Have you ever come across VPN blocks?
Imagine getting your hands on the best VPN before traveling to a highly restrictive like China, only to find out that the service is no longer active in the region. The agony!
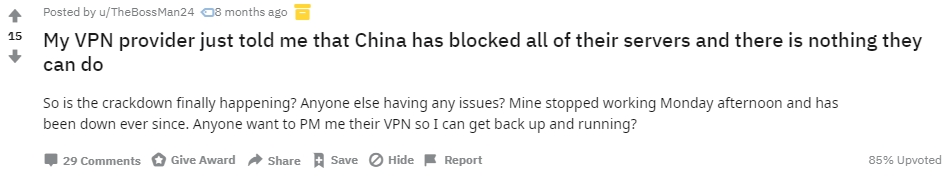
It is not just different governments that block VPNs, there are ISPs, streaming services, schools, universities and other alike that prevent the use of a VPN.
Based on the outcry of various VPN users on different forums, you expect to have unhindered access to any website or service whenever you want.
Sadly that’s not the case.
This is why I am writing this detailed guide about Obfuscation – a technology used by various providers to circumvent the problem of VPN blocks.
As the popular phrase goes “necessity is the mother of invention”, Obfuscation technology is VPN provider’s last hurrah against online censorship.
But what is obfuscation, what countries is it useful for, and how can it help bypass geo-restrictions, that’s exactly what I hope to answer in this short article.
Obfuscation, Powerful or Just Hard To Pronounce?
Obfuscation, although a tongue twister, is a powerful technology, to say the least. Outside the context of VPNs, Obfuscation (OBFU) involves making something difficult to understand.
The role of the obfuscation feature becomes important when we evaluate every VPN service during our unbiased VPN reviews to determine if it includes an obfuscation feature in its arsenal.
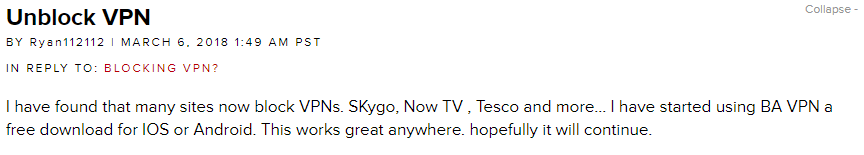
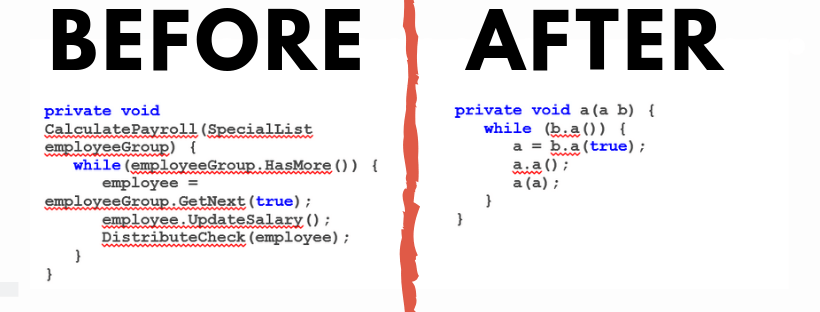
The term ‘Obfuscation’ is commonly used in the realm of computer programming. Developers often obfuscate some or all parts of their code to protect intellectual property.
By restricting reverse engineering in programs, obfuscation makes it impossible for malicious entities to access revealing Metadata.
As powerful as this technique is, it is no short of a double-ended sword. While it empowers programmers to protect their code, it also enables ill intent individuals to obscure malicious code. [Source]
Stepping a bit towards VPNs and, the term obfuscation refers to securing of cryptographic keys from unauthorized entities.
In the context of networking, this terms refers to obscuring an attacked payload from inspection by network protection systems and techniques. [Source]
In less derogative terms, obfuscation takes your data and makes it look like someone spilled spaghetti all over it.
In all seriousness, the obfuscation code is comprised of multilateral techniques that work together to create a layered defense. Some basic examples of obfuscation techniques include:
- Rename Obfuscation
- String Encryption
- Control Flow Obfuscation
- Anti-Tamper
- Anti-Debug
But before I get too technical, here’s how basic obfuscation looks like:
How VPN Obfuscation Works and Why is it Useful?
In the world of VPNs, obfuscation goes by a lot of names. Some providers like to call it stealth while others refer to obfuscation as Camouflage, however, it is essentially the same thing.
