”.
Even though ISPs have been selling personal data for years, with greater power, they can generate substantial datasets on online activities of certain demographics.
To drive a point, ISPs can use gathered data to build a very precise persona of you that can be sold to marketers.
Testing Criteria
Unlike other websites that make it overly complicated to test VPN leaks by introducing advanced tools, I’m going to keep my VPN test plain and simple.
Instead of using complicated tools, I’m going to use a bunch of run of the mill online VPN leak test tools.
Reason?
To be honest, both advance and basic VPN test tools are going to yield the same results anyway, why use overly complicated methods to test VPN?
With that being said, here are some of the VPN test sites I’ll be using to test my VPN:
- https://ipleak.net/
- https://browserleaks.com/webrtc
- https://dnsleak.com/
- https://ip8.com/
- https://ipleak.org/
- https://doileak.net/
It’s also worth noting that I might not use all the above-mentioned tools for each of the VPNs I’ll be discussing in this VPN test guide. Instead, I’m going to use each of the tools in variations.
VPNs That Don’t Leak
While some VPN do occasionally suffer from leaks, there are few exceptions that don’t leak, at least that’s what I’ve experienced in my VPN test.
Down below I’ve compiled a list few paid and free test VPN that did not leak during my testing. I’ll add more VPNs to this list as I test more VPNs.
1. ExpressVPN – PASSED
Testing Server: Canada
Kicked off my VPN test with the Express VPN DNS leak test and I was more than happy with the results. As you might have noticed, my IPV6 address is not visible. That’s just of how my office network is set up.
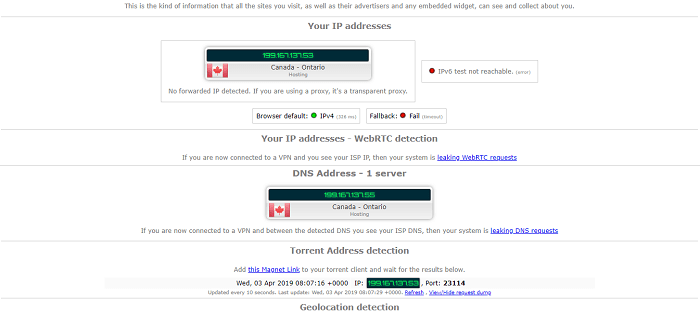
Coming down to WebRTC leak and IPLeak.net wasn’t able to detect a leak on my test VPN connection. Since I didn’t disable WebRTC in my browser prior to the test, not being able to see IP is a very good sign.
I even performed a Torrent leak VPN test and ExpressVPN cleared that too without any hiccups.
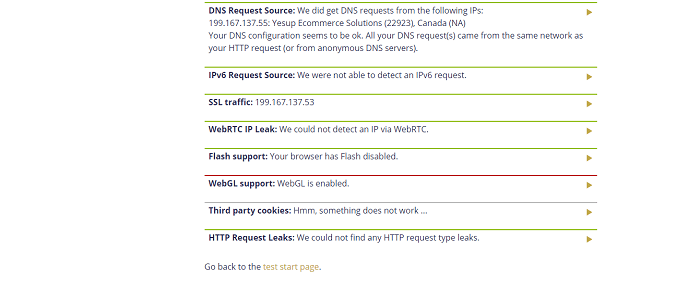
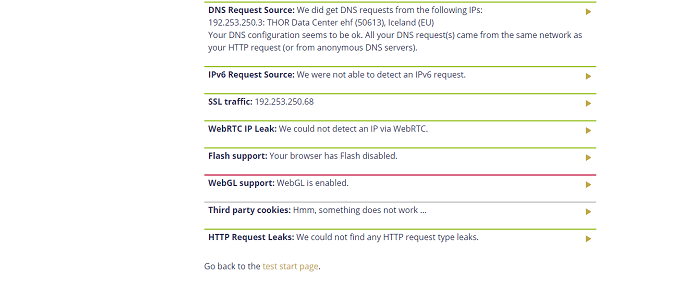
Performing the same leak test on Doileak.com, and I didn’t encounter any leaks with ExpressVPN enabled.
2. NordVPN – PASSED
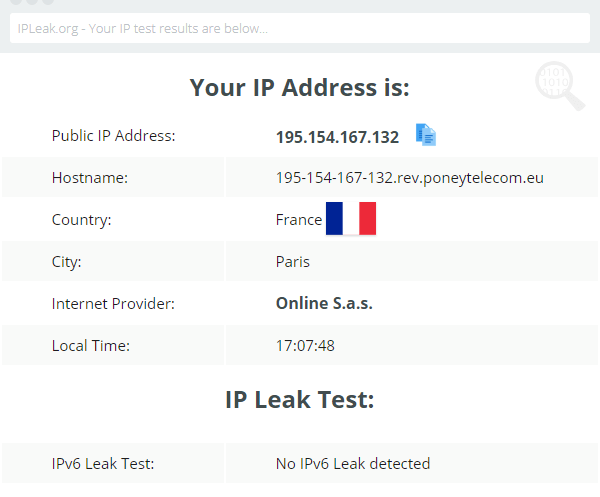
Testing Server: France
Next, I tested NordVPN. For this VPN test, I connected to one of their servers in France. In my test, NordVPN did not leak my true IP.
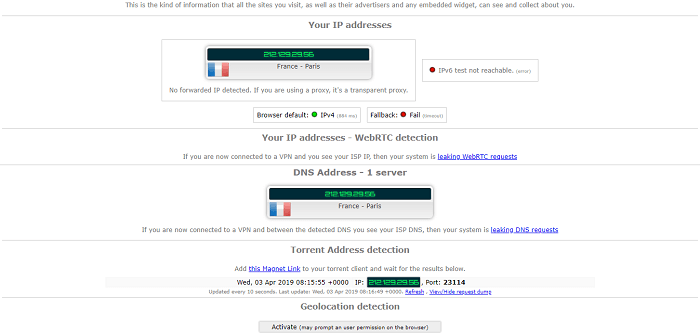
NordVPN also passed DNS, WebRTC, and Torrent leak test without any issues on both IPleak.net and Doileak.com.
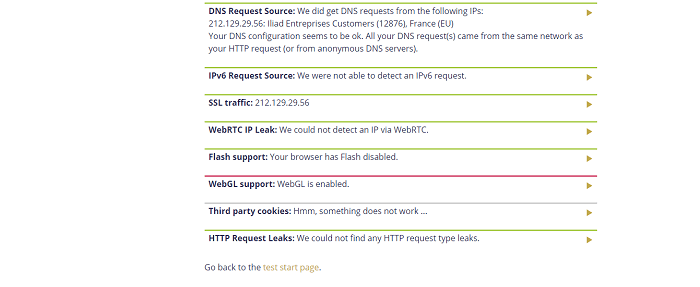
3. Surfshark – PASSED
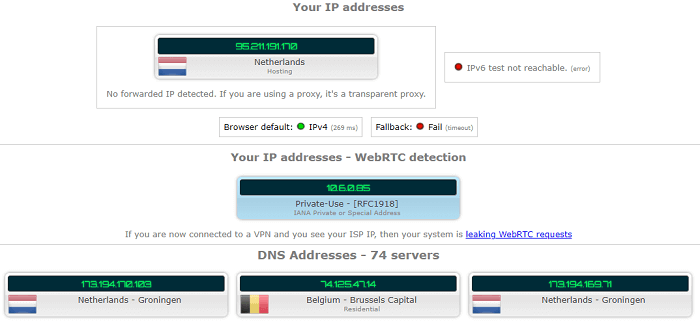
Testing Server: Netherlands
And it was the same story with Surfshark’s test VPN, no IP, DNS, WebRTC or Torrent leaks were detected.

