Whenever I’ve researched about VPNs, I’ve always encountered the infamous “5 eyes”, “9 eyes”, and “14 eyes”.
However, I’ve never felt the need to properly address this topic until now. No matter where I look, all I can see is people seriously concerned about their privacy.
So after dedicating 96 hours to comprehensive research covering 123 VPN providers, I’ve carefully curated this guide to provide you with the most reliable insights.
By the conclusion of this guide, you will not only be well-informed about the jurisdictions in which various VPN providers are based but also how this impacts your privacy. You’ll gain valuable insights into which is the best VPN, ensuring that you can make an informed decision about which one to trust.
Here is a quick breakdown of countries in each of the Eyes alliance that are an enemy of the internet:
-
- Five eyes: United States, Canada, United Kingdom, Australia, New Zealand
- Nine Eyes: United States, Canada, United Kingdom, Australia, New Zealand, Denmark, France, Netherlands, Norway
- Fourteen eyes: United States, Canada, United Kingdom, Australia, New Zealand, Denmark, France, Netherlands, Norway, Belgium, Germany, Spain, Italy, Sweden
Is the VPN You’re Using Outside 5,9,14 eyes countries?
- What are 5 Eyes Nations?
- What are 9 Eyes Nations?
- What are 14 Eyes Nations?
- How Do 5 Eyes, 9 Eyes, & 14 Eyes Impact Your Privacy
- What Do Industry Experts Have To Say About 5 Eyes, 9 Eyes, 14 Eyes
- Invasion of Privacy Incidents: If Diana was spied upon, so can YOU!
- Implications of Selecting a VPN from 5 Eyes, 9 Eyes & 14 Eyes Countries
- Are Governments forcing VPN services to store users’ information?
- Surveillance Programs Operated by 5,9, & 14 Eyes
What are the Five Eyes Nations?
So, who are the five eyes?
Well, five eyes or FVEY is an alliance between the intelligence agencies of five nations. The core objective of the five eyes intelligence is collective surveillance.
Five eyes alliance includes:
-
-
- The United States – National Security Agency (NSA)
- The United Kingdom – Government Communications Headquarters (GCHQ)
- Australia – Australian Signals Directorate (ASD)
- Canada – Communication Security Establishment Canada (CSEC)
- New Zealand – Government Communication Security Bureau (GCSB)
-
First signs of five eyes intelligence alliance were seen post World War II and dates back to the UKUSA Agreement. The pact between the USA and UK formalized an alliance for intelligence sharing. The agreement has strengthened over the years and soon other nations (Australia, Canada, and New Zealand) were made part of the surveillance coalition.
But the five eyes alliance just doesn’t end there, in fact, as global threats increased and the need for more rigorous online surveillance arose, more and more global nations pitched in.
The Birth of 5/9/14 eyes alliance

The 5, 9, and 14 eyes surveillance alliance work in coalition to intercept and closely analyze both offline and online activities of the masses.
These intelligence agencies don’t just operate in their own designated jurisdictions, but also in other countries where they don’t have legal rights.
If for say NSA wants to track down someone in Canada, they can just ask CSEC to handle the operation for them.
The primary goal of these organizations is to fend off any threats to national security.
That said, as you shall see later on this blog, these alliances have also been involved in some very shifty spy operations against people like you and me.
5, 9 and 14 eye alliances are nothing new, they ’ve and have been operating under the radar. However, the general public was only made aware of the ongoing mass surveillance as recent as 2013 thanks to the whistleblower, Edward Snowden.
Subsequent to the Snowden leaks, The Guardian disclosed that the NSA had been secretly recording telephone records of tens of millions of Americans.
By now you must be wondering, how on earth they get away with unlawful mass surveillance?
Well, that’s because the governments backing five eyes alliance has passed bills that allow surveillance agencies to freely conduct such operations.
Here’s a rundown of few brute force investigatory legislations…
United Kingdom (Investigatory Powers Act, AKA Snoopers charter)
Back in 2016, the United Kingdom passed the Investigatory Powers Act. This act mandates ISPs and telecom companies that fall under the umbrella of the Five Eye to actively store connection information, text messages and even browsing histories of users.
Furthermore, these logs must be kept for two years (2) and must be made available to the U.K government and collaborating alliances. Worst of all, this data can be stored and shared without any form of legal warrant.
