Phishing is the oldest trick in a hacker’s book. Yet, despite its age, this particular attack vector is the most enduring of them all. Over time, phishing attempts have largely improved in their ability to appear more legitimate and convincingly deceive the layman and – indeed – even cybersecurity experts in many cases.
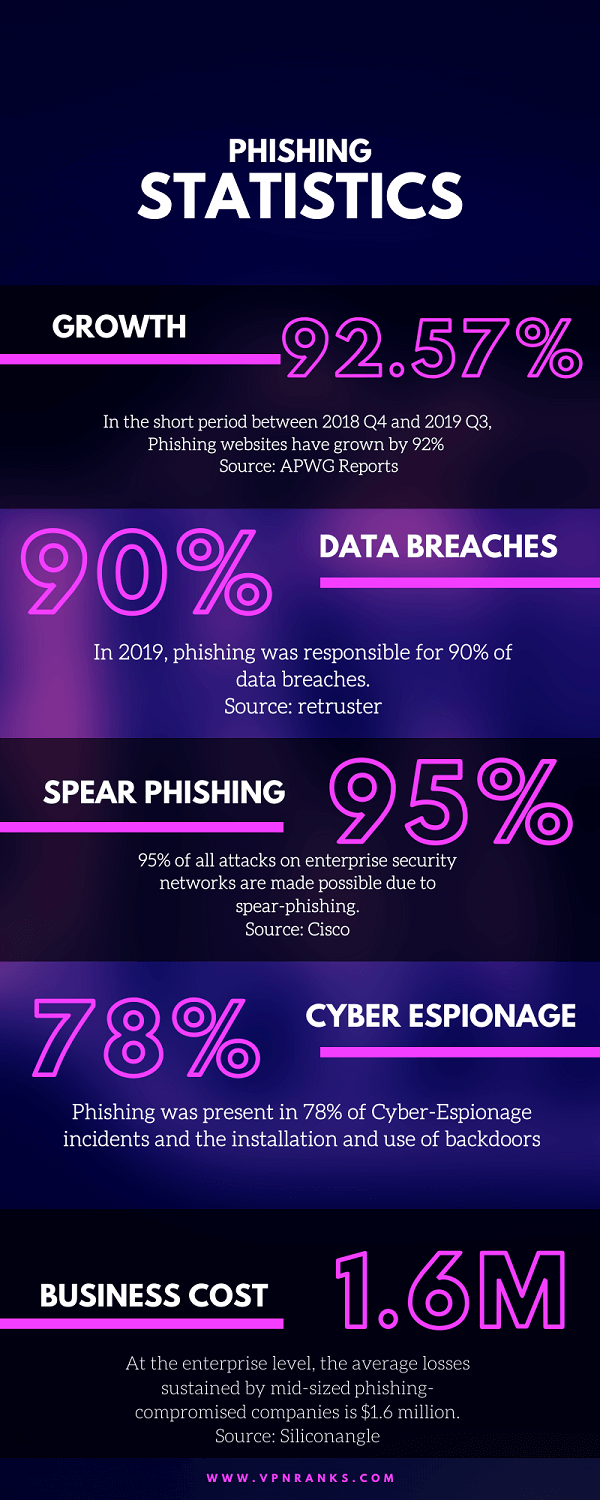
With the emergence of artificial intelligence, the Internet of Things, and related technologies, the volume, and virulence of phishing is only likely to increase. Unsurprisingly, APWG reports phishing websites to have increased from a number of 138,328 to 266,387, representing an almost twofold increase in the short period between 2018 Q4 and 2019 Q3.
That is only one of many alarming statistics that reveal just how devastating phishing has been in the recent past for people and businesses alike. Recent events, technological developments (AI and deep fake), and surrounding data worryingly indicate – as you’ll find out in this article – that the threat of phishing might become even bigger and more insidious than it already is.
And we might not be fully prepared for that.
Phishing Statistics – The Damage Done
The statistics of phishing show an upward trend, an unmistakable surge that hasn’t been observed for the past 3 years. Greg Aaaron, APWG Senior Research Fellow said “This is the worst period for phishing that the APWG has seen in three years, since the fourth quarter of 2016”.
According to Verizon, 32% of the data breaches reported in 2018 were a result of phishing attacks. This became even worse in 2019 with phishing responsible for 90% of data breaches. The stats suggest that hackers still predominantly rely on social engineering and confidence tricks rather than brute-force and other more sophisticated attacks to access sensitive information of users/businesses.
The effectiveness and high success rate of phishing attacks for cybercriminals can also be estimated from the fact that as many as 1.5 million phishing websites are created every month. Such extraordinarily high activity can only be sustained if the agents behind phishing are profiting handsomely off of it.