I even tested Surfshark with Doileak.com and there were no leaks detected.
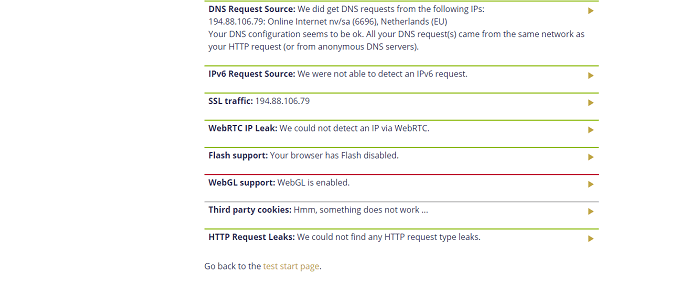
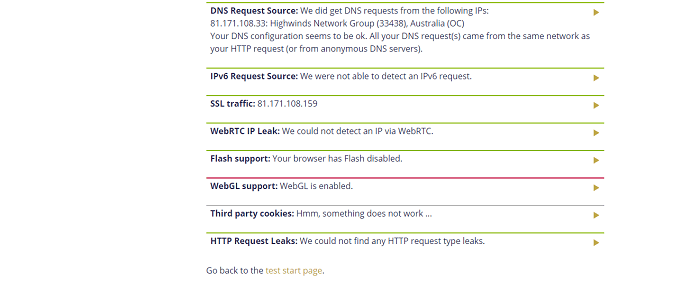
4. IPVanish – PASSED
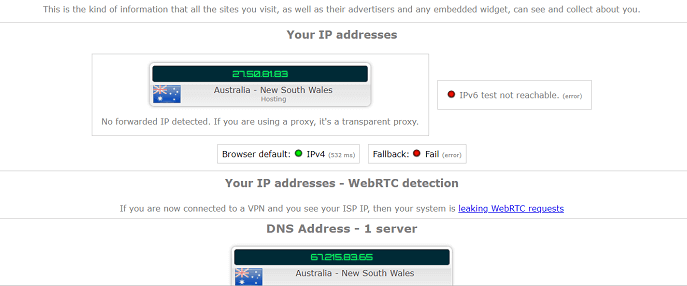
Testing Server: Australia
IPVanish did not leak either.
I connected to the Australian server of IPVanish for testing and sure enough, IPleak.net confirmed that I was, in fact, using the Australian server during my VPN test.
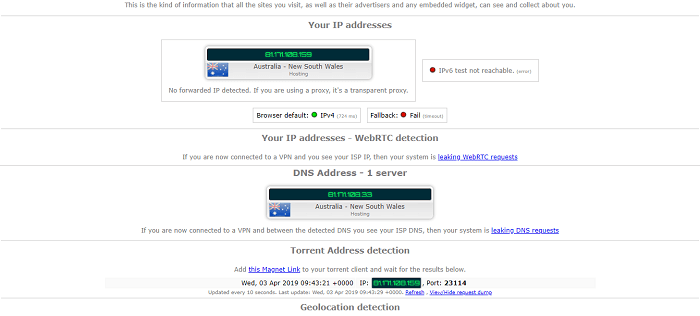
My WebRTC was not visible and my Torrent IP was the same as the IP of the VPN server I was connected to.
Although my DNS address was different from my IP address, it still did not reveal my actual IP.
Safe and secure.
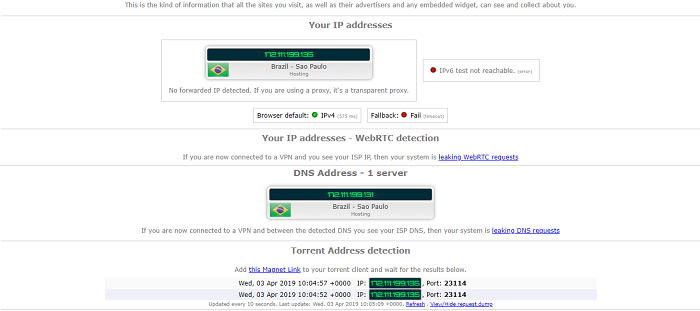
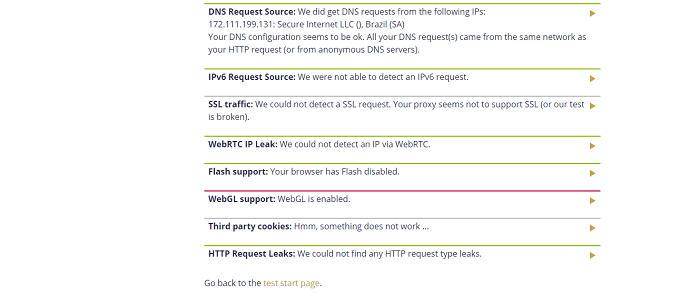
5. Ivacy – PASSED
Testing Server: Brazil
Although Ivacy is a relatively small provider, it still didn’t leak my actual IP. I must say, it took me by surprise. It is also one of the few VPNs working in Brazil.
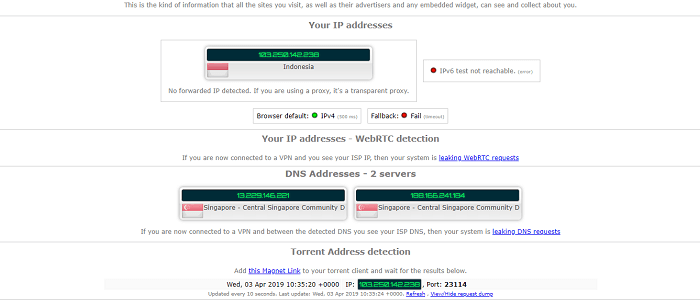
6. VyprVPN – PASSED
Testing Server: Indonesia
Further down on this list, we have VyprVPN. This is another test VPN that I thought for sure would leak during my VPN test but actually didn’t.
7. StrongVPN – PASSED
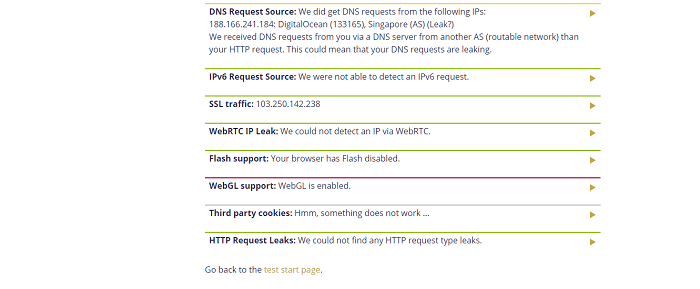
Testing Server: Poland
Another lesser-known VPN that passed my VPN test was StrongVPN. Not only did it not leak my IP address, but it also managed to pass the WebRTC leak test.
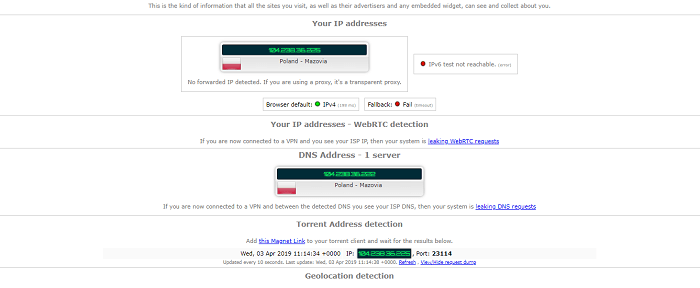
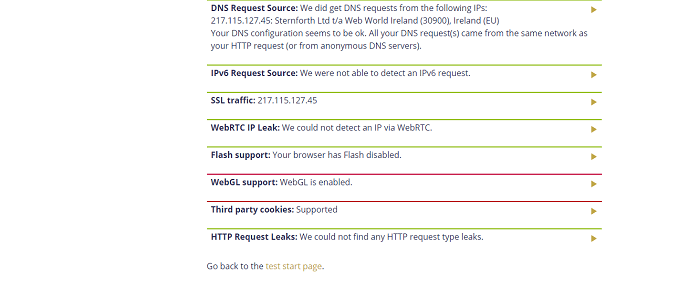
8. TunnelBear – PASSED
Testing Server: Ireland
Leaks are something you normally expect from free providers. With that in mind, I performed the leak test with TunnelBear.
Surprisingly enough, TunnelBear did not leak. I wish other free VPNs (ehm, ehm Hola VPN) would learn from TunnelBear.
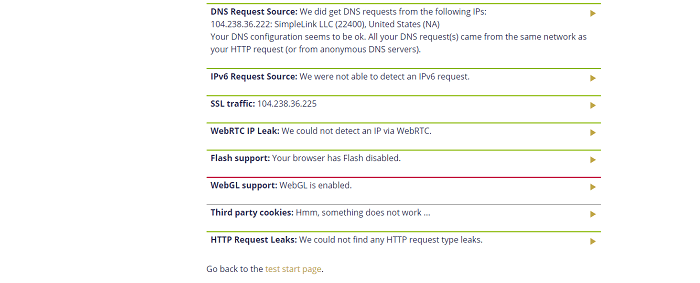
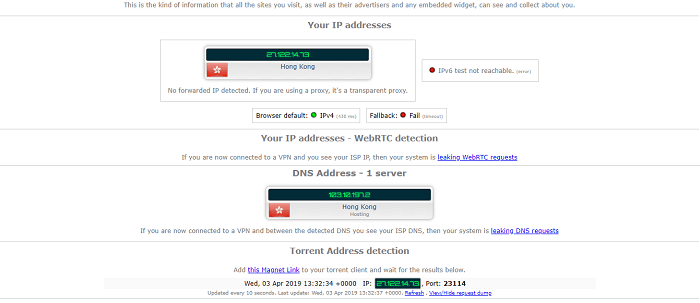
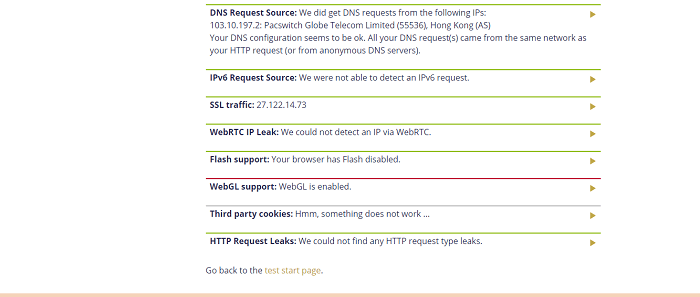
9. Windscribe – PASSED
Testing Server: Hong Kong
Another VPN that didn’t leak in this list is Windscribe. WebRTC leak was nowhere to be found and so was my IP, DNS and torrent IP.
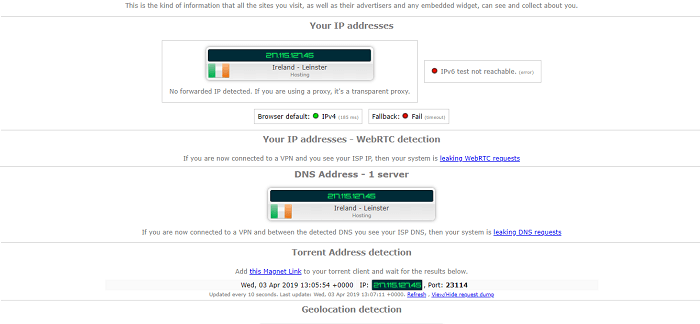
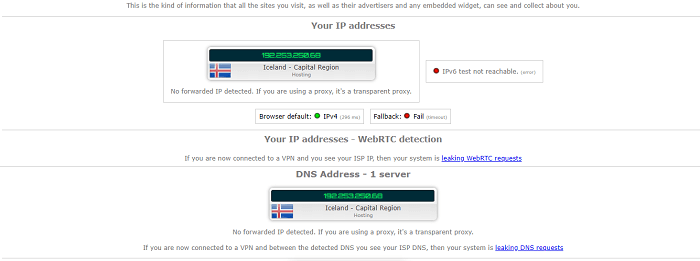
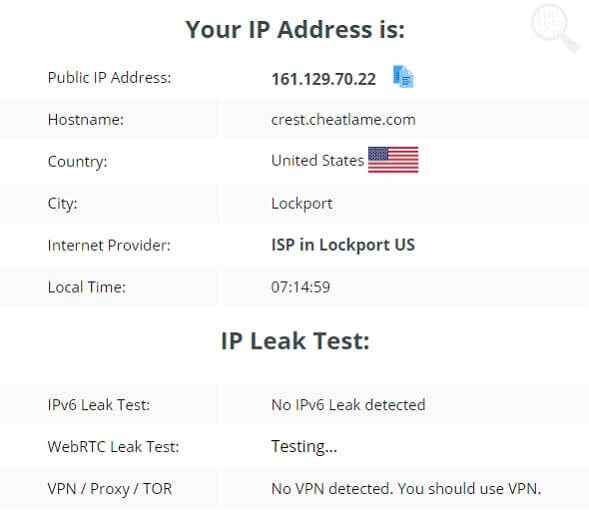
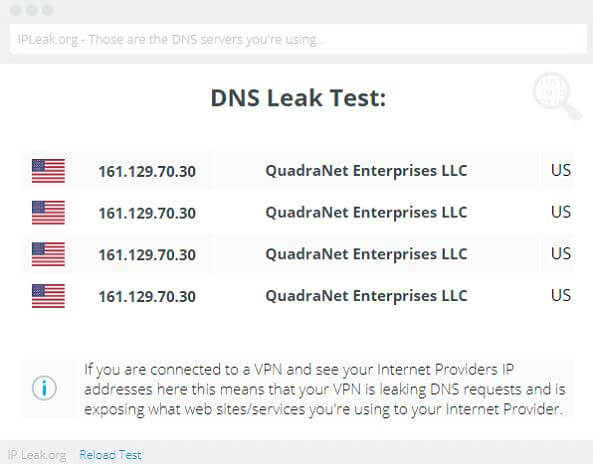
10. PureVPN – PASSED
Testing Server: Iceland
PureVPN also passed the test without any issues. It did not leak my true IP, nor did it suffer from WebRTC, DNS or Torrent IP leak.
11. Private Internet Access – PASSED
Testing Server: Australia

