
Every network based on IP packets has a Maximum Transmission Unit (MTU) size. The MTU, as the term suggests, is the maximum size of the packet that can be transmitted on the network.
IP packets bigger than the MTU size require being split into smaller fragments or packets so they can be traveled across the network.
Still confused? Don’t worry.
In this guide, we’ll explain all about IP fragmentation – what it is, what it does, how it’s used, and its drawbacks, in layman’s terms for understanding. We’ll further answer some specific queries of users related to the topic. So, without further ado, let’s get started!
What is IP Fragmentation?
Every local network supports a maximum size of IP packet. So, when a host uses the network to transmit an IP packet, it shouldn’t be larger than the Maximum Transmission Unit (MTU) size. Otherwise, it’s divided into small pieces – a process called IP fragmentation.
This size is usually determined by the MTUs and the data link of the network that is often the same. A contemporary workplace, data center, or campus network offered through Ethernet has MTUs worth 1500 bytes.
However, IP packets first transferred over a network supporting a single MCU might require routing across VPN tunnels, WANs, or across other networks with smaller Maximum Transmission Units. In case the size of the packet exceeds the smaller MTU, the data in this packet would need to be fragmented.
The data would be broken into multiple pieces and carried in new fragments (packets) that are smaller or equal in size than the lower MCU. This fragmented data will then reassemble when it reaches its destination.
Fragmentation allows for;
- Higher layer protocols and Internet Protocols (IPs) to work across diverse and variable network paths and mediums without a path discovery protocol.
- Transport layer protocols to downsize overheads and be ignorant of the underlying network architecture.
IPv4
The IPv4 Header Fields Used
The fragmentation and the reassembling process have various IP header fields involved that are set into pieces/fragments.
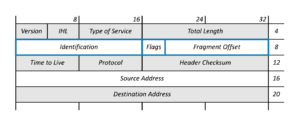
(Image Credits: packetpushers.net)
The operation of fragmentation relies on three IP header fields (a total of 32 bits). All these fragments will have values significantly different as compared to the original IP packet:
The Identification field (16 bits) contains a unique ID number which is a mixture of source and destination IP addresses. The Protocol field, having the original packet’s value, enables the destination to differentiate among the various packets’ fragments coming from the same source.
This simply means that the same ID can be utilized even when the source, protocol, and destination of the fragmented packets are not the same.
Exactly like the original IP packet, the first reserved bit of the Flags field (total 3 bits), and the second one, the Don’t Fragment (DF) bit will both be unset (0).
However, the final fragment will have the field’s third bit i.e. More Fragments (MF) set to 1. All the bits in this field of the last IP packet will be set 0, exactly like the original IP packet (unless it’s a fragment).
If in the original packet, the Don’t Fragment flag is set, then this would prevent fragmentation and result in packets required to be discarded. Errors should be sent to the sender in this case, like type 3 ICMP error: ‘Destination Unreachable’, code 4: ‘Fragmentation required, and DF set.’
The field Fragment Offset (total 13 bits) is utilized for indicating the initial data position in the fragment, in relation to the starting data of the original IP packet. This is then used for reassembling the data from all fragments (arrived or not).
The offset in the first fragment is 0 since the data in this fragmented packet and the original one start at the same place. In the following fragments, the value is offset of fragmented data from the starting of the data in the initial fragment (0 offset), in 8-byte blocks (also known as octawords).
If an IP packet containing data worth 800 bytes is split into two equal pieces/fragments, each carrying 400 bytes, then the fragment offset of the 1st fragment is 0, while the other one is 50 (400/8).
The offset value has to be the number of 8-byte blocks of data. This means that the previous fragment has to be a multiple of 8 bytes. The final fragment is allowed to carry data that isn’t a multiple of 8 bytes as there won’t be any more fragments.
IPv6
Even though most of the header fields remain the same, IP fragmentation in IPv6 works a bit differently than IPv4. In IPv6, data can only be fragmented on the source host. This means that fragmentation cannot be performed on other networks, except the source.
There is no Don’t Fragment flag available, so all you need to do is not create fragments.
