 This article has been reviewed by Professor Arthur Cockfield of Queen’s University Faculty of Law. He is a tax law scholar and policy consultant having expertise in Law and Technology, Privacy law and Tax law.”
This article has been reviewed by Professor Arthur Cockfield of Queen’s University Faculty of Law. He is a tax law scholar and policy consultant having expertise in Law and Technology, Privacy law and Tax law.”
Life is full of deceptions. Things advertised online, aren’t always what you actually get.
Hate to spoil your mood, but that super delicious ice-cream ad you saw online, is just food coloring and tasteless mashed potatoes.
While it’s relatively easy to spot fake ads, sometimes marketers can use a little bit of finesse to bamboozle you.
This is also true for the VPN industry. Believe it or not, after “no logs”, “VPN servers” are the most overly hyped and exaggerated feature of VPNs.
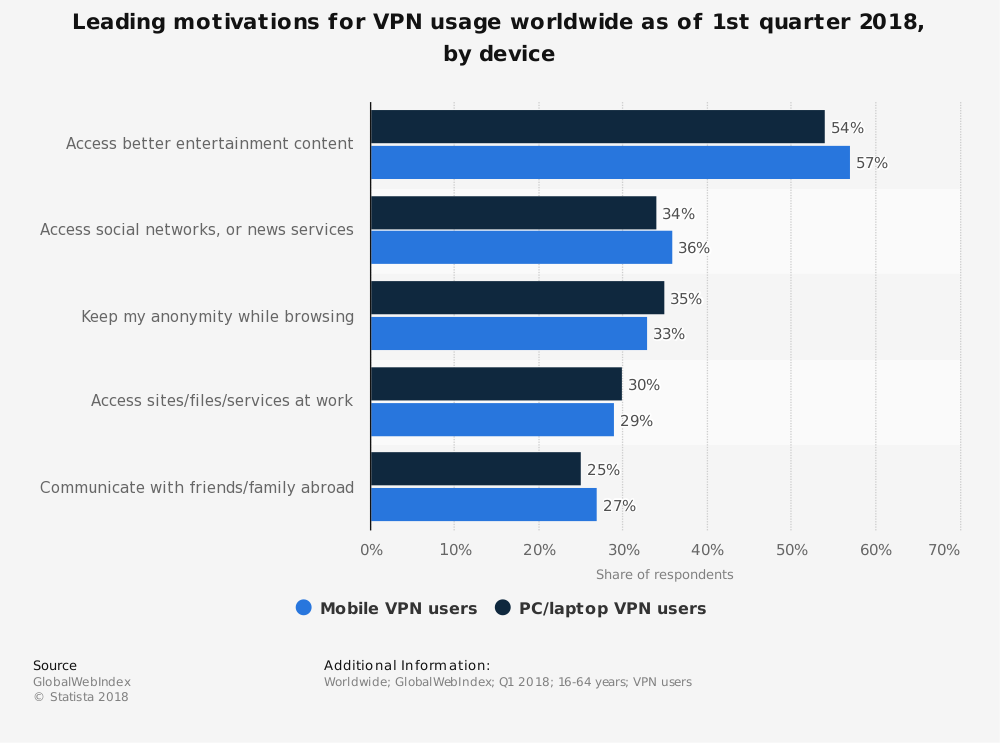
According to Statista, the leading motivation to use a VPN is to access better entertainment content on the internet (54% on PC and 57% on mobile). And the only way to do that is through VPN servers.
Even though it is nearly impossible for VPN providers to offer thousands of bare metal (physical) servers, some VPN providers actually claim that they don’t use virtual VPN server locations.
On that note, in this article, we’ll take a look at a few examples of best VPN services that are either completely transparent about their VPN server locations or lie about using virtual servers.
Difference between Virtual and Physical Servers
Physical servers – As the name suggests, a physical server is an actual physical computer. Think of it like a desktop computer capable of running operating systems like Windows or Linux.
Physical servers are normally, much larger in size than your average desktop computer. Obviously with larger size comes greater power as well.
On the surface, physical servers look like a jacked up version of your average desktop computer.
Since physical servers are quite chunky in size, managing them require a separate server rack. In almost all cases, even a dedicated air-conditioned room is required to host and cool down the massive machine.
In terms of raw power, imagine Jeremy Clarkson (currently The Grand Tour presenter), screaming “power” at the top of his lungs. That’s, what owing physical or bare metal serves to feel like.
Physical servers are comprised of powerful components in general. For resource intensive operations, servers may be fitted with two or more physical CPUs with multiple cores.
Just imagine 20+ cores processing data simultaneously. Data processes like a hot knife through butter. For a VPN service, it’s doesn’t get better than this.