12. VPN Unlimited – PASSED
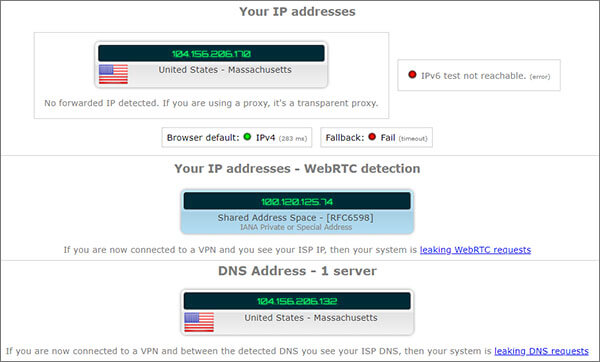
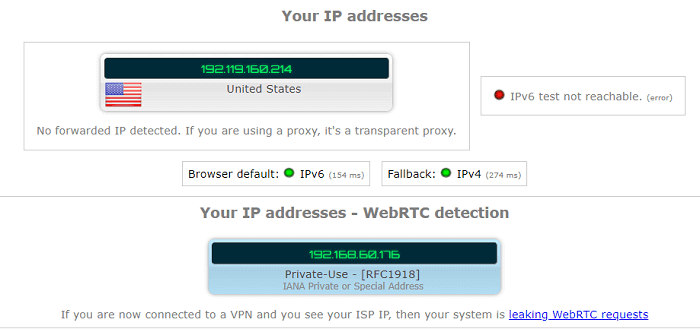
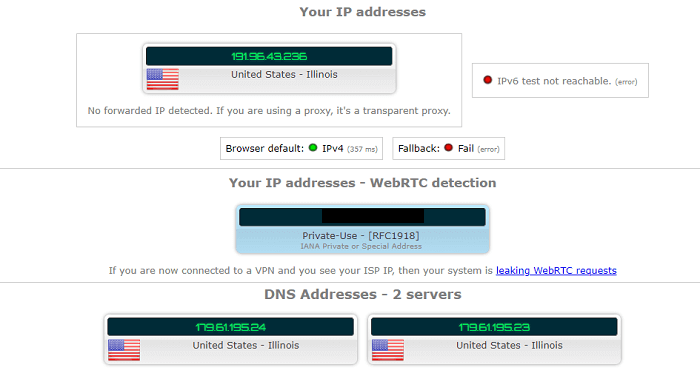
Testing Server: USA