Australia (Assistance and Access Bill 2018)
Similar to the U.K’s stringent Investigatory powers Act, Australia’s recent Assistance and Access Bill gives law enforcement agencies unhindered access to encrypted user data. Australia’s equivalent legislation contains three different powers, but the one we should be all concerned about is the “technical capability notices” (TCN).
This power forces a wide range of companies associated with the digital sector to integrate spyware into devices and apps without the consent or knowledge of their customers. [Source]
In opposition of the new legislation, Greens’ senator Jordon Steele-John said in a tweet, “Far from being a ‘national security measure’ this bill will have the unintended consequence of diminishing the online safety, security and privacy of every single Australian”
What are the 9 eyes countries?

If you have seen the James Bond movie Spectre (2015), then you have an idea about Nine Eye Nations.
9 eyes is basically an extension of the five eyes alliance, and further includes four more countries. In total, 9 eyes countries include:
-
-
- The United States
- The United Kingdom
- Australia
- Canada
- New Zealand
- France
- Norway
- Denmark
- Netherlands
-
The overall goal of this arrangement between the nine nations is the same, share intelligence with each other.
First signs of this were seen when the Danish intelligence agency collaborated with NSA. The Danish authorities gained access to NSA tech while allowing the American intelligence agency to install surveillance equipment on fiber optic cables throughout the country.
What are 14 eyes countries?

The intelligence alliance further expanded between nations and included more countries, resulting in 14 Eyes. This agreement included both Five eyes countries, nine eyes country, and other nations:
-
-
- The United States
- The United Kingdom
- Australia
- Canada
- New Zealand
- France
- Norway
- Denmark
- Netherlands
- Spain
- Sweden
- Germany
- Italy
- Belgium
-
The objective of this arrangement was also the same: share intelligence information with each other, provide technical support, and allow respective agencies to conduct surveillance in the country.
How Do 5 Eyes, 9 Eyes, & 14 Eyes Countries Impact Your Privacy?
Ever sent an encrypted message? Of course, you have. In fact, WhatsApp, Messenger, and other mainstream social sharing apps have all incorporated end to end encryption.
Nobody wants people spying on them. Privacy of personal information is everyone’s basic necessity – Right?
Well, that’s what you think. Five eyes law enforcement group and other surveillance alliances beg to differ. Just last year, Five eyes countries have been pressuring tech companies to give them lawful access to all encrypted user data. [Source]
For instance, when the Russian Ambassador got assassinated in turkey, ExpressVPN’s servers got seized by the authorities.
Sounds crazy right? Just wait for what I have I store for you.
If granted access, Five eyes, and other alliances could legally intercept text messages, encrypted emails, and even voice conversations.
This is all real, swear to god I’m not scaremongering. I’m just as paranoid as you are.
To know more about factors other than jurisdiction that influence users’ privacy to certain extent, read our unbiased VPN reviews guide.
So why does FVEY wants to access to your data?
Well, according to the Australian government’s national security policy, encryption “present challenges for nations in combatting serious crimes and threats to national and global security”.
While encryption is a godsend for privacy-concerned folks like you and me, it’s also a holy grail for criminals, sex offenders, and even terrorist organizations.
Now I’m all up for catching pedophiles and countering terrorists, but I’m still not comfortable with global surveillance on the masses.
According to the Attorneys General and Interior Ministers of the five (5) nations, “The Governments of the 5 Eyes encourage information and communications technology service providers to voluntarily establish lawful access solutions to their products and services that they create or operate in our countries.” [Source]
“Should governments continue to encounter impediments to lawful access to information necessary to aid the protection of the citizens of our countries, we may pursue technological, enforcement, legislative or other measures to achieve lawful access solutions.” [Source]
In other words, if tech companies don’t comply with the Five eyes, they’ll forcefully get access anyways.
What are the risks?
So, what are five eyes basically proposing? Well, they want a master key to decrypt all encrypted data in transit. In other words, global backdoor access to encrypted communications.
What could even go wrong? (Sarcasm)
If you aren’t catching my drift, this is a serious threat to our privacy. Can you even imagine someone barging into your home and ransacking your personal belongings? Me neither.
As I said, Encryption is a basic necessity. We need it for banking, online shopping and making sure no one screws us over.