Another reason why physical servers are preferred is because of security. Since physical servers are located in a secure isolated environment, compromising its integrity would require someone actually breaking into the data center.
But perhaps the number one reason why physical servers are preferred over virtual servers is because of their exceptionally low latency.
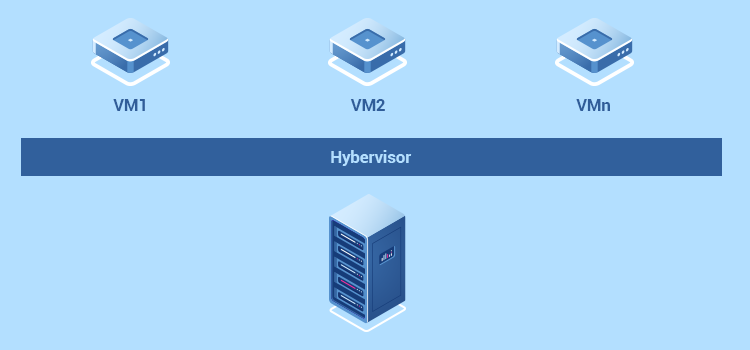
Virtual servers – AKA VPS or a Virtual Machines, on the other hand, are servers within an actual physical server. In other words, a virtual server is a software computer that emulates an actual physical computer.
A virtual server is meant to operate in a multi-tenant environment, meaning that multiple virtual servers can run on the same physical hardware.
Unlike physical servers, virtual servers consume the hardware resources of the actual physical server. This is obviously a more cost-effective option.
If you’re a VPN provider, you’d obviously want to go with virtual VPN server locations instead of physical.
Since it’s possible to configure multiple virtual servers running multiple operating systems on a single physical server, it requires significantly fewer hardware resources.
Although virtual servers are much cheaper to operate, they can be relatively more complex to set up than physical servers. This is why it takes hypervisors such as VMware, vSphere or Microsoft Hyper-V to create and manage VS.
Since hardware resources are shared, virtual servers aren’t ideal for VPN use. In addition to that, as I mentioned earlier, virtual servers suffer from significantly higher pings due to extensive routing which can impact the overall performance of your VPN connection.
What’s the Big Fuss about Using Virtual Servers?
If it’s not obvious by now, virtual VPN server locations can significantly impact the performance of your VPN connection.
But why is that? Let’s dig in a bit deeper and find out.
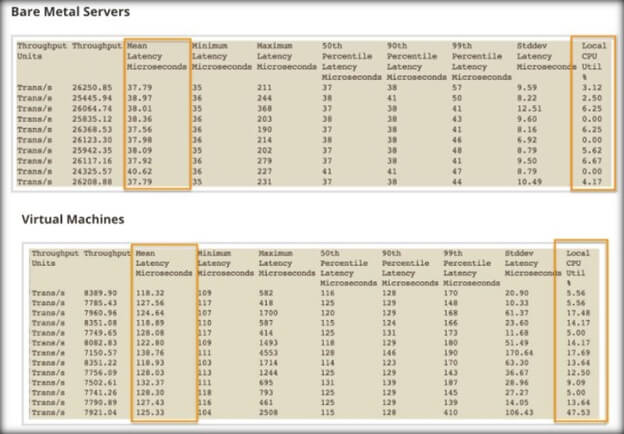
From the image I posted above, it’s clearly obvious that the physical server’s offer significantly lower latency than virtual servers.
But what even is latency?
Well, latency is the time it takes for a packet of data to move from its origin to its destination. Now that you know what latency is, let’s talk about what actually causes latency.
In technical terms, computers send and retrieve data at the speed of light by using “gateway nodes” or more simply, “hops”.
Before I lose you, a hop is considered as the number of devices such as routers, through which the data must pass to get to the source or the destination. Since data doesn’t flow directly over a single wire, the more the number of hops, the greater the latency.
Think of this as the delay caused on the highway due to various diversions or a toll plaza. Higher the number of diversions, the longer it will take to reach your destination.
In networking, the longer the distance between the user and the server hosting the website, the greater the number of nodes or hops between them.
For instance, data traveling from Singapore to the US would take considerably longer than the data traveling from the US to Canada. In the end, it all comes down to hop count.
Now back the question, what’s the big fuss about using virtual servers?
Well for one, since virtual VPN servers are on separate networks, which alone can lead to packet delays.
In addition to that, with virtual VPN servers, there is no way for you to establish a direct connection with the physical hardware due to the hypervisor layer between your VPN app and physical computing resource. This obviously causes higher latency.
Last but not least, since virtual servers are significantly less powerful than physical servers, performance bottlenecks may occur due to the sheer number of users.

But are slower speeds the only thing you should be concerned about when using virtual VPN servers?