Since VPN providers can’t physically place VPN servers in countries with strict internet censorship, VPN providers instead use virtual servers with powerful obfuscation to bypass unreachable firewalls.
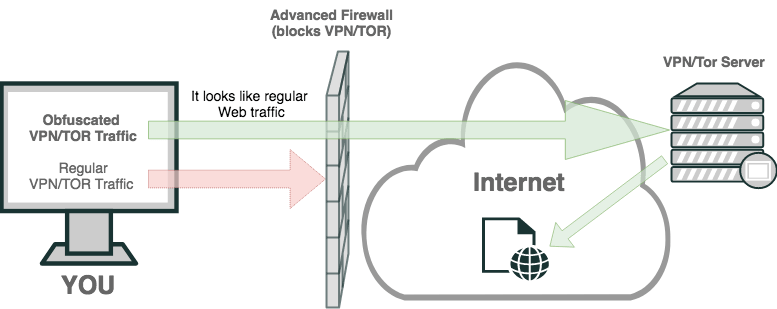
Obfuscation or whatever you want to call it basically disguises data packets passing through the VPN app to look like regular HTTPS traffic.
But why HTTPS and what even is it?
Hypertext Transfer Protocol Secure (HTTPS) is an extension of the Hypertext Transfer Protocol (HTTP). [Source]
If you don’t know what it is, it is used for secure communication over computer networks. It encrypts network communication by utilizing Transport Layer Security.
We use it every day without even batting an eye, yet HTTPS is what ensures no one on the same network gets a hold of our confidential data.
Here’s how a secure website looks like:
Since HTTPS connections are essentially used for transmitting secure information like passwords, credit card numbers, etc., it can bypass most firewalls.
This is what essentially makes VPN obfuscation technology so effective.
Now you might be wondering, why would already encrypted VPN traffic needs to be obfuscated?
Well, as I mentioned earlier since VPNs are restricted by some countries, obfuscating VPN traffic deceives ISP’s or anyone from knowing that your Internet Traffic is encrypted.
Masking your VPN traffic to look like HTTPS traffic using port #443 helps it get past firewalls and access restricted websites.
What can VPN obfuscation be useful for?
For starters, obfuscation allows you to access the VPN service in regions that restrict its use. Obfuscating internet traffic can also be useful for accessing blocked streaming services like Netflix, Hulu, BBC iPlayer and many others.
As most of you might be aware of Netflix’s unfair distribution of shows, some regions get better content than others. Not to mention cheaper pricing plans.
That brings us to another reason why obfuscation is useful and why there is price discrimination. While Netflix costs $7.10 in Australia, it costs a whopping $11.90 in Switzerland.
Same goes for online gaming as well. Let’s say your ISP charges more for gaming and less for general browsing, you could obfuscate your VPN traffic to look like you’re just browsing the web.
Hypothetically speaking!
How VPN Traffic Is Transformed Into Obfuscated Packets
To further elaborate how exactly VPN traffic is transformed into obfuscated packets, take a look at the diagram below:
So now that you have a basic idea of VPN obfuscation, let’s dive in a bit deeper and look at how it works, step by step.
#1 – Basic concept of OpenVPN encrypted data
Although VPNs use multiple protocols, OpenVPN is most widely used. If we talk about OpenVPN, data packets are essentially comprised of two parts, the Header, and the Payload.
The Header
Think of this as an envelope, it contains information such as browser type, language, content type, and so on. The header also includes information that identifies the data packet as OpenVPN traffic. Essentially, it contains information that identifies if the traffic is being routed from a VPN server or not.
The Payload
Think of this as the letter inside the actual envelope. Technically speaking, the payload contains an encrypted data packet. This is essentially what is sent to websites by the VPN server.
#2 – Get rid of VPN Metadata from the header file
Since header files contain the source of the data packets, its content type and so on, if intercepted by DPI (deep packet inspection), it can easily be blocked by the network firewall.
In order to bypass firewalls, VPNs use obfuscation to get rid of VPN Metadata from the header packet. Take away the source and it makes it almost impossible to know that the traffic is coming from a VPN server.
Think of this as de-badging your car. Getting rid of VIN number and all the branding would make terribly difficult to know the actual manufacturer of the car.
#3 – Make your VPN encrypted traffic look like HTTP
So now that the header information has been obfuscated, it’s time to mask the encrypted VPN traffic to look like regular HTTPS encrypted web traffic.
Although the implementation itself is fairly complex, the concept is easy to understand. To disguise the VPN traffic to look like HTTPS traffic, the encrypted VPN traffic needs to be encrypted once again using SSL or TLS protocols.