13. AVG Secure VPN – PASSED
Testing Server: USA
14. Betternet – PASSED
Testing Server: USA
Although it seems like Betternet is leaking WebRTC from the VPN leak test, however, since it’s not displaying my actual IP, it’s not suffering from leaks.
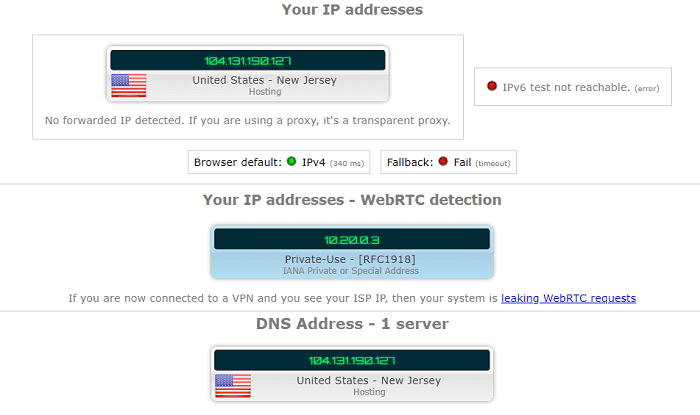
15. VPNSecure – PASSED
Testing Server: USA
16. KeepSolid Business VPN– PASSED
Testing Server: USA
KeepSolid managed to pass my VPN leak test without a problem. For this VPN I used three different tools just to see if it’ll trigger a leak.
17. Connecto VPN– PASSED
Testing Server: USA

18. Tunnello VPN– PASSED
Testing Server: USA
19. Confirmed VPN– PASSED
Testing Server: USA
20. Hotspot Shield– PASSED
Testing Server: USA

21. Proton VPN– PASSED
Testing Server: USA

22. Trust.Zone– PASSED
Testing Server: South Africa

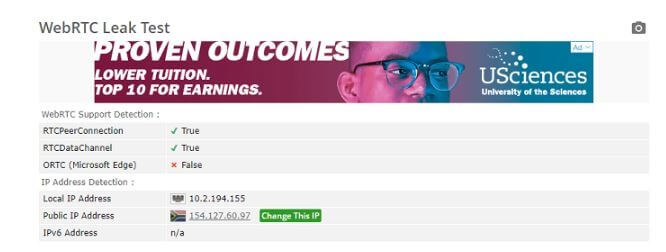
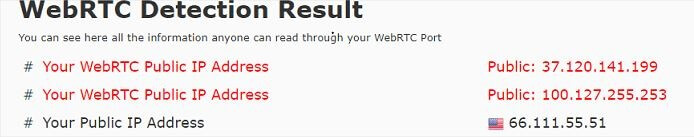
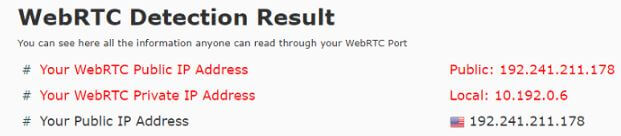
Although the WebRTC test is visibly showing local IP and public IP address, it is not my true IP. Long story short, Trust.Zone also passed my VPN leak test without a hitch.
23. Cactus VPN– PASSED
Testing Server: USA