Apparently not. Allow me to explain…
You see, VPN providers that offer physical or bare metal servers actually get full control over the acquirer server.
Using physical servers, IT staff can fully customize and configure the server to their specifications and business requirements.
Take for example NordVPN server locations. Since all of their servers are actually physical (yes, I did test them), they can configure their own proprietary Vanilla OS to ensure all of their servers work in accordance with their business guidelines.
Not only that, using only physical servers enables NordVPN to implement powerful obfuscation to bypass even the most robust firewalls.
In comparison, VPN providers offering virtual VPN server locations, cannot independently control their servers or the applications running on them.
In order to provide access to content in a high-risk country, VPN providers route traffic through virtual VPN server locations in other countries. Doing so requires the deployed server to comply with that country’s data retention laws (if any exists).
For instance, if you connect to a Hong Kong server thinking it’s secure and your data actually gets routed through the Canadian VPN server instead, your server would be required to log some data as per the Canadian laws.
However, VPN providers go to great lengths to avoid offering virtual servers in countries falling under the 5, 9 and 14 eyes surveillance alliances. Hence the greater latency.
But what if a VPN provider is offering a virtual server to a safe location yet its data-center is located in a country with strict data retention laws?
Note that sometimes a VPN company may advertise a virtual server that is located within a country that has laws that appear friendly to a user who does not want the government to access their personal information (e.g., log data).
Yet the actual data is stored in a data-center that is based in a country with different laws that may make it easier for third parties to access a user’s personal information.
Under general principles, data protection laws of the country where the data-center is located will govern the collection, use, and disclosure of any user information. In other words, users should be aware that the laws of the data center country will be the ones that normally matter.
In some cases, data protection laws allow for the transfer of personal information to another country for purposes such as storage and processing and indicate the laws of the second country do not apply.
However, even in these cases the company based in the ‘transferring country’ often needs to ensure that the information processor in the ‘transferee country’ is accountable to handle the data in the way mandated by the laws of the transferring country.
Why Do VPN Provider’s Use VPN Server Locations?
Well, it’s simple, to meet the demands of their customers. I mean, if customers want access to a high-risk location, doesn’t it make sense for the VPN provider to give users that access.
While small VPN providers use virtual VPN server locations mainly for the sake of cost-cutting, more mainstream VPN providers like ExpressVPN, use virtual VPN server locations for the sake of fulfilling gaps in their global server coverage.
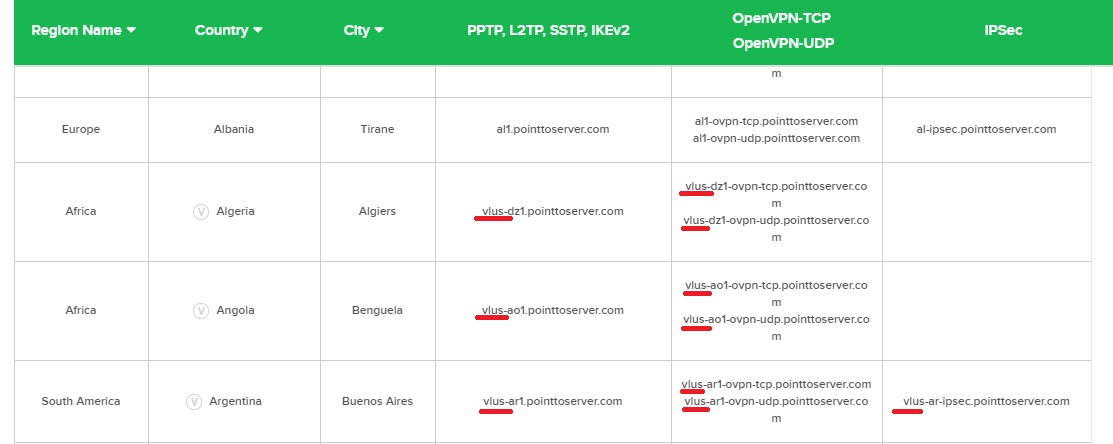
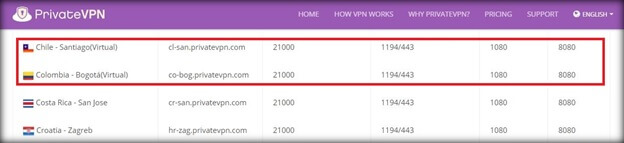
Top VPN providers like Surfshark, PureVPN, and ExpressVPN are completely transparent about using a mix of virtual and physical servers. In fact, PureVPN server locations page explicitly mentions the use of virtual servers.
PureVPN server locations:
Similarly, ExpressVPN also has a separate page listing their virtual servers locations and a brief description of why they use them.
In order to offer access to certain geo-restricted contents, VPN providers don’t have any other choice but to offer virtual VPN server locations in neighboring countries and assigning it an IP of the country in which the content resides.