To jog your memory, both SSL and TLS protocols are used by HTTPS. Since the primary goal of obfuscation is to make VPN traffic look like HTTPS traffic, these protocols do the job quite well.
Anyways, encrypting VPN traffic with SSL and TLS protocols is just one part. To properly obfuscate VPN data packets, the data must be assigned a port number. Since we are using HTTPS, that means we have to assign port #443 to the data packets.
With that taken care of, VPN traffic is pretty much impossible to uniquely distinguish from the rest of the HTTPS data and therefore can’t be blocked by firewalls.
Countries with Restrictive Internet Policies
By now I hope you have a basic understanding of obfuscation and there is no doubt that VPNs are a powerful tool. With military-grade encryption and geo-lock bypassing capabilities, VPNs can evade sophisticated internet censorship.
That is obviously a big NO, NO in the eyes of repressive governments. It is exactly why some countries use sophisticated technology to try and block access to VPN services.
Although demanding and outright difficult to implement, some countries like China and North Korea have blocked all access to overseas IP addresses.
Even though VPNs masks your IP address and routes all traffic through encrypted VPN servers, your VPN traffic can still be blocked.
With powerful technology like Deep packet inspection (DPI), Countries blocking VPNs can identify and can block ports and protocols used by VPN providers. They can even outright block a VPN service if it is prone to leaking.
On the other hand, counties that don’t have sophisticated technology to block VPNs, pass legislation to outlaws VPN services that don’t comply with government regulations.
This obviously is much worse than just blocking VPNs. By deeming VPNs illegal to use in the country, repressive countries use scare tactics to discourage the use of VPNs with severe punishments and fines.
Take for example the Middle East. Aside from strict religious laws banning the use of VPNs, a series of events like the infamous Arab Spring protests of 2010 and 2012, have triggered Middle East countries to take action against VPN services.
If you don’t know what I’m talking about, I’m referring to the uprising of oppressed young Arabs that in most cases overthrew the governments of Egypt, Libya, Syria, and so on.
But what does toppling governments had to do with banning VPNs?
Well to give you a short answer, it was the use of social media that contributed to the escalation of the Arab civil war. In short, Tweets and posts shared on social media fueled the fire that caused the uprising.
For instance, Mouawiya Syasneh, the boy who started the Syrian civil war when he was just 14.
Aside from Middle Eastern countries blocking or making the use of VPNs illegal, there are also other oppressive countries blocking VPN.
Let’s take a look at some countries that ban the use of VPNs.
Countries that have Banned the Use of VPNs and Why
There are primarily 10 known countries that either block VPNs or have deemed the technology as illegal in the region. Let’s start with the most extreme country first, China.
1. China
China goes to great lengths to segregate the region from the rest of the world when it comes to the internet. China, as we all know, has implemented the so-called Great Firewall (GFW) to filter out and block restricted websites and services. However, you can access them with a VPN best for China.
If you don’t know what GFW is, it is one of the largest and most intricate technologies designed for mass surveillance and censoring.
The technology was inspired by the great Deng Xiaoping’s saying that goes: “If you open the window for fresh air, you have to expect some flies to blow in.”
Based on the same methodology, in the year 2003, the Chinese government initiated the Golden Shield Project, which is one of the world’s most extensive massive surveillance and censorship program targeted towards international content.
Considering that the CL97 legislation criminalizes cybercrime in China by law, bypassing foreign content using VPNs can be dealt with the full force of the law. At least you expect to be fined $145 for using VPNs in some part of China.
If you don’t know what the CL97 law is, it basically dictates that illegal activities conducted over computer networks are classified as cyber-crime.
This law is particularly concerning as it does not require the approval of The National People’s Congress NPC.
As a result of powerful blockades and online surveillance, around 1.4 billion Chinese citizens don’t have access to plenty of blacklisted websites.
Of the top of my head, these are some of the websites blocked in mainland China:
- Gmail
- YouTube
- Wikipedia
- Dropbox
- The New York Times
Just before the ban on VPNs got mandated, Zhang Feng, the Chief Engineer of China’s Ministry of Industry and Information Technology, said, “We want to regulate VPNs which unlawfully conduct cross-border operational activities”. [Source]
“Any foreign companies that want to set up a cross-border operation for private use will need to set up a dedicated line for that purpose. They will be able to lease such a line or network legally from the telecommunications import and export bureau” he further added.
Sounds fairly harmless right? Giving backdoor access to the Chinese government to spy on your internet activities.