If Five eyes get a go-ahead to use backdoor methods of decryption, that’ll pave the way for other more malicious groups of individuals. [Source]
In theory, it would drastically change the way we perceive online privacy and our dependency on everyday apps.
A perspective on online mass surveillance
Ever since Edward Snowden blew the lid off of the Five eyes, more and more confidential information started to surface.
Two of the most revelations opens up a whole new Pandora box mass surveillance activities. According to official government documents disclosed by CBC News and The Intercept, the Communications Security Establishment (CSE) has monitored file downloading activities of millions of Canadians every day. [Source]
To be more specific, according to Edward Snowden documents, the CSE has been involved in storing and analyzing up to 15 million file downloads daily. [Source]
If that’s not terrifying, I don’t know what is.
That’s just one country, just imagine what atrocities FVEY can jointly wreak.
That’s not all. After already disclosing the unethical surveillance program of CSE, CBC News and The Intercept again disclosed shocking documents revealing the mass email surveillance of Canadian citizens. From the investigation, it was disclosed that Canada’s electronic spy agency collected around 400,000 emails to the government every day. [Source]
Without a doubt, such excessive monitoring is enough to generate an accurate profile of you and the people you interact with.
Paranoid? Well, hold on to your pants for this one…
According to Professor Ron Deibert, a collection of precise metadata can give surveillance agencies the power to “pinpoint not only who you are, but with whom you meet, with what frequency and duration, and at which locations.” [Source]
In conclusion, FVEY and subsequent alliances are spending billions of dollars on mass online surveillance.
What Do Industry Experts Have To Say About 5 Eyes, 9 Eyes & Fourteen Eyes Country
To get an external view on Five eyes, 9 Eyes, and 14 Eyes, we got in touch with some industry experts and asked their opinion and tips.
Arthur Cockfield – Professor at Queen’s University
Arthur Cockfield is a Professor and a member of the Faculty of Law at Queen’s University. His expertise is in Law and Technology, Privacy law, and Tax law. Our team reached out to Arthur and asked if there are any laws that protect users against governmental agencies from obtaining personal information.
The countries that participate in 5 eyes, 9 eyes, and 14 eyes are all democracies with a strong rule of law. Accordingly, each country has due process protections, with varying degrees, against government searches of personal data.
While there are some processes that safeguard users, but they can be overlooked when it is a matter of national security.
However, in many cases, national security concerns identified by ‘eyes’ countries can trump these due process protections. For instance, an intelligence service may be able to demand or access a users’ personal data stored by a VPN without obtaining a warrant or other legal mechanism with due process protections.
The above statement by Arthur clearly explains that even if a VPN is based outside an FVEY jurisdiction, there is always a chance that the provider would have to comply with legal notices such as warrants and subpoenas.
David Murphy – Senior Technology Editor, Lifehacker
David Murphy is an experienced tech writer and editor who has years of experience covering various topics related to technology. He is currently working as Senior Technology Editor at Lifehacker and our team asked him some question about VPNs based in 14 eyes countries and what tips can he offer our users.
According to David, choosing a VPN within the FVEY jurisdiction comes down to what is your purpose of use. He explained it through an interesting example saying, “If you just care about protecting your online shopping while you’re working at your local coffee shop, it doesn’t really matter.”
If you're running a BitTorrent server and you're looking to avoid the law as much as possible, I'd probably look for a VPN outside of the 14 eyes countries.
When we dug a bit deeper with David about trusting VPN providers based in the 5 Eyes, 9 Eyes, 14 Eyes, he said:
Generally speaking, you can probably get away with using a VPN within the 14 eyes countries so long as the provider uses solid encryption and doesn't keep logs, and the country where it's located has pretty strong privacy laws—like, say, Switzerland, though that's technically not a 14 eyes country.
This was an interesting take on the subject, and while we cannot stop to use the internet, David provided valuable tips that users can use to safeguard against agencies snooping on their activities. He said that it all boils down to how paranoid you are about your privacy and don’t want to be tracked.
“Burner devices. Tor. Running your own VPN that only you have access to. Not sticking to the same habits or routines for where you connect to the web. Not using a similar online handle for your secret / non-secret activity. Sandboxing anything you do in your OS, or keeping your nefarious activities limited to a virtual machine (or Live USB key, like Tails),” he advised.
Invasion of Privacy Incidents: If Diana was spied upon, so can YOU!