24. Psiphon VPN– PASSED
Testing Server: USA

25. Turbo VPN– PASSED
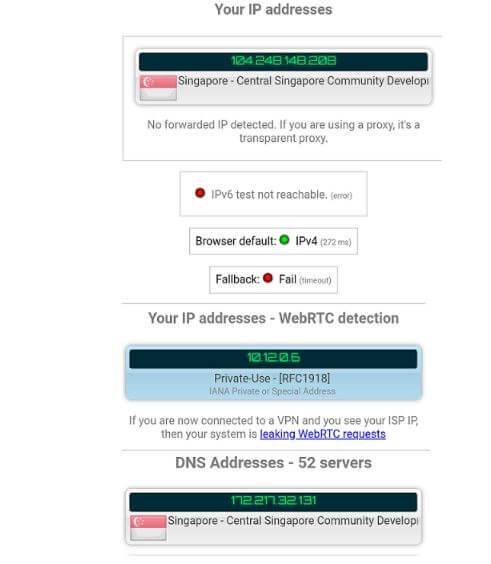
Testing Server: Singapore
26. Hide My IP VPN– PASSED
Testing Server: USA



27. Avast SecureLine– PASSED
Testing Server: USA
28. VPNBook– PASSED
Testing Server: USA
29. VPNGate– PASSED
Testing Server: Japan
30. Opera VPN– PASSED
Testing Server: USA
31. SurfEasy VPN– PASSED
Testing Server: USA
32. Mullvad VPN– PASSED
Testing Server: Sweden
33. F-Secure Freedome VPN– PASSED
Testing Server: Singapore

34. B.VPN – PASSED
Testing Server: Australia
35. VPN Traffic – PASSED
Testing Server: France
36. IPinator VPN– PASSED
Testing Server: USA

