The ultimate purpose of a VPN is to maximize online security and safeguard user privacy. However, not all VPNs are equally good in performance and in their ability to keep yourself secure. But how can one be sure if a VPN is secure enough to be worth buying?
Well, there are a few critical tests you can run to determine the strength of your VPN. In this blog, I will explain how you can conduct these tests to check just how secure your VPN really is.
DNS Leak Test
DNS (Domain Name System) takes care of converting a website’s URL into an IP address. This process of translation is necessary because web browsers communicate with the Internet through IP addresses, rather the domain names, which are only used for the convenience of us human beings.

DNS translation is typically performed by the ISP (Internet Service Provider). However, the translation process leaves text logs of the websites you are visiting, allowing the ISP to see which websites you have been visiting.
So, DNS translation exposes you to the ISP and other third-parties that may be interested in invading your privacy for some reason.
If you use a VPN, then DNS translation requests are handled by the VPN itself, increasing your privacy considerably. However, if the VPN you are using isn’t strong enough, the DNS request can leak, revealing your browsing activities.
To test if your VPN is leaking DNS, you can use the web-based tool dnsleaktest.com. The standard test is sufficient to check if you have a DNS leak. If test correctly guesses your ISP, their IP address, and location, then your VPN is leaking your DNS and it’s time for you to invest in a secure VPN like ExpressVPN.
If the test shows a different location and ISP than the one you are connected to, then be glad, because your VPN is successfully tunneling your DNS requests without leaks.
IP Leak Test
A DNS leak does not reveal your IP address, but only that of your ISP. But that information is enough to reveal your true location and your browsing history.
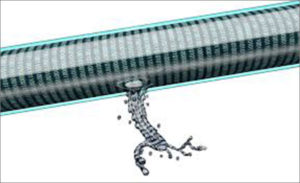
An IP leak, on the other hand, directly exposes your true IP address. Hiding the real IP of users is the main function of VPN services. If your VPN is failing to do that, then there really is no point using it at all!
You can test if the VPN is leaking your IP address through ipleak.net, an online tool. If it correctly displays your IP address and your location, then you surely have an IP leak and it’s time to get rid of your VPN for a stronger one, such as ExpressVPN.
Some VPNs may be effective in preventing IP leaks once you are connected to them, but not when the connection drops and the VPN is reconnecting. This is usually the case with VPNs lacking a kill switch feature.
It is harder to ascertain if your VPN leaks IP during the reconnecting phase, because you would manually have to conduct a series of tests in a quick succession while the VPN is reconnecting to find out.
Here is how you can test for an IP leak during Internet reconnection:
- Open the online IP leak test tool on a number of different tabs
- Keep the VPN running but disconnect your Internet.
- When the connection has dropped, reconnect to the Internet and quickly refresh all browsers tabs.
- As soon as the VPN has made connection with the Internet, stop refreshing
- If your real IP address is detected by the IP leak test tool in any of the tabs, then you have a leak during reconnection
WebRTC Leak Test
WebRTC is short for Web Real-Time Communication. WebRTC supports P2P sharing, video, and voice chatting via your browser without using browser extensions. Unfortunately, all browsers haven inherent vulnerability with WebRTC that exposes your IP address.
VPNs can prevent WebRTC leaks to an extent. The root cause of the problem are browsers themselves, rather than VPNs. So, if you want to get rid of WebRTC leaks completely, you shouldn’t rely on VPNs alone: it pays to change settings in your browsers as well.
So, what if you have a leak?
As I suggested earlier, you shouldn’t compromise on your security and continue using a VPN if you have learned that it is leaking your DNS or IP address. You may try contacting customer support of your VPN provider and complain the problem of leaks, but I doubt that will solve your problem.
The only thing you can do is to get rid of your insecure VPN and choose a reliable provider that values your privacy and security above all else.
The most trusted VPN providers that suffer from no such leaks are:
| VPN Providers | Price ($) | Special Deals | More Info |
|---|---|---|---|
|
Overall Best VPN