By now you might have an idea of what the five eyes countries are capable of. Now we’ll take a look at some of the outrageous invasion of privacy incidents committed by the infamous Five eyes
August 1997 – The Night Princess Diana Passed away
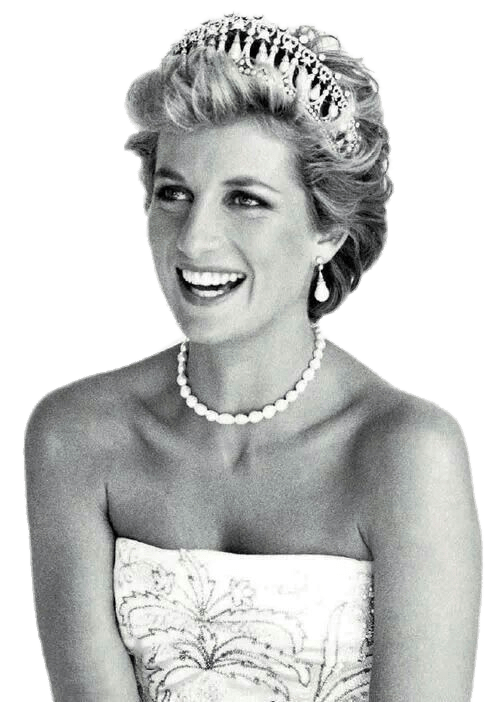
One of the most high-profile cases of the century, the American secret service bugged Princess Diana’s telephone conversations without the approval of the British security services on the night she died.
The princess of Wales had been under the radar of the five eyes surveillance alliance and primary spied upon by the NSA. More than a 1000 page dossier was compiled on the princess. Although some information related to the case was publically released, 39 classified documents will never be released.
In reference to her mysterious death, NSA later admitted that they were monitoring Princess Diana, but never actively monitored her movements.
At least that’s what the intelligence reports tell us, who knows what might be locked up in those 39 classified documents.
The 1970s– John Lennon under surveillance

According to former Sunday Express legal correspondent Fenton Bresler, classified documents obtained from the FBI and CIA reveal that Lennon was being tracked by the intelligence agencies during the 1970s.
NSA and GCHQ were reportedly speculated to conducting warrantless eavesdropping on the Beatles singer, John Lennon. [Source]
According to sources, intelligence agencies were becoming more concerned with Lennon because of his radical influence in politics. The FBI and CIA jointly ordered agents to continue surveillance on Lennon. [Source]
January 2012 – Unlawful Raid on Kim Dotcom

January 2012, New Zealand law enforcement personals in coordination with NSA, forcefully entered Kim Dotcom’s mansion ransacking his property and seizing alleged evidence of US copyright infringements. This case was particularly appalling, as it violated the GCSB Act article 14.
According to article 14, ‘[n]either the Director, nor an employee of the bureau, nor a person acting on behalf of the bureau may authorize or take any action for the purpose of intercepting the communications of a person who is a New Zealand citizen or a permanent resident.’
Even prior to his arrest, Dotcom had been under surveillance from December 16, 2011. Surveillance cameras were installed at a nearby property by the Organized and Financial Crime Agency New Zealand, (OFCANZ).
In addition, tiny pencam was used or was about to be used by law enforcement when they raided the Mahoenui Valley property on January 19, 2012, without a warrant.
Sadly, despite there being evidence of forced entry and physical abuse, law enforcement agents that conducted the raid, mostly denied the accusations.
June 2013 – Telephony Meta-Data Collection

On June 5th, 2013, Guardian, a major news publication firm, disclosed NSA’s National Security Telephony Metadata Collection program. [Source]
According to The Guardian, NSA collected the communication records of millions of US citizens, indiscriminately and in bulk. During the program, The NSA collected unique identifiers such as time and duration of all intercepted calls.
Naturally, the invasion of privacy of millions of US citizens was met with mass outrage and anger. Sadly, despite the unlawful eavesdropping by the NSA, The White Paper issued by the Obama administration deemed the program legal under section 215 of the USA Patriot Act.
That’s outrageous, to say the least. I mean, what gives them the right to tap our phone calls.
2013 – Brazilian Mining and Energy Ministry surveillance
One of the infamous cases of international invasion of privacy occurred in 2013.
CSE, an organization that had already been ridiculed for their outrageous surveillance tactics, went overboard and conducted surveillance operation on Brazil’s Mining and Energy Ministry.