37. Blockless VPN– PASSED
Testing Server: USA

38. Security Kiss VPN– PASSED
Testing Server: USA
39. Seed4.Me VPN– PASSED
Testing Server: USA
40. HideIPVPN– PASSED
Testing Server: Netherlands
41. Unblock VPN– PASSED
Testing Server: Germany
42. PerfectVPN– PASSED
Testing Server: USA
VPNs That Do Leak
Not all VPN providers are leak-free and can get you into trouble. Here are 10 services that I found to be leaking IP/DNS during testing:
- Hola
- Hoxx VPN
- Touch VPN
- BTGuard
- Ace VPN
- SecureVPN
- VPN.ht
- Speedify
- DotVPN
- AzireVPN
How to test a VPN for Leaks?
Now that you know which VPN providers to trust and which to avoid, how can a novice VPN user like you and me check for leaks?
To be honest, identifying VPN leaks is a fairly simple affair, however, you do need to be both persistent and vigilant about it. There are plenty of online tools you can use to look for leaks yourself.
However, what’s not so simple is actually fixing, or should I say patching VPN leaks. Don’t worry though, I’ll be sure to make it super simple for you.
Anyways, here’s how to test your vpn for leaks:
1) Start by identifying your local IP address
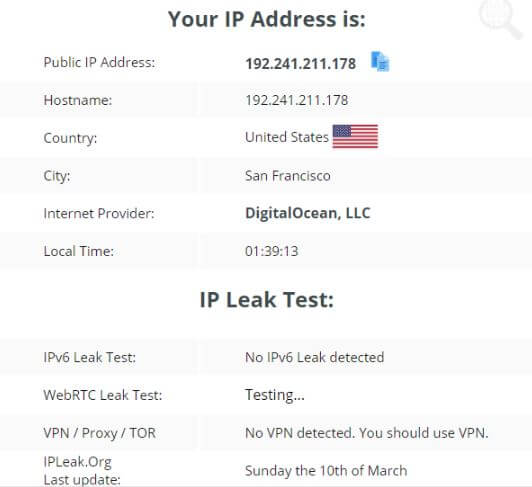
First things first, you need to look for the local IP address of your internet connection. This IP address is assigned to you by your ISP. You must check your IP without connecting to the VPN.
To look for your public IP address, aka your original IP address, you can use websites like WhatIsMyIP.com. Note this IP down as this is the IP address you don’t want your VPN leaking.
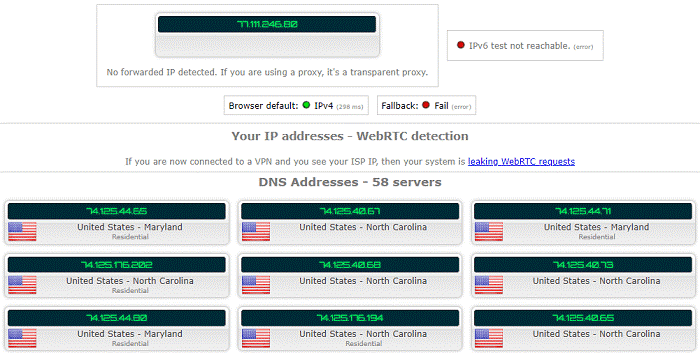
2) Next, perform a baseline test
Now you must perform a baseline test. This is to verify that the test tool is even working properly or not.
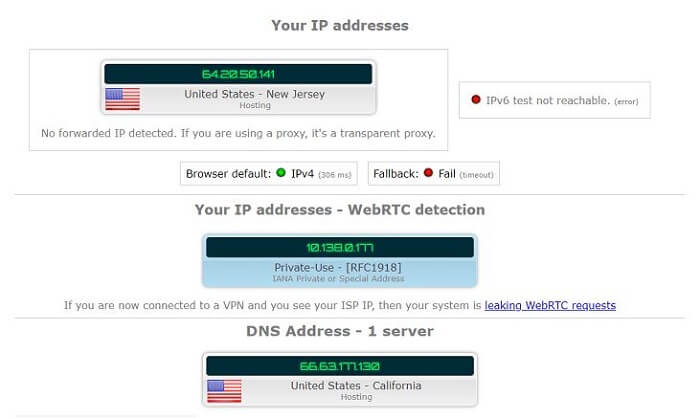
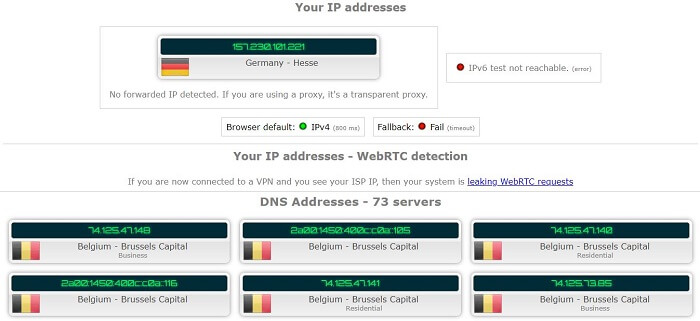
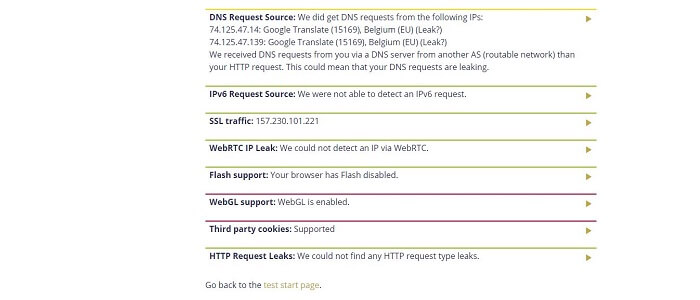
Now with your VPN still disconnected, head over to IPLeak.net. You don’t need to use multiple tools since IPLeak.net combined checks for IP, WebRTC and DNS leaks against your internet connection.
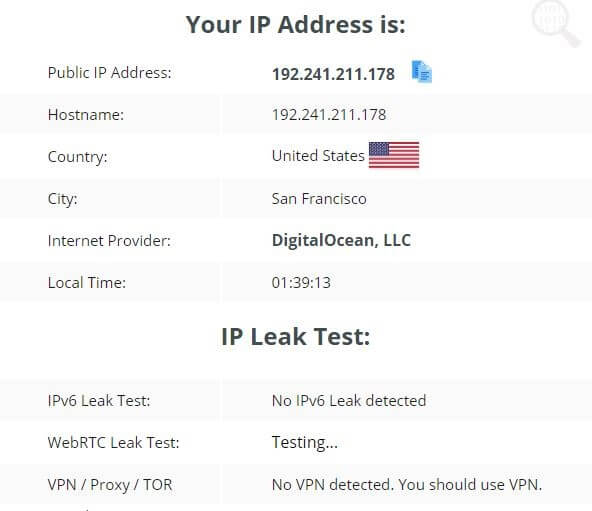
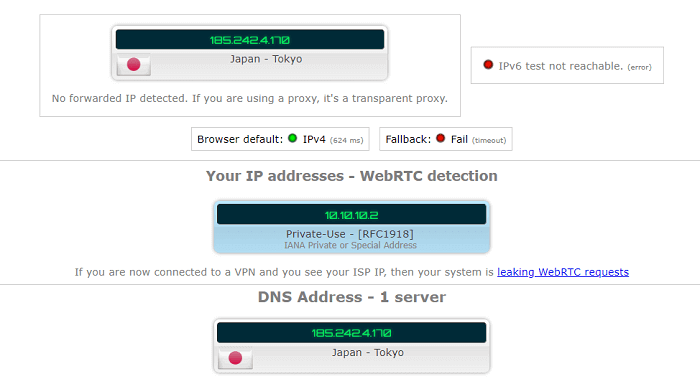
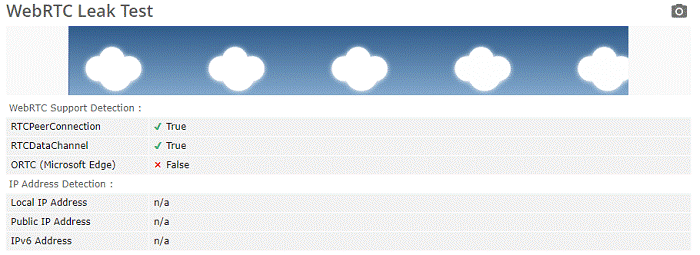
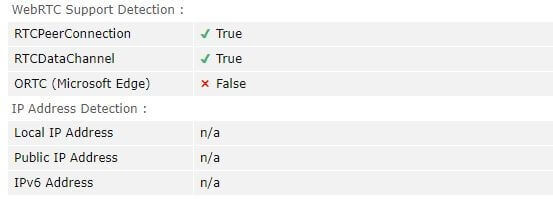
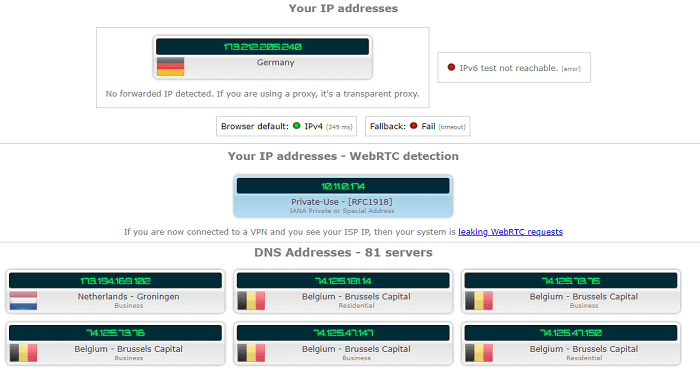
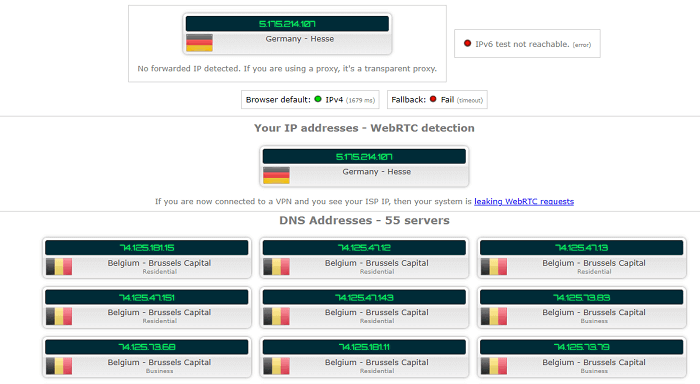
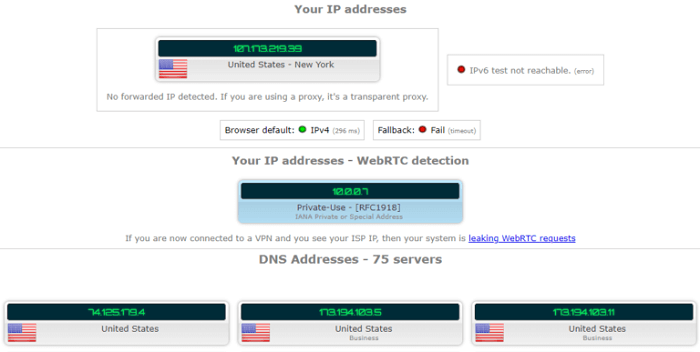
Here’s how the test results should look like:
As you can see, the above screenshot is showing my IP address as well as the DNS servers I’m using. The test is also showing that my browser is, in fact, suffering from a WebRTC leak.
So now that you have basic reading, you can proceed to the real test.
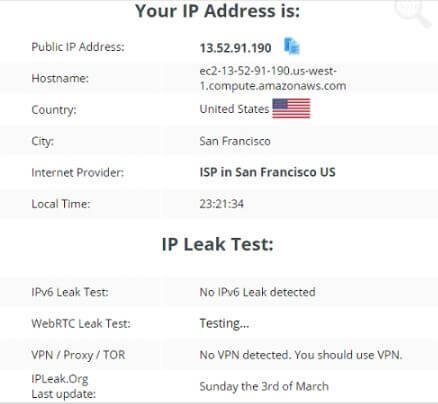
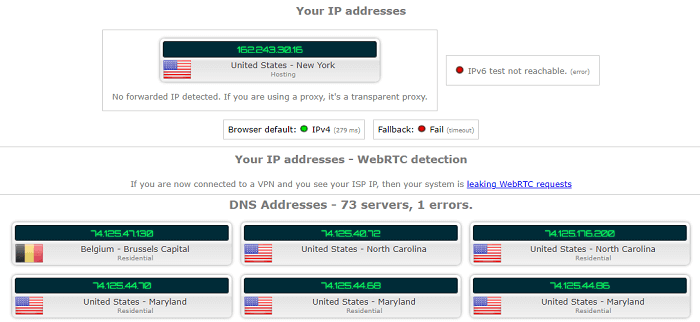
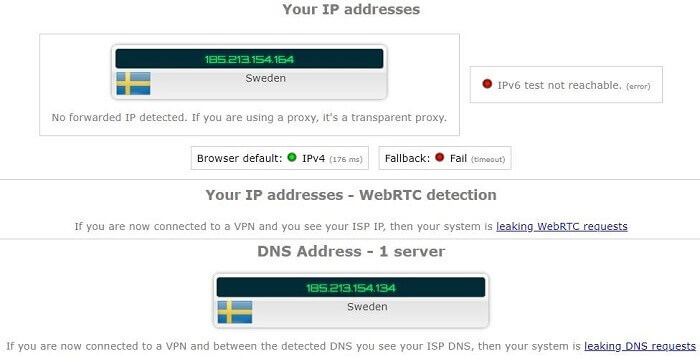
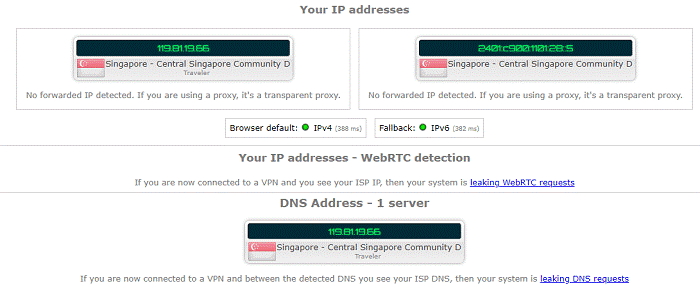
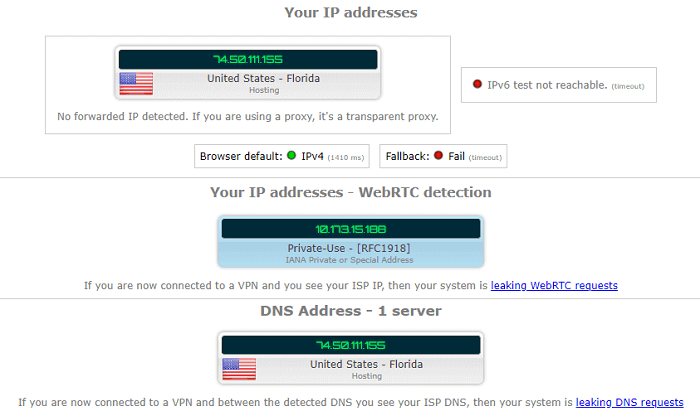
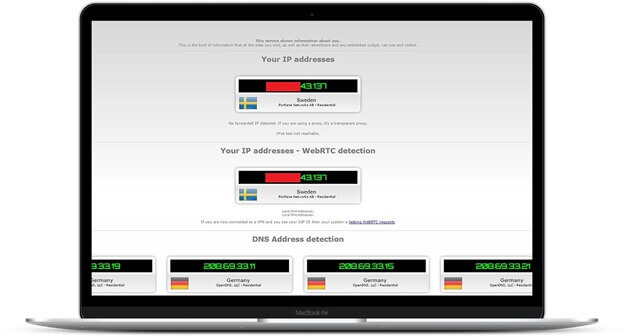
3) Connect your VPN and perform the test again
Now you need to enable your VPN connection and hook up to a VPN server of your choice. Once you’re done with the prerequisites, you need to perform the test once more.
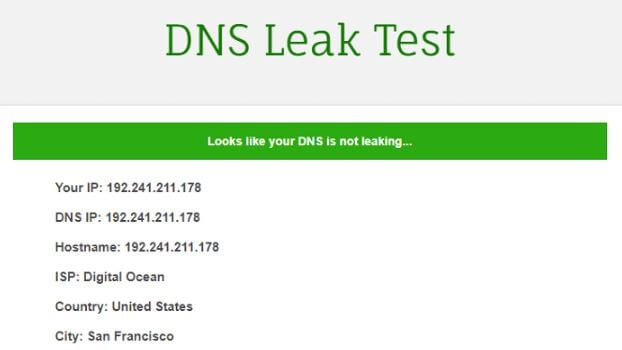
Just like before, head over to IPleak.net and run the test. If you’re using a reliable VPN with leak protection, your results shouldn’t disclose your original IP.
More specifically, you shouldn’t see your original IP at the top of the page, in the WebRTC section and you definitely shouldn’t see your IP in the DNS address section.
Another Way to Check for Leaks
Although IPleak.net and other such tools are enough to check if your VPN is leaking, these tools might not be sufficient for some users since it requires sending DNS requests to checker tools.
Since you send a request with your actual IP address at least once to checker tool servers, your IP might get logged. However, I’m just speculating this and theirs is no actual proof of it.
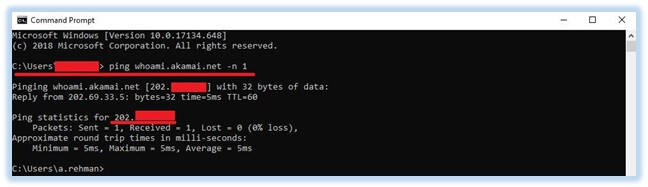
Anyways, if you’re paranoid like me, you can use the command prompt to alternatively test VPN security. Here’s how you can do it yourself:
1) Open up the command prompt on your Windows computer and enter the test server address you trust. If you don’t know any servers, you can use the following:
- akamai.net
- dnscrypt.org
- fluffcomputing.com
- ultradns.net
2) In the command prompt, type in ping [server name] -n 1. If it’s not obvious enough, replace the server name with one of the above-mentioned servers. For example, “ping whoami.akamai.net -n 1”.
After you’ve run the command, you need to make sure you’re not seeing actual IP in the results. If that is, unfortunately, the case, you my friend have got yourself a leaking VPN.
Here’s how the VPN tester results should look like:
How to Fix VPN Leaks?
Now you can’t go about and fix every vulnerability that VPNs suffer from, however, you can patch IP, WebRTC and DNS leaks quite easily.
Here’s how you can make sure your VPN is not suffering from leaks…
1) Get a reliable VPN
The first and easiest option you have is to opt for VPN services with built-in leak protection. NordVPN and ExpressVPN both claim to offer leak protection. As I mentioned earlier, leak protection keeps everything within the encrypted tunnel.
2) Get rid of WebRTC
Since most modern browsers have WebRTC pre-enabled, it can be the source of your leaking IP.
What’s worse?
While you can disable WebRTC in browsers like FireFox, you can’t do it in Google Chrome. Since there’s no in-app way to disable WebRTC in Chrome and Opera, you have to rely on third-party plugins.
Disable WebRTC in FireFox
Disabling WebRTC in your FireFox browser is super easy. Since there is an in-app solution to disable WebRTC, you just need to access the right setting to get rid of it.
Here’s how to do it…
Head over to the address bar and type in about:config. Once you hit enter, you should see a warning message.
Don’t be scared though, just click on the “I accept the risk!” button and you’re halfway there. Now in the search bar, type in “media.peerconnection.enabled” and change the value of the setting that appears to False.
This is how you can completely disable WebRTC in Firefox.
Disable WebRTC in Chrome & Opera
Disabling WebRTC in Chrome and Opera isn’t all that easy when compared to FireFox. As I mentioned earlier, you would have to rely on third-party add-ons.
However, do note that Plug-ins are not completely effective. By that I mean in some circumstances, your browser might still leak.
Here are some browser plugins you can check out on Chrome store or Opera Add-ons page.
That being said since Chrome and other Google products can be a major pain in the neck when it comes to privacy, I suggest you give a try.
3) Fix your leaking IP
Fixing IP leaks can be quite inconvenient for the most part. However, if you’re lucky, you can just mess around with a couple of settings in the VPN app to patch both DNS and IPv6 leaks.