For instance, according to Express VPN server locations page, “if you choose to use ExpressVPN to connect to Indonesia, your network traffic will be routed through a server in Singapore and assigned an Indonesian IP address so that your traffic appears to come from Indonesia.”
From an end-user perspective, other than probably experiencing higher pings, there is no obvious way to distinguish a virtual VPN server location from a physical one.
It is interesting to note that, at least in theory, VPN companies could be liable to users or subject to a government fine if they mislead consumers by stating they have physical servers when in fact they are using virtual servers.
Many countries have laws that allow consumers to sue companies if these misleading statements cause consumers damages. Also, countries often have laws against false advertising or engaging in deceptive commercial practices that could result in fines or other sanctions for the offending business.
That said, in the next section you follow the steps to see if a VPN provider uses virtual servers or not.
How to test if your VPN uses virtual VPN server locations?
Testing to see if your VPN provider uses virtual VPN servers is fairly easy. All it takes is a couple of tools and a bit of investigative work to roughly find the location of a VPN server.
Feeling pumped? Hold just a minute there Sherlock!
Before you use any tools, the best option for you is to ask the provider directly if they use virtual VPN server locations or not. Whether through email support or live chat support, you’ll easily get a definitive answer right there and then.
For instance, when I started writing this article, I emailed PrivateVPN and asked if they used virtual servers. Here’s what they emailed me back:
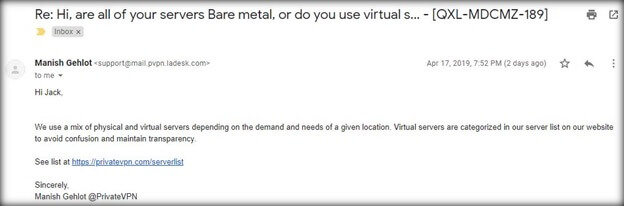
Pro tip: Just mention that you’re a reviewer and want to update your review. That always gets the job done.
But if you don’t get a definitive answer, it’s time to put on your investigation hat and conduct the test yourself.
Here’s what you’ll need:
- The VPN server address of the server you want to perform the test on. You can browse through VPN server lists when you log in to your VPN providers website.
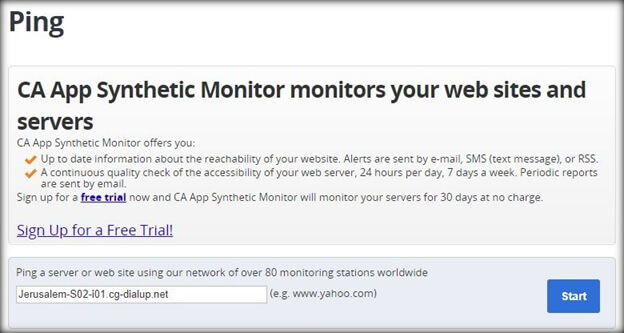
- Ping testing tool like Ca Technologies App Synthetic Monitor or other tools like pe.
- A Traceroute utility. Again you can use App Synthetic Monitor’s Traceroute utility. If you don’t feel like using the online utility, you can even run the tracert command in the Command Prompt.
The above-mentioned tools should give you a rough estimation of whether the VPN server you’re using is physical or not.
However, if you feel like taking your investigation one step further, you can even find out the name and location of the data center hosting the server using the BGP tool kit from Hurricane Electric Internet Services.
Now that you know what you’ll need to perform the test, we can now discuss how to actually conduct it.
Testing virtual and physical VPN servers
So what do I want to cover in this section? Well in addition to showing you how to perform the test, I also want to show you which providers are true to their words.
To do that, I’ve contacted 23 VPN providers and asked them whether they use virtual servers or all of their servers are actually bare metal (physical). I’ve also performed the test using the tools I’ve mentioned above.
Let’s start the test…
PrivateVPN – True to their Claims
Starting off with PrivateVPN and they claim they offer a mix of both physical and virtual servers. It is true, they actually have a dedicated page clearly mentioning and distinguishing both their physical and virtual servers.
However, PrivateVPN actually took me by surprise as the few “virtual” servers that I tested, actually turned out to be physical. I guess they didn’t update their page.
Here’s how I performed the test…
To start off, I selected a virtual server (fr-par2.privatevpn.com) from their VPN server address list. If you’re wondering what is VPN server address, the image below perfectly explains it.

Anyways, I then wanted to ping the server from various locations (countries) to see which location was the closest.
You’ll want to look for the field that has the lowest values, more specifically, you’d want to look for the location with the least round trip time (min. rtt).
If the round trip time is 2 or under, that’s a big indication that the server is actually located in the country where it’s claimed to be.