That’s just absurd. After all, it is the exact reason we use VPNs in the first place.
That’s not all, the state on online censorship is so bad that in 2008, the Chinese government initiated “Operation Tomorrow” that requires Internet café owners to store customers logs.
The worst thing about such blockades is that they’re not going away anytime soon. Even Zuckerberg talking in mandarin to the Chinese president Xi Jinping didn’t prove to be too fruitful. [Source]
2. Russia
The Russian government doesn’t take online censorships lightly either. Why should it, after all the country has been involved in numerous high profile cyber security cases.
Whether it’s rigging the 2016’s presidential campaign or hacking mainstream websites, these are enough reasons for the Russian government to impose regulations on the internet.
It is exactly why in 2017, a law was passed by the Russian government to ban the use of VPNs. The reason for the ban you ask, to restrict the spread of extremist and unlawful content.
While on the topic of extremist and unlawful content in a high profile case that surfaced just recently, a Russian blogger (Ruslan Sokolovsky) convicted of promoting hatred and insulting a particular religion got 3 1/2 year suspended sentence that was later reduced by more than a year.
Even worse, Sokolovsky was also added to an official list of “terrorists and extremists”. [Source]
Although an isolated case, there can be much considering that legislation like Yarovaya Law in 2016, requires VPN services to register with the government and log users’ online activities.
But the harshness of the Russian laws doesn’t end just there. As it might be bluntly obvious to you by now, much like China, the Russian government also wants to restrict what content can be accessed in the country.
As a result, anyone caught using VPNs in Russia, can be fined up to $5,100. The penalties for VPN providers are even worse. Failing to comply with Russian laws, VPN providers can be fined up to $12,000.
That said since Russia doesn’t go overboard to spy on its own citizens like China, there’s no realistic way of identifying violators and imposing fines.
3. Iran
The western world isn’t the only one blocking or banning VPNs. Iran and other middle-eastern countries are also keen on blocking VPNs. Ever since 2013, Iran has been imposing harsh penalties on people using VPNs.
That said, only a few governments approved VPNs are allowed to be used in the country. However, since the so-called approved VPNs are regulated by the government, giving the government backdoor access to all secure data, it totally ruins the whole point of a VPN.
However, there is no social justice in the country when it comes to VPNs since it has been reported that government officials and other state-owned institutions consistently break their own censorship laws.
The Iranian government has also blocked a number of social apps including access to the internet in certain parts of the country during government protests throughout 2017 and 2018.
Due to strict restriction, if you’re caught using a VPN in the country, you can face up to one-year imprisonment. This is one country you don’t want to be using a VPN.
4. UAE
Another Middle Eastern country that takes strong actions against VPNs is the United Arab Emirates. Although a very liberal country as opposed to other countries in the region, it still for some reason considers VPN usage as a federal offense or a crime.
It makes no sense. You can buy liquor openly and party in clubs and stuff, however, if you use a VPN, you can be fined around 500,000 AED – 2 million AED, which is around $136,000 – $544,000. [Source]
However, the ban is only imposed on individuals using VPNs for personal use, since banks and other institutions can use VPNs freely.
This is primarily due to the government trying to profit from telecommunication companies. By blocking VoIP services like Skype, locals have no option but to use expansive talk time packages for national and international calls.
According to UAE’s law No 5 of 2012, local residents are only permitted to use to state-owned VPNs. Depending on the severity of the violation, residents can face life imprisonment or fines ranging between Dh50,000 and Dh3 million. [Source]
5. Oman
Similar to UAE’s law banning VPNs on an individual level, Oman also prohibits locals to use VPNs for bypassing prohibition VOIP services and accessing foreign geo-blocked contents.
Oman’s Telecom Regulation Authority (TRA) has proposed to pass regulations that will prohibit the use of Virtual Private Networks for individuals in Oman.
The proposed law imposes a fine of around 500 Omani Riyal which is around $1,300 for individuals and 1,000 Omani Riyal for companies that operate without proper permits. [Source]
However, it’s worth noting that the proposal for the new law was published in 2010, and there is no relevant information regarding the current stance on the proposed law.
VPN providers that offer obfuscation
Given that so many countries are blocking VPNs, only a handful of VPN providers offer obfuscation technology. With that said, here the top 5 best VPNs that support the obfuscation feature?