An outrageous move indeed.
Soon after the matter surfaced, mass hysteria and anger were demonstrated by Brazil. Even the Brazilian President of that time (Dilma Rousseff) strongly condemned the violation of Brazilian sanctity by CSE.
January 2014 – Pearson Airport Wi-Fi spying

In January of 2014, CSE initiated mass surveillance on Canadian travelers using airport Wi-Fi at the Pearson Airport, Canada.
According to the details related to the case, CSE collected data of thousands of travelers without any warrant. The unethical operation went on for weeks and gathered very precise tracking information of travelers around the world.
That’s seriously messed up.
Speaking on this matter, Ron Deibert, a privacy expert, labeled the unlawful surveillance as, illegal and unconstitutional.
Deibert further quoted “I can’t see any circumstance in which this would not be unlawful, under current Canadian law, under our Charter, under CSEC’s mandates.”
I couldn’t agree more.
Implications of Selecting a VPN from 5 Eyes, 9 Eyes & 14 Eyes Countries
When it comes to selecting a VPN, there plenty of factors you need to consider. For instance, experts would advise to avoid VPNs that leak, use virtual VPN servers or aren’t transparent about their company or business.
However, the number one thing you should look for in any VPN service is the jurisdiction from which the VPN provider is operating its business. More specifically, is the VPN provider operating from Five eyes, 9 Eyes, or 14 Eyes countries.
Why is that?
Well, VPN providers have been pressurized by law enforcement agencies in the past and forced to comply against their will. Just to give you a perspective, let’s look at the case of PureVPN and HideMyAss VPN.
HMA user handed over to the FBI
Who can forget the case of the infamous log of HideMyAss VPN? For those of you who don’t remember, back in June 2011, Cody Andrew Kretsinger, then only 23-year-old, was sentenced to 15 years in prison after getting caught by the FBI.
Kretsinger was suspected to be a member of a malicious hacker group LulzSec. According to the allegations, he was accused of hacking Sony Pictures Entertainment servers using SQL injection.
Being such a high profile case, HideMyAss was ordered by the court to hand over Kretsinger VPN logs. Despite boasting about No logging policy, HideMyAss complied with the court’s order and handed over Kretsinger real home IP.
You can read the official case file at this [Source].
PureVPN helps the FBI catch a Cyberstalker
A bit different than the HMA’s case, PureVPN also cooperated with FBI. However, some may argue that PureVPN’s cooperation with the FBI was for a good cause.
Allow me to explain what I’m talking about…
In October 2017, PureVPN helped FBI identify a crazed Cyberstalker. Ryan S. Lin of Newton Massachusetts was found to be stalking a female victim. After getting a hold of the victim’s intimate photos and other information, Lin then distributed it to hundreds of online users.
However, according to the FBI, PureVPN aided the authorities in identifying the two IP addresses associated with Lin, effectively leading to his arrest. [Source]
So what does that leave you with?
This is where using a VPN based in an internet friendly location and preferably outside the Fourteen eyes is preferred.
However, there are several other factors to consider when choosing any Best VPN service. Among them is whether the provider keeps VPN logs or not.
If a VPN provider does not record or store your browsing and downloading history, they would have nothing to handover to the concerned authorities.
Likewise, with the introduction of GDPR, companies now offer greater transparency than before. But not all VPNs are compliant.
This is because selecting a VPN based solely on its location is difficult. Their jurisdiction of preserving user’s privacy and security cannot be determined based on the country of its operations.
VPN Jurisdiction: China
Only 3 to 4 VPNs work in China, mainly because the official authorities in China only allow a handful of VPN services to operate in the country.
The Chinese officials started a major crackdown against VPNs back in 2011. When people started having issues connecting to offshore websites and services, businesses and universities actually issued warnings to not bypass the great firewall.
Subsequently, in 2012, VPN providers reported that the Great Firewall of China was able to detect and efficiently block encrypted communications passed through VPN providers. [Source]
Although the country does not have any affiliation with 5 eyes, 9 eyes, and 14 eyes countries, you can still find yourself in trouble if the official authorities catch you red-handed.