Since I’m performing the test on the virtual server in France, the server that’s pinging PrivateVPN’s server should show significantly higher rrt.
However, as I said earlier, even their virtual servers are actually physical.
Instead of showing high rrt in France, their virtual server located in France actually showed 1.496 rrt.
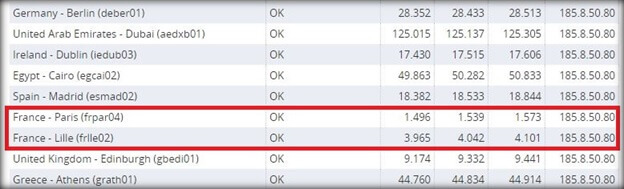
That’s a clear indication that in fact, their virtual server is no longer virtual.
However, in order to cross verify the test, it’s better to run it through the traceroute utility to see if it’s actually a virtual or a physical server.
If you don’t know what the traceroute utility does, it tells you the hop count, IP address of each node and their pings.
To perform the traceroute test, I used the same server address as before (fr-par2.privatevpn.com).
Since we’re cross verifying that the server is indeed located in Paris, France, as evident from the ping test, you’d want to perform the traceroute test from Paris.
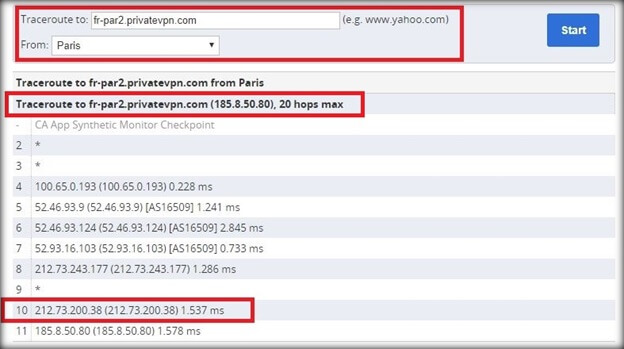
From the test result posted above, you’d want to look at the second last field. Since the ping value is, in fact, similar to the min. rtt value from the ping test, the server is in fact located in Paris France.
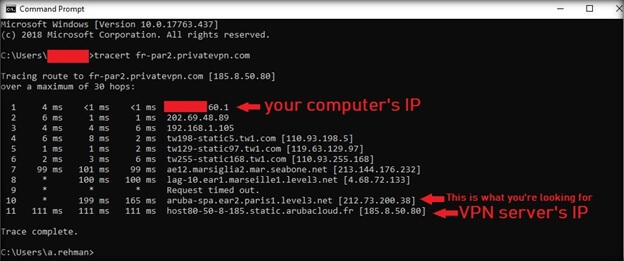
Now, as I mentioned earlier, you can also perform the tracert test using the Command prompt on your Windows computer. However, you can’t perform the traceroute from a specific location. Instead, the cmd will perform the traceroute test from the location of your computer.
Here’s how to do that…
- Open up the command prompt on your Windows computer by hitting the Windows key and typing in “cmd”.
- On the command prompt, type “tracert” command along with the server address and hit enter.
Here’s how the test result looks from my computer…
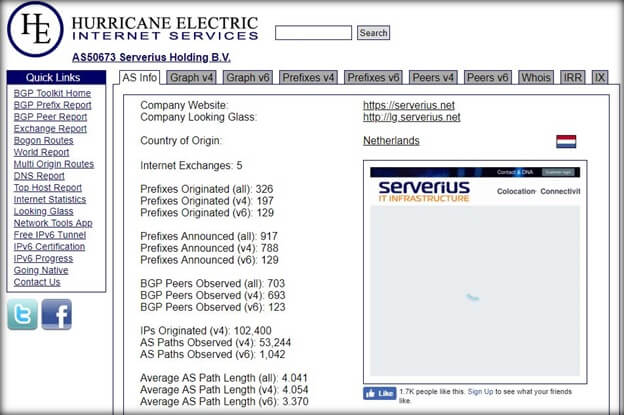
Now that I’ve covered both the ping and traceroute test, there’s one additional thing to cover. I’m talking about finding the data center hosting the VPN server.
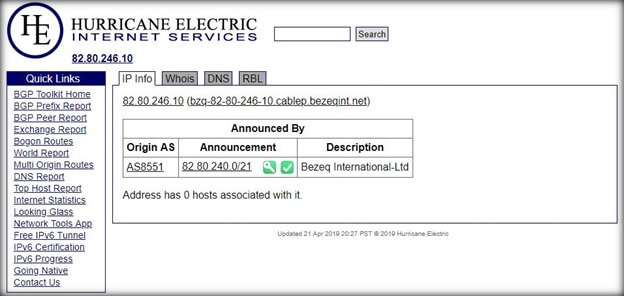
Doing that is fairly simple, you just need to enter the second last IP address from the traceroute test we conducted previously.