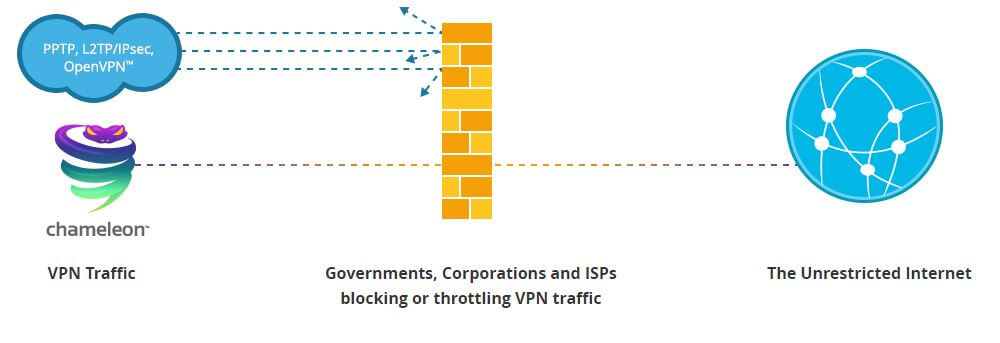
VyprVPN
VyprVPN is among the very few VPN providers that have developed their very own proprietary VPN protocol. Dubbed as the ‘Chameleon’ protocol, it effectively obfuscates 256-bit OpenVPN encrypted traffic and transmits it using port 443.
VyprVPN’s obfuscation technology is very effective at evading strict online censorship in regions with power Firewalls. According to VyprVPN’s website, the Chameleon protocol can bypass restrictions in China, Russia, India, Iran, and Syria.
This technology will be very vital to bypass high-level mass-surveillance and censorship which is already deployed in many countries. One of the prime examples of such a country is India. Very soon, the majority of their population will be forced to rely on VPNs to circumvent government censorship and surveillance. If you are in India, then you should read secure VPNs in India.
One another name for this technology is the internet traffic blocking phenomenon and it is being used by different VPN providers to circumvent the ISP’s firewall that are set up by the government. A good example of this scenario would be Turkey, where government-imposed censorship is increasing day by day, and citizens are forced to rely on this technology which is offered by best Turkish VPN, in order to bypass these restrictions and stay anonymous.
Aside from the super powerful Chameleon protocol, VyprVPN offers around 700+ servers in a 70+ global location. However, unlike other providers, VyprVPN owns and manages its servers.
VyprVPN is available for all major platforms including Windows, Mac, iOS, and Android devices. Features like Smart VPN, VPN Kill-switch, NAT protection, and many others is what makes VyprVPN such a desirable VPN to get.
Interested in VyprVPN? Make sure you check out our in-depth VyprVPN review.
NordVPN
Another VPN that effectively bypasses regional Firewalls like the GFW is NordVPN. Even though NordVPN is the worst enemy of most countries blocking VPNs, it still effectively passes all regional geo-restriction.
NordVPN even works in countries like China. Even though none of it 5000+ servers are located in China, NordVPN’s obfuscated servers are perfectly capable of accessing content within and outside of China.
While on the topic of servers, NordVPN offers a dedicated list of obfuscated servers. Since there are more than 450 obfuscated servers, you can pretty much unblock any geo-restricted content out there.
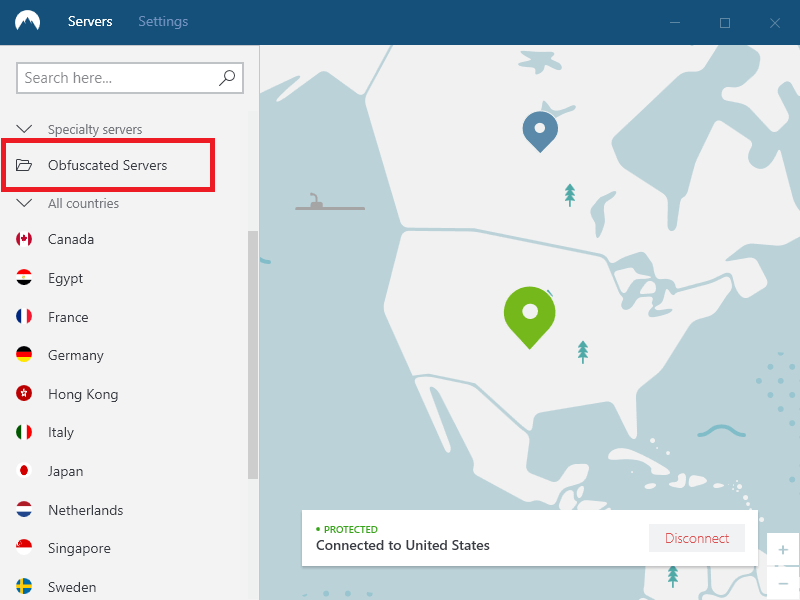
In addition to powerful obfuscation, features like the Kill Switch, Smart play, double VPN and military encryption is what makes NordVPN such a reliable and powerful bypassing tool.