Since VPNs in China are considered illegal, you can expect a hefty fine. According to The Inquirer, you can be fined $145 just for using a VPN. [Source]
Multinational organizations that are collecting personal information in China have to store that information within China too. They have to abide by the Chinese Data Protection Regulation (CDPR). The country is also planning to devise rules regarding personal information cross-border transmission. [Source]
If all of this sounds a bit complicated, I’ve extensively covered China-related issues and VPNs that offer obfuscated servers in my best VPN for China guide.
VPN Jurisdiction: Australia
Assessing the current legislations regarding online privacy in Australia, It feels like user privacy is fading at an alarming rate.
The Australian government is infamous for masquerading overly intrusive online surveillance programs as a need to safeguard national security.
The recent amendments to online surveillance legislations have legally granted intelligence agencies including federal and state police to request access to telephone and internet records.
Even encrypted communications is not totally safe. If we take a look at the “Telecommunications and Other Legislation Amendment (Assistance and Access) Act 2018”, government agencies have greater access to encrypted communications.
Similarly, in an attempt to counter piracy in the country, Australia’s Anti-piracy laws are speculated to blocking and potentially limiting access to virtual private networks (VPNs).
Copyright Amendment (Online Infringement) Bill 2018, can force telecommunication providers to prevent its customers from accessing particular online services. This bill is also applicable for VPN services since they can aid access to blocked content. [Source]
According to Communications Minister Senator Mitch Fifield, the copyright amendment bill will make it much harder for the operators of such services to bypass geo-blocks. [Source]
I’ve spent a great deal finding a quality VPN for Australia and I could only find a few.
As of now, VPN services are not blocked, but they do have to comply with data retention laws. These rules force them to keep data logs.
According to the Australian Prime Minister’s official site, you can use a VPN to access geo-restricted content. Nevertheless, this notion only applies to content streaming. As soon as users download or upload copyright content with the help of a VPN, they violate copyright law through VPN. They receive legal penalties in return.
Famous tech giants like Facebook and Google have shown their disappointments over the drafted Australian data bill. According to this, tech firms need to assist Australian police to decode specific forms of communications on their platforms. This act can greatly hamper the online privacy of Australians. [Source]
The same is true for New Zealand as well. You can use a VPN in New Zealand, because they are not considered illegal by the government. However, use of VPNs for illegal activities is a punishable crime in New Zealand.
VPN Jurisdiction: Canada
Canada is also an integral five eyes member and considered one of the harshest countries In terms of surveillance, data retention, and net neutrality. You can use a VPN within the legal parameters, however, intelligence agencies can use and share users’ information with other nations without their consent.
Windscribe, SurfEasy, and TunnelBear are just a few VPNs in Canada. You are going to be monitored, that’s inevitable. Therefore, it is essential that you opt for only those VPN providers in Canada, that have jurisdiction outside the 5,9 and 14 Eyes countries.
However, there are still some VPNs that can help you access content in the USA.
Similar to Australia, Canada also doesn’t consider VPNs to be illegal. However, if you violate the terms and conditions of any service, let say Netflix or Hulu, you can either have your subscription canceled or won’t be able to access the site at all. [Source]
Bypassing geo-restrictions through masking IPs, is in a gray area. In references to accessing streaming services through VPNs, Mitch Stoltz, a staff attorney at the Electronic Frontier Foundation said,
“While there are differences among the courts about the use of masking IP addresses to gain access to a site, it is pretty well established that simply violating the Terms of Service alone is not sufficient to warrant a violation of the Computer Fraud and Abuse Act.” [Source]
VPN Jurisdiction: United Kingdom

Just strongly clarify, the UK is in fact a five eyes country. VPNs are legal within the territory of the UK. There are no bans and no restrictions on VPNs either. But since the UK is a part of the five, nine, and fourteen eyes alliances, your VPN usage will inevitably be monitored.
As I mentioned earlier, the Investigatory Powers Act 2016, gives law enforcement agencies unimaginable power to carry out surveillance on their own citizens.
So while VPN providers are flourishing in the country, UK based VPN services have to follow British data retention laws.
For instance, you can exercise your freedom of expression right by hiding behind a VPN, however, Your online activities will still be under surveillance by the GCHQ. The same is true for other European countries like Italy, thus making the use of a VPN in Italy not a choice, but a necessity, considering the current online privacy scenario.
On the bright side, The GDPR (General Data Protection Regulation) has already started affecting UK tech organizations. Data Protection Act (DPA) 2018, empowers U.K citizens to take control of their data.