Here’s how you can do it yourself:
- Copy the second last IP address from the traceroute test we conducted previously, in this case, it is 212.73.200.38.
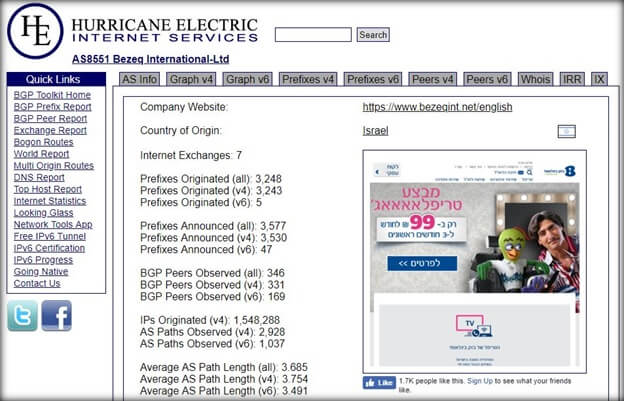
- Now head over to he.net and enter the copied IP address in the field provided and hit search.
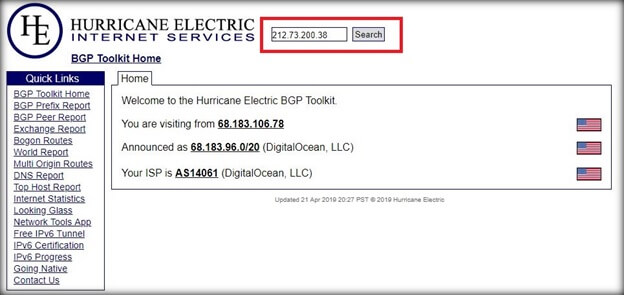
- Now click on where it says “Origin AS” and you should be able to see the name and the country of the data center hosting the VPN server.
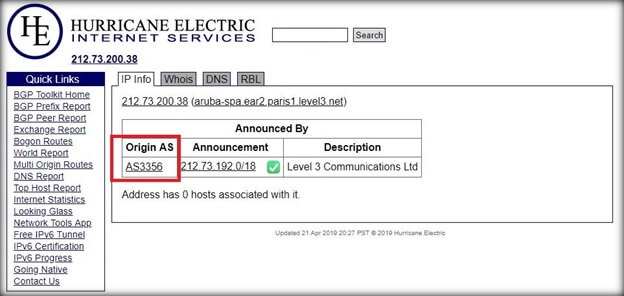
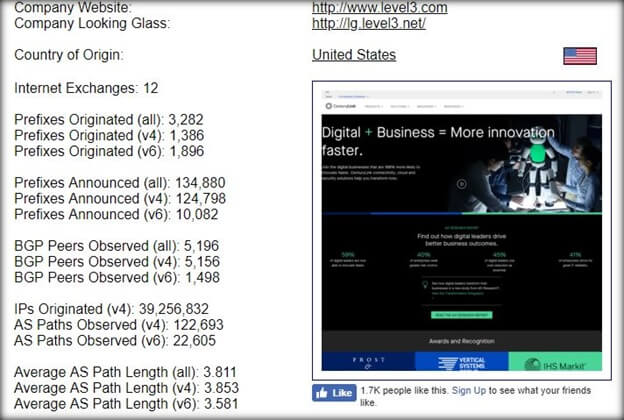
As you can see, the server we just tested is in fact located in France, but it isn’t actually owned by a French data center. It is actually in the US.
But here’s the catch.
Data centers have to comply with laws and regulations of the countries they are based in. So for this particular case, the data center is in the 5 Eyes nation, which means it could lead to privacy concerns.
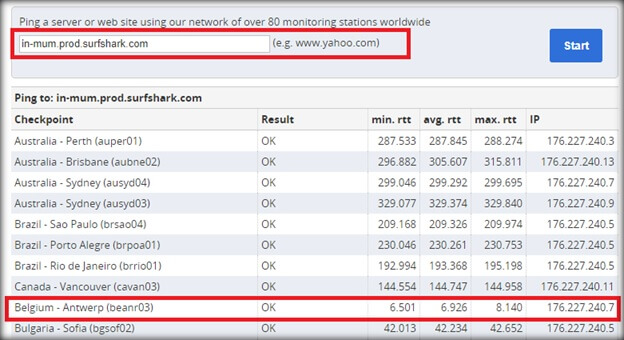
Surfshark – Might be using Virtual Servers
Now Surfshark is an amazing VPN service, in fact, I can personally vouch for how good it is. However, that doesn’t necessarily mean I wouldn’t test it though.