In case your VPN app doesn’t support such customizations, you’ll have to manually disable both DNS and IPV6 settings on your desired device.
For demonstration purposes, I’m going to show you how you can disable DNS and IPV6 settings on your Windows machine.
The reason why I choose Windows is because it’s the most widely used platform, and also because it’s so god damn leaky.
As I mentioned earlier, Windows handles DNS requests very poorly. Even with VPN turned on, you might still encounter leaks.
On that note, let’s start by disabling Smart Multi-Homed Named Resolution feature from the Group Policy Editor.
Disable Smart Multi-Homed Named Resolution
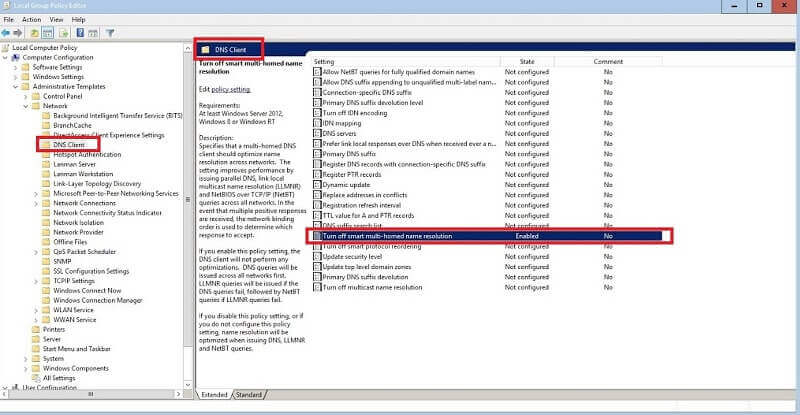
1) Start by heading over to Group Policy Editor. To do so, press Windows + R and type in “gpedit.msc”
2) Next, navigate to Administrative Templates > Network > DNS-Client and look for “Turn off smart multi-homed name resolution”.
3) Now double click on the setting, click “Enable” and then press the “OK” button
That’s it, you’ve just successfully disabled the pesky Smart Multi-Homed Named Resolution feature.
Manually set DNS servers
The second option you have to fix leaking DNS on your Windows machine is to manually configure your desired DNS servers. This is obviously a much easier option than the one I showed you earlier.
To do that, you need to head over to the “Network Connections” setting on your windows computer. Just follow the steps below and you should be done in no time.
1) Head over to Control Panel > Network and Internet > Network Connections and right click the network adapter you wish to change the settings for. For instance, I’m going to alter the settings for Astrill VPN.
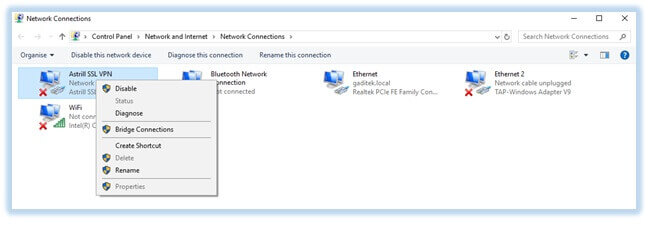
2) Now click on the properties option to pull up Ethernet properties.