Here are VPNs with UK servers that can help you circumvent online restrictions in the UK.
VPN Jurisdiction: USA
VPN usage is lawful within the US. However, the country is a part of five, nine, and 14 eyes groups.
Therefore, surveillance agencies can track users’ online activities through the support of ISPs. In addition to that, recent overturn of the net neutrality rules by the FCC, has created a ripple effect.
The official authorities do not censor online content, but the VPN providers have to store their subscribers’ data logs.
Recently, the US has abolished net neutrality rule. As a result, ISPs can charge an extra fee for providing specific content streaming. The initiative could hurt small and medium-sized business firms quite badly in the future.
That said, price discrimination can be tackled by VPNs. Here are some Best USA VPN You can consider.
Are Governments forcing VPN services to store users’ information?
Yes and no, there are some jurisdictions that are exempt from online surveillance. For instance, there are no mandatory data retention laws in Hong Kong. That is because Hong Kong is a Special Administrative Region (SAR).
This is primarily the reason why most Hong Kong-based providers offer Source
Similarly, Panama and British Virgin Island (BVI) are the other two known jurisdictions that are free from data retention laws.
On the other hand, countries falling under the Five eyes, 9 eyes, and 14 eyes alliances have initiated stern actions that allow them to influence businesses to store their users’ data. They can compel VPN services to abide by the rules described by higher authorities.
This way, the information collected can be shared with other stakeholders. Intelligence agencies from other countries may also access the information if they wish to use it for their own purposes.
Surveillance Programs Operated by 5, 9 and 14 Eyes Countries
There are several surveillance programs carried out by the Five eyes countries. Thanks to Edward Snowden, we know details about most of these surveillance programs.
ECHELON
One of the most prominent programs involved the development of ECHELON surveillance systems during WWII. Built to monitor the Soviet Union’s communication, ECHELON computers were capable of storing millions of records. It was then later used to eavesdrop on private conversations and commercial communications.
Over 5 decades, ECHELON has aided the UK and United States to track enemies and allies alike with great precision. Although the scope has evolved since then the objective remains the same. [Source]
ECHELON was mostly talked about by conspiracy nerds, however, it was only until the Snowden leaks that everything came into plain sight.
The program was used by Bush administration to tap American phones without warrants. Just for perspective, one ECHELON facility in York-shire U.K monitoring 300 million emails and phone calls daily. [Source]
PRISM
PRISM is one of the most talked about surveillance program conducted by the five eyes network.
It was a code name project run by NSA and its main objective was to monitor and record internet communications.
Several tech companies were part of the program, including the likes of Google, Facebook, Yahoo, AOL, YouTube, Microsoft, Apple, and Skype.
According to the revelations unveiled by Edward Snowden about PRISM, NSA could conduct mass surveillance on live communications and record information such as emails, conversations over VoIP services (Skype), social media activities, file transfers, videos, pictures, voice and video chats, and internet browsing history.
Likewise, NSA and other intelligence agencies could summon special requests to ISPs and tech companies and demand for data regarding specific users.
The extent of surveillance was not only restricted to the NSA. Other intelligence agencies such as GCHQ of UK could also use the program to intercept communications of civilians. [Source]
In short, any operative from NSA, FBI, CIA, DIA or other agency could know anything about anyone using PRISM.
XKeyscore
XKeyscore is another program run by the NSA in collaboration with intelligence agencies from Australia and the UK.
The primary aim of this program was to search and analyze internet traffic from around the world.
Edward Snowden revealed top-secret documents pertaining to XKeyscore, unveiling how NSA was able to monitor, record, and analyze communications and internet usage of just about anyone.
In an interview, with a German broadcaster asked Edward Snowden about the capabilities of XKeyscore and he replied:
“You could read anyone’s email in the world, anybody you’ve got an email address for. Any website: You can watch traffic to and from it. Any computer that an individual sits at: You can watch it. Any laptop that you’re tracking: you can follow it as it moves from place to place throughout the world…”
Investigatory Power Act
The GCHQ and other intelligence agencies in the UK are just as involved in cyber surveillance as NSA.
With the passage of Investigatory Power Act, ISPs and telecom companies can record internet browsing history, conversations, text messages, and all other forms of communications.
This data is stored for two years and gives full liberty to intelligence agencies to access it for their use.