On that note, I began by contacting their chat support (using a pseudo name Jack). The question was simple, do you use virtual servers or all of your server’s bare metal?
In the response, Surfshark told me they only used physical aka bare metal servers as of now, however, they’re planning on introducing virtual servers in the future.
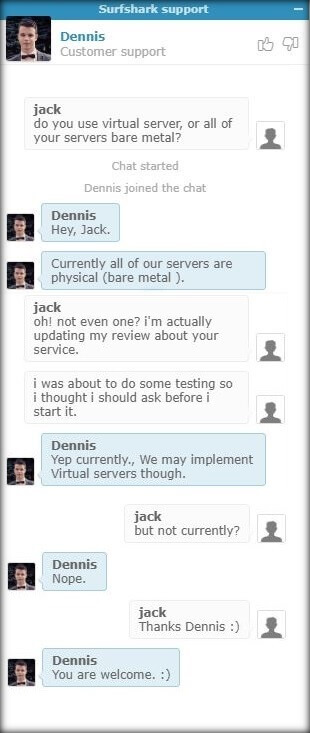
Despite their claim, I still decided to test out some of the more exotic locations offered by Surfshark, so I choose Vietnam.
While their other mainstream locations like the UK, US, Canada, and Australia did pass as actual servers, Vietnam seems to be a virtual server location. At least that’s what my tests showed.
Here’s how I performed the test…
Just like l did with the PrivateVPN, I picked a server to test from Surfshark’s website. In this case, it was the Vietnamese server.

Now I pinged it using the App Synthetic Monitor’s ping testing tool.
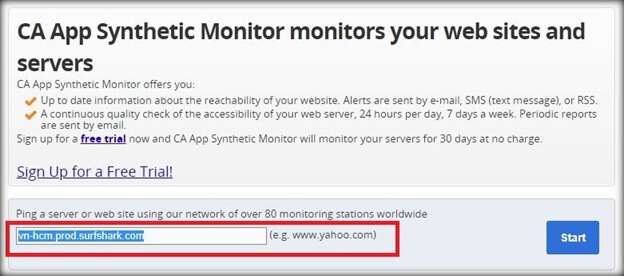
Now if Surfshark’s Vietnamese server is actually physical, it should show a significantly low (min. rtt), however, that was not the case. On the contrary, Surfshark’s Vietnamese server showed a significantly high (min. rtt).
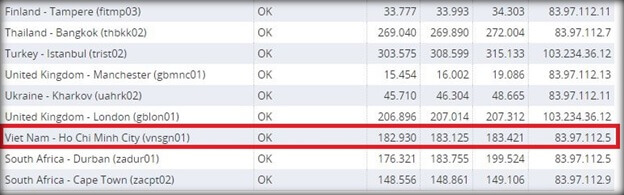
On the other hand, Antwerp, a location in Belgium showed suspiciously low (min. rtt), a clear enough sign that Surfshark’s Vietnamese server might actually be located somewhere near Belgium.
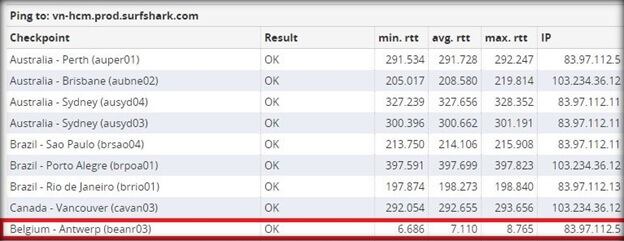
To cross verify my test results, I did run it through the Traceroute test as well. The test results were in fact quite similar, a telltale sign of a virtual server.
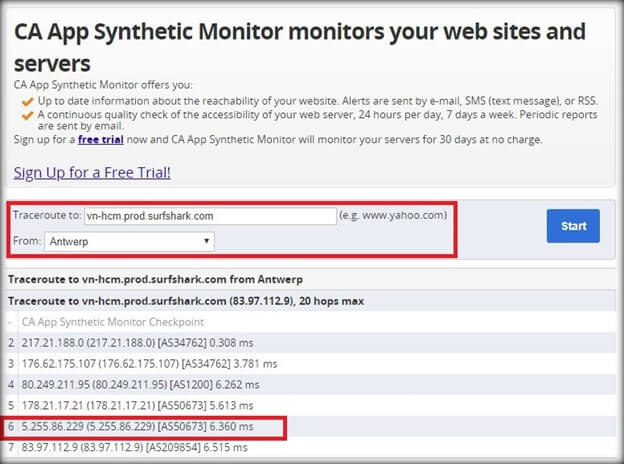
Now bear in mind, the above test results aren’t 100% accurate, but based on my testing, it looks like Surfshark might be offering a virtual server for Vietnam. I mean how else you can explain such a ridiculously low rrt in Belgium.