In fact, at the enterprise level, the average losses sustained by mid-sized phishing-compromised companies is $1.6 million. No wonder phishing has a special place in every hacker’s heart.
The enduring success of phishing is simply a result of our human tendency to be tempted to perform an action, especially when we trust the source.
Salvatore Stolfo, CTO at Alluresecurity aptly observes:
It’s true that AI can be reverse-engineered and weaponized by adversaries to target people with cyber attacks. But the reality is, when it comes to phishing, attackers do not even need to be that tech-savvy to succeed. And that is why phishing continues to endure as a top attack vector. It taps into our basic instinct to trust and click on a link that we believe comes from a legitimate source, such as your bank, or a brand you know and trust like Microsoft, Netflix or PayPal.
Evolving Methods – Phishers on the Storm
The methods and strategies for phishing are only going to get more sophisticated with time. In fact, improvements in techniques are already evident, pointing towards a seriously precarious cybersecurity environment in the times to come.
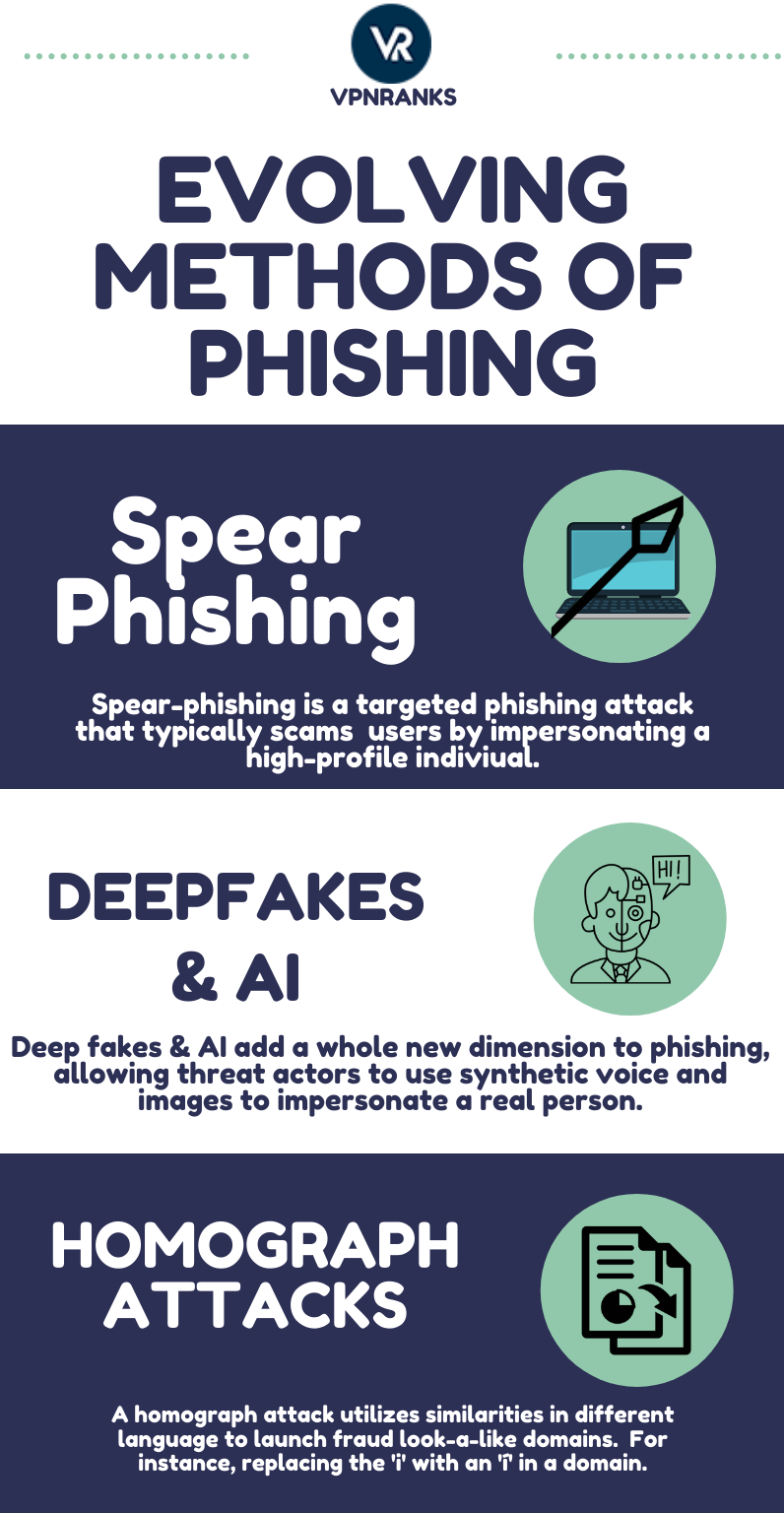
Spear-phishing
We’ve already