Check out all the amazing features of NordVPN in our exclusive NordVPN review.
ExpressVPN

Although ExpressVPN doesn’t have a built-in toggle switch for enabling the obfuscation feature if you connect to their servers in Hong Kong, you can obfuscate your network traffic and bypass Firewalls like the one present in China.
Since the provider doesn’t log user data and located outside the jurisdiction of the 5, 9 and 14 eyes alliance, you can rest assured that your privacy is in good hands.
Aside from that, I can’t help but admire their super-fast speeds and their relatively large server park. At the moment they boast around 2000+ servers in some of the best locations around the world.
If you’re particularly into watching foreign content, you’d be glad to know that ExpressVPN offers a very nifty feature called the “MediaStreamer” which works as a Smart DNS service and helps unblock geo-even the most heavily restricted content.
Curious to find out all the other features of ExpressVPN, don’t forget to check out the complete ExpressVPN review.
IPVanish
Lastly, we have IPVanish. Unlike that doesn’t provide a dedicated option to enable obfuscation mode, IPVanish makes it dead simple to obfuscate your traffic with just a flip of a toggle switch.
Not only that, but you can also enable obfuscation on both their desktop and mobile apps. Enabling the obfuscation mode redirects all of your encrypted network traffic through the port 443.
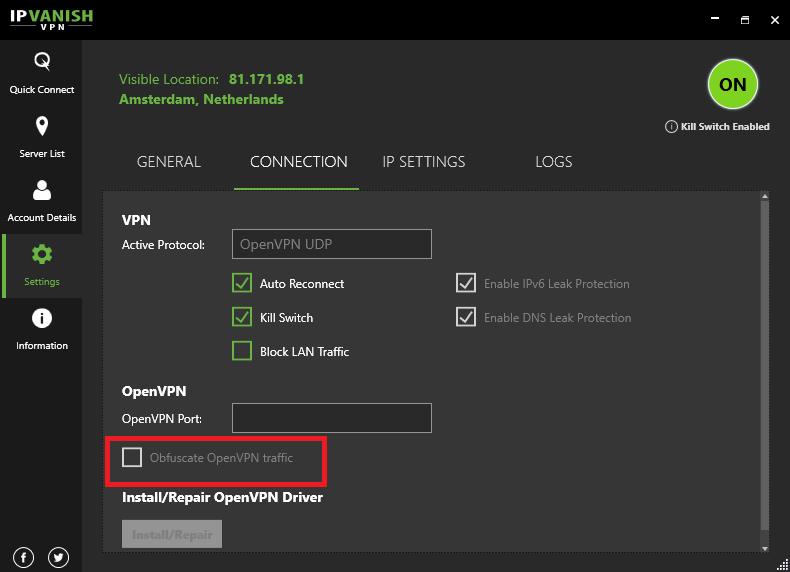
Aside from that, IPVanish boasts around 1,300+ servers in 75+ locations worldwide. You can find servers in pretty much every part of the world except for Antarctica.
Not only that, they don’t keep logs despite being in the US (part of 5 Eyes), they offer 24/7 customer support and overall amazing performance. Couldn’t recommend it more.
If you’re interested in checking out all the features that IPVanish has to offer, make sure to read the complete IPVanish review.
Final thoughts!
With the growing number of geo-restriction across the globe, instead of moving towards a borderless global infrastructure, the internet becoming more and more segregated.
While some content might be available in one county, that same content might be blocked in the other. Even if you aren’t necessarily experiencing blockades, you can be never safe from being surveilled by the 5, 9 and 14 eyes alliances.
Whether you’re residing in a liberal country like the US, or in a totally conservative region like the Middle East, you’re going to encounter internet censorship in one way or the other. And with the recent out the casting of VPNs, online blockades are the only getter harder and harder to get past.
With that said, state-of-the-art technology like obfuscation can reliably and effectively take down even the toughest of Firewalls.
To make it convenient for you, I’ve listed a handful of VPN providers that offer obfuscated servers, so you can easily access any content in China, Russia or any part of the world. If you want to know which other VPNs offer obfuscated servers then check out our blog Best VPN with Obfuscated Servers.