ExpressVPN
|
$12.95
$6.67
Per Month |
Exclusive Offer
Save 49% today! |
|
|
Fastest VPN Service

Surfshark
|
$12.95
$2.49
Per Month |
82% Off
2 Year Plan |
|
|
Best for Geo-Unblocking

NordVPN
|
$11.95
$3.99
Per Month |
69% Off
2 Year Plan |
|
|
Feature-rich VPN

PureVPN
|
$10.95
$3.29
Per Month |
81% Off
Exclusive 2 Year Offer |
|
|
Best for Private Browsing

CyberGhost
|
$12.99
$2.03
Per Month |
83% Off
3 Years + 4 Months Free |
Checking VPN for Malware
It is extremely sad that many VPNs on mobile devices, especially on Android, claiming to be free services fraudulently infect the devices of users who install these apps with malware. The intent behind this is usually to collect user data and make a profit by selling it to third parties (ad agencies, IT firms etc.)

You should never opt for a free VPN, as a lot of these are unsafe and make a fool out of users. The best way to stay safe from getting infected with a malware by a VPN is to avoid downloading and using free VPNs.
However, if you are still up for the risk, then you should at the very least upload the app to VirusTotal. This website scans uploaded files using more than 50 Antivirus tests and then gives you the result. If no virus is reported by the result, then you just might get lucky with the free VPN you want to use.
Fixing WebRTC Vulnerabilities for Different Browsers
The WebRTC vulnerability is not inherently a fault with VPN services. Rather, it is a browser related problem and it affects all popular browsers including Firefox, Opera, Chrome, and Brave.
The only true way to fix it is by disabling it the browser you are using.
Follow the instructions below to disable WebRTC for each browser:
Firefox
Firefox is the only browser where disabling WebRTC is a fairly simple thing to do:
- Open Firefox and type “about.config” in the address bar. Then press enter
- A warning screen will open. Click “I accept the risk!”
- Now, in the search box, type “media.peerconnection.enabled”.
- Double click the preference name to change the Boolean value to false
That’s all it takes to disable WebRTC in Firefox.
Chrome
Unfortunately, you cannot disable WebRTC in desktop version of Chrome, as Google provides no such setting to play around with WebRTC.
The only way to disable it in Chrome is through the use of third-party add-ons like WebRTC leak prevent. However, you should keep in mind that add-ons are not always effective in keeping you secure from exploitation of WebRTC vulnerabilities.
So, for Chrome users, the most effective solution is to simply stop using this browser altogether.
Though, you CAN disable WebRTC on Chrome for Android.
Here’s how:
- Open Chrome on your Android and visit the URL chrome://flags/#disable-webrtc
- Scroll down to see WebRTC Stun origin header and disable it
This action effectively disables WebRTC on Chrome.
Opera
Opera does not have any setting that allows users to turn WebRTC off, just like Chrome. The only hope is to use the WebRTC Leak Prevent extension.
- Install WebRTC Leak Prevent in your Opera
- Open Advanced options and > IP handling policy: Disable non-proxied UDP (force proxy)
Keep in mind that disabling WebRTC through add-ons is not a perfectly effective solution. So, if you’re paranoid about your privacy, you can avoid using Opera altogether.
Brave
Brave is emerging as a reliable browser with strong security and privacy options built into it. It allows users to disable WebRTC through settings:
- Navigate to Preferences > Security > WebRTC IP Handling Policy
- Now choose Disable non-proxied UDP.
Protect your online privacy and security while browsing with a best VPN for Brave browser.
Key Takeaways
- VPNs are supposed to enhance your security, not ruin it with these leaks
- Unknown and free VPN providers often have DNS, IP, and WebRTC leaks
Considering the facts noted above, there is little room for doubt that the true test of a secure VPN is one that doesn’t suffer from leaks of information having the potential to compromise a user’s security and privacy. If you choose a well-reputed premium VPN, it is highly unlikely that they will allow any such leaks from happening.
So, perform your tests, do your research, and choose your VPNs wisely, guys!