3) Next, uncheck “Internet Protocol Version 6”, for every adapter you might have to protect prevent IPv6 from leaking.
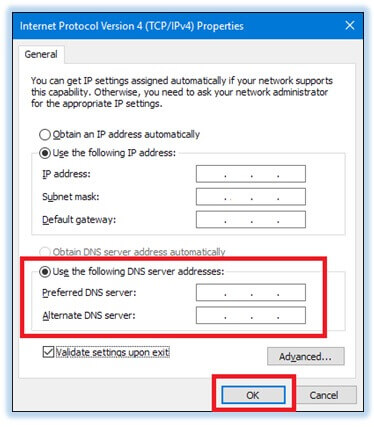
4) When you’re done with that, select “Internet Protocol Version 4” and click on the “Properties” button.
5) Now from the properties menu, select “Use the following DNS server addresses” and enter the exact DNS server address of your VPN provider as the preferred and the alternate DNS server. If your VPN provider doesn’t offer their own DNS server address, you can just use public DNS servers.
Wrapping up!
Although I don’t enjoy name shaming VPN services, however, with a growing number of privacy concerns, disclosing leaking VPNs is an actual need.
Because let’s face it, no one enjoys playing Sherlock on their own internet connection. And it certainly doesn’t hurt to carry out a preliminary VPN Security test.
Rather than blindly using it, test your VPN for any lacking and run it through a basic VPN leak test.
With that being said, I’ve done all the leg work for you, so you don’t have to perform the cumbersome VPN test yourself.
You’re welcome.