IP fragmentation cannot be performed if PMTUD is not utilized. Nodes cannot use an MTU higher than 1280 bytes which is the minimum of IPv6 if they do not implement Path MTU Discovery (PMUTD).
While the Path MTU Discovery works in the same way as IPv4, the message of ICMP error is different:
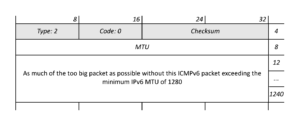
(Image Credits: packetpushers.net)
If the IP packet is larger in size than the MCU, then the IPv6 router has to discard it and send a type 2 ICMPv6 error ‘Packet Too Big’ – code 0 to the sender.
Please note that relying on a back channel and ICMP transmission to the originating host has multiple flaws – an important one being that ICMP messages are often blocked at various instances in a network due to security advantages.
This way, the originating host won’t receive the Packet Too Big messages and will retransmit the IP packets that were discarded various times, which certainly won’t reach. Eventually, the connection would be considered unstable and closed. Even if a new one would be established, the problem would repeat.
The header fields related to fragmentation are placed in an extension header called the Fragment Header. This is specified with a Next Header field (44 value) in a standard IPv6 or any previous extension header.
Just like all extension headers, this one is 8 bytes/64 bits long, along with a standard header, resulting in an IPv6 fragmentation with a higher overhead than IPv4.
The IPv6 Header Fields Used
Check out the fields in the extension header of the IPv6 Fragment:
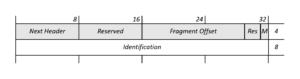
(Image Credits: packetpushers.net)
The field called Next Header (8 bits) specifies the header type, like an upper layer protocol header or IPv6 extension header. The next 8 bits are then reserved.
The 13-bits field Fragment Offset is used in a similar way as IPv4. After this, the next 2 bits are reserved.
The field M flag will be set to 1, and the final fragment will be set like IPv4’s More Fragments (MF) field.
The 32-bits Identification field is the same as the IPv4 field of 16 bits containing a unique ID number for the combination of source addresses and destination addresses. The Protocol field is unavailable in IPv6.
The Drawbacks of IP Fragmentation
The stack of IP protocol is deemed to have an unreliable mechanism due to which the end hosts cannot figure out the maximum size of the payload when communicating through an IPv4 and IPv6 host.
Even though the absence of an MTU mechanism across the network is understandable as the IP packets take different routes, the lack of end-to-end information can result in intermediary routers receiving oversized packets and being unable to forward them.
The IPv4 routers can split IP packets into fragments while transiting, but the same function isn’t available in IPv6 routers – where the sender has to perform the fragmentation.
Fragmentation results in a spike in the overhead of layer-3. So, for example, if the end host believes that it can use IP packets of 1500 bytes, but faces a hop in its path of MTU size 1472, then the IP packet would be divided into two packets, resulting in an added IPv6 header of 40 bytes and IPv4 header of 20 bytes.
IP fragments put an added burden on the receiving system as it’s required to reassemble the fragments to deliver them to higher protocol layers. This activity is aggravated when the router terminates the IP traffic.
If a router tries assembling the fragmented packets, the packets would fail to reassemble in the hardware and reduce the platform’s performance drastically.
FAQs
Why is IP fragmentation needed?
IP fragmentation is vital for the transmission of data since each network has a different size limit for processing data. This limit is also known as MTU (maximum transmission unit).
Do routers reassemble fragmented packets?
No, routers can fragment IP packets, but not reassemble them. It’s the work of the destination device to reassemble these packets for the user.
What happens if an IP fragment is lost?
If single or multiple fragments of a datagram are lost, then the complete datagram is discarded after the timeout period.
Conclusion
This ends our detailed guide about IP fragmentation.
To give you a quick overview, if the data being sent over a network is larger than the Maximum Transmission Unit (MTU) size, then the data would be divided into multiple fragments and sent over to the receiver.
As soon as the IP fragments reach their destination, they would reassemble in the correct order so the data can be useful to users. The mechanism of fragmentation is different between both IPv4 and IPv6 networks, the details of which are mentioned above.
In case you have any questions about IP addresses and fragmentations, please approach us with them in the comments.