If my test results are correct, Surfshark is routing their traffic through servers nearest to Belgium and assigning it a Vietnamese IP.
But this isn’t the only server I found to be virtual, in fact, the Indian server of Surfshark seemed like it might be virtual as well.
To keep things concise, I’m posting the test results for the Indian server below.

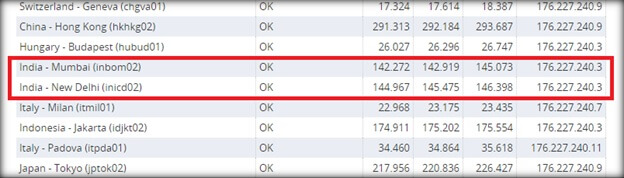
As you can see, both Indian servers pinging the Indian server of Surfshark are showing significantly high (min. rtt).
On the other hand, the Antwerp server located in Belgium showed significantly low (min. rtt).
Similar to their Vietnamese server, Surfshark might be routing their traffic for the Indian server through some server located near Antwerp Belgium.
Digging in a bit deeper and both the Vietnamese and the Indian server of Surfshark are owned by the same data center which is located in the Netherlands.
These were just two locations. There is a possibility that there might be others as well.
CyberGhost – No Virtual Servers in Sight
To test whether CyberGhost VPN server locations, I first contacted their chat support and inquired about it quite casually.
According to CyberGhost, all of their servers are physical and they don’t use any form of virtualization.

For the actual testing part, I choose an Israeli server of CyberGhost. Since this location was kind of exotic, it did had a high probability of being a virtual server. Turns out I was wrong.

Pinging the Israeli server of CyberGhost revealed that they, in fact, weren’t lying about using physical servers.
Their Israeli server is in fact located in Israel – Kiryat-Matalon.
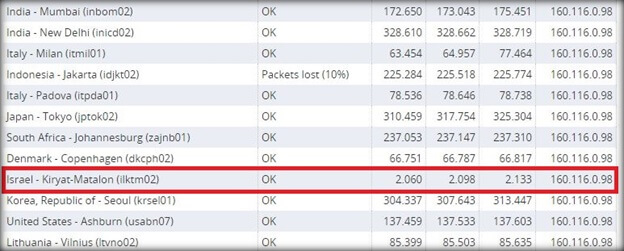
Even running the traceroute tool showed a similar result with an extremely low ping rate from Kiryat-Matalon to Jerusalem.
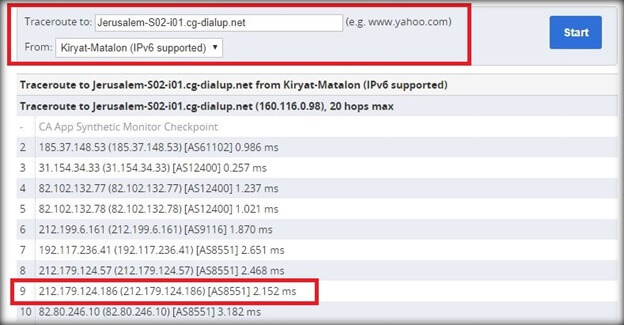
Even the data center hosting the Israeli server of CyberGhost is also located within Israel.
List of VPNs that Disclose or Use Virtual Servers
Below is a list of few VPN providers that use virtual servers. There can be many others, which I will add to this list in the future.
- ExpressVPN
- Ivacy
- PureVPN
- PrivateVPN
- CactusVPN
- GetFlix
- VyprVPN
- Surfshark
Wrapping up!
First the flawed logging policies, than leaks and now the use of virtual servers, it seems like VPN providers love getting themselves tangled in controversy.
Even though there’s isn’t anything technically bad about using virtual servers, some VPN providers are too reluctant to appropriately advertise it on their website.
On the contrary, some providers would even go about and claim that all of their servers are physical. But as we saw with Surfshark, it might not always be true.
Another such example is CactusVPN. Even though they use a combination of virtual and physical servers, they don’t mention it anywhere on their website.
While on the other hand, VPN providers like ExpressVPN, PureVPN, Ivacy, and VyprVPN have clearly mentioned that they use of both virtual and physical servers as necessary.
In all honesty, this topic is quite confusing in nature. However, the only gripe I have is that VPN providers should be more transparent and openly disclose what kind of servers they offer.
 This article has been reviewed by Professor Arthur Cockfield of Queen’s University Faculty of Law. He is a tax law scholar and policy consultant having expertise in Law and Technology, Privacy law and Tax law.”
This article has been reviewed by Professor Arthur Cockfield of Queen’s University Faculty of Law. He is a tax law scholar and policy consultant having expertise in Law and Technology, Privacy law and Tax law.”