Other Notable Surveillance Programs
In addition to the above-mentioned programs, other initiatives undertaken by the five eyes nations or fourteen eyes surveillance network includes:
-
-
- Signals Intelligence
- Tempora
- STATEROOM
- MUSCULAR
- Data Retention Bill in Australia
-
Do Additional Eyes Exist?
Edward Snowden has revealed more or less 30 countries that are working as third-party partners. They support eyes countries by different surveillance acts like cyberspace monitoring, information, wire-tapping and so on.
Here is the list of countries that are acting as allies of eyes territories.
-
-
- Japan
- South Korea
- United Arab Emirates
- Singapore
- Israel
-
Huawei – Dividing the Five Eyes Alliance
Let’s be honest for a second, there’s no corporation out there that can challenge the five eyes, right? That’s what I thought too until I stumbled upon the news of the five eyes banning the Chinese telecoms giant Huawei from the 5G race.
But not all members of the 5 eyes alliance are on the same page. The US is campaigning hard to restrict Huawei from delivering 5G infrastructure over privacy concerns.
Bill Evanina, the head of America’s National Counterintelligence and Security Center had this to say:
“We have serious concerns over Huawei’s obligations to the Chinese government and the danger that poses to the integrity of telecommunications networks in the US and elsewhere”
“Chinese company relationships with the Chinese government aren’t like private sector company relationships with governments in the West.”
Even though the Huawei straight up denied being under control of the Chinese government, or that it poses any risks, the US is not only adamant about restricting the company but is also pressuring other allies to take the same course.
However, despite pressure, allies like the UK are considering collaborating with the solely because Huawei is the cheapest 5G vendor currently in the market.
But according to the latest updates on the matter, Australia and New Zealand have decided to take the same course as the US and ban Huawei from participation in their 5G networks.
What about Canada?
Well, it’s not concretely decided yet whether Canada will subdue to the US, however, according to speculations, Canada might take the same approach as the UK.
Since the 5 eyes members cannot settle on a collaborative decision, many have speculated that this will directly impact the intelligence sharing between the countries.
Tom Tugendhat, a former military officer who chairs the UK Parliament’s Foreign Affairs Committee had this to say on the matter:
“I think it’s hugely concerning because the Five Eyes relationship is fundamentally based on trust,”
“Injecting doubt into a trust-based relationship can undermine the fundamentals of the partnership. Particularly at a time when the liberal order is in question.”
If Canada and the UK go ahead with their decisions, it could ultimately mean limited information sharing between the alliances, or even quite possibly a complete dismantlement of the so-called five eyes alliance.
Final Words
If you’ve ever seen the movie, “Enemy of The State”, then you know how powerful NSA’s surveillance really is.
With surveillance programs stretching to international borders, several alliances have formed over the years. The most famous of all is the 5 Eyes, 9 Eyes, and 14 eyes countries.
These so-called “saviors” of our privacy have been caught doing some very shady stuff. I personally cannot trust them, and you shouldn’t too.
Now, I’m not against surveillance agencies. After all, they’re the reason we can sleep safely at night. However, don’t you think it might be better if at least they can be a little bit transparent about it?
Anyways, after personally researching VPN jurisdictions of 100+ VPN providers, I’ve rounded up only a handful of best VPN Services.
And if you’re not looking to spend a lot of money, we have great VPN deals and best christmas 2019 VPN deals for you as well!
You’re welcome.

Can you please suggest me which VPN is best for Children i need VPN for my kidz PC thanks
Hey, Lamar hope you’re doing well.
I would suggest you go for either PureVPN or Surfshark. Both these services are quite affordable and their user-friendly interfaces make it perfect for newbies.
So based on this article which VPN provider is the best one?
Hmm, that’s a tricky question.
I would suggest you do your own research or use the tool above to see if your VPN is outside the grasp of the Five Eyes.
But if I had to recommend one VPN, I would suggest you go with ExpressVPN. They are based in the BVI, offer a no log policy and have a pretty clean track record.
Express Vpn, is what I use. and so far its great,
I just have one small complaint sometimes the speed fluctuates from time to time . and also if anyone can advise me, how do i get my Dish network to work without having to sign off of express vpn. ?
Hey Dlong, speed fluctuations is something you’re going to experience with almost all VPN providers. The way out of this issue is to simply switch to a different server. As far as your dish network is concerned, can you please elaborate it a bit?