Any malicious software that is programmed to infiltrate your device, collect information about you and transmit it to any third-party entity without your permission to obtain profit is known as Spyware.
The software can be harmful to your private data as it can be misused and leaves you vulnerable to various data breaches. Spyware programs also have an impact on your device and network capabilities to perform at full potential.
By only becoming more aware of spyware, you can effectively protect yourself and your organization against them. For this purpose specifically, in today’s article, we will be discussing how to detect Spyware in USA and acquire protection against them?
Spyware in USA – What does it do?
Before we continue, we must establish that we refer to the malicious applications that access your device and steal your personal information by spyware.
Malicious spyware will conduct its operations in the following step-by-step process:
- Infiltrate — In the form of application installation, malicious website, or file attachment.
- Monitor and capture data — Recording keystrokes, screen captures, and other tracking codes.
- Send stolen data — Transmit the information to the spyware creator, for-profit purposes.
The spyware usually targets the following types of information:
-
- Login credentials
- Credit card details
- Keystrokes
- Browsing history
- Email address
Spyware in USA – How does it attack your system?
For spyware to infiltrate and contaminate your device without being discovered, the spyware creator tries very hard to disguise it completely. The usual way of accomplishing this is to hide the malicious files between unsuspicious download files and websites.
Upon downloading or opening these websites, the users unconsciously invite the malicious software into their system without realizing it. The malicious software will continue alongside trusted programs and websites through code vulnerabilities or in custom-made fraudulent applications and websites.
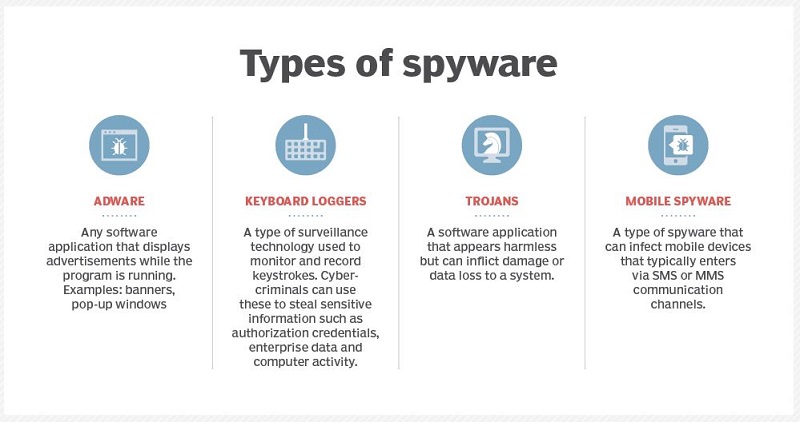
Different types of Spyware in USA
Spyware can’t be associated with just a single type of malicious program. So let’s take a look at the different types of spyware in USA:
Image Source: Search Security
Adware
Adware is responsible for collecting data regarding your browsing habits and history. That data is later on used to target you with relevant advertisements. Various third-party advertisers are willing to pay a lot for stolen data as the probability of earning a hefty revenue from targeted advertisements is very high.
One recent example of this spyware is the UltimaSMS Adware that spread through Google Play Store and corrupted over 151 Android apps that had been downloaded over 10.5 million times. It targeted the Gulf region and Middle Eastern countries.
Trojan
Masked as docile updates, attachments, or files, trojans are used specifically for stealing your data, sensitive information and inducing adware into your device.
Some examples of such spyware are FluBot that targeted Android devices back in August. It acted as a spyware and SMS spammer as well. Another example is the Android Joker malware that spread via Google Play Store in June, infecting over 1700 apps.
Keyboard loggers
Various cybercriminals use a monitoring procedure to steal personally identifiable information, log-in details, and other sensitive data belonging to any organization.
Employers can also use this procedure to monitor their employee’s activities, parents to oversee their children’s internet usage, device proprietors to trace any unlawful activity on their devices, or law enforcement agencies to investigate incidents involving computer use.
keylogging software can be downloaded on purpose or downloaded unconsciously and utilized as a remote access Trojan.
Mobile spyware
The ability to get transferred through SMS or MMS text message services and the fact that it doesn’t require any user interaction to perform commands makes mobile spyware the most dangerous of them all.
After getting affected by mobile spyware, the device’s camera and microphone can spy on the nearby activity and record calls and browsing history. In addition, the location of the owner can also be tracked via Global Positioning System (GPS).
Spyware in USA – Examples
Let’s suppose you have a medical condition and you searched online about a particular medicine. You’d notice that you will start receiving various advertisements that are somehow connected to that medicine or the medical condition for which that medicine is usually prescribed after a while.
This is how adware works.
Your search preferences and patterns are sold to paying advertisers so that they can run customized ad campaigns to entice you into purchasing products or services in USA. We have gathered a few examples of spyware in USA.
NSO Group Spyware:
According to the Guardian, Whatsapp accused an Israeli spyware company called NSO Group of hacking its 1,400 users. The users included various human rights activists, diplomatic officials, journalists, and even the Catholic priest in Togo.
Android Spyware targets Pakistani users:
In January 2021, trojanized versions of several legitimate apps, including the Pakistan Citizen Portal, were declared legitimate applications. These applications were spyware that was targeting Android users in Pakistan. Unfortunately, the creators of these legitimate apps were not even aware that a malicious version existed.
Spyware in USA – How to tell if you have been infected?
Several signatures can easily indicate that your device has been infiltrated by spyware in USA.
You have been infected with spyware if:
- Your device has become slow.
- Your device experience sudden crashes or freezes.
- You are experiencing annoying advertisements in the browser.
- You see various unexpected error messages.
- Your browser is acting weird and redirecting to new search engines.
These signs also indicate attendance of other malware, so you must dig deep into the issues and determine the root cause of the problem.
Spyware in USA – How to remove it from your device?
The removal of spyware is possible through solutions that can identify and remove malicious files. The first step of this procedure is to assure that your device is completely cleared of infection.
By doing this, you will ensure the personal information and data which you will set up on the device in the future will be completely safe from getting stolen. Purchasing security software that comes with spyware removal, the ability to clean the affected devices, and repair system files that the spyware may have infected.
Once your device is all cleaned up, it is essential to inform your bank regarding any potentially fraudulent activity on your credit card. In addition, if the spyware has affected an organization, then legal and regulatory violations need to be reported to the appropriate law enforcement agency.
Spyware in USA – How to protect yourself against it?
Here are a few tips that you can use to protect yourself against spyware in USA:
- First, implement strict firewall rules and use robust anti-virus or anti-malware tools that can help you secure yourself from various types of spyware.
- Always download and install software, games, other applications from a legitimate source. Avoid using third-party stores as they often contain different types of malware.
- Always check for the software developer or manufacturer code signing certificate to confirm the legitimacy of the software.
- Make sure always to update your software, hardware, and IT systems frequently. Not applying the updates will leave your device and network vulnerable to risks.
- Establish a habit of spreading cyber awareness. Employees who are agile enough to detect cyber risks can help keep important data and IT systems out of the grasp of cybercriminals.
Final Thoughts
The TOS or terms and conditions that you agree to without reading, the approvals you give to all of your applications, and various other free software that you download from untrusted sources all pave way for Spyware in USA to spy on you.
Without a doubt, data is invaluable. As a result, cybercriminals and various organizations spend so much time and effort to spy and crack your online activities. It is your job to ensure that your personal information and data aren’t stolen from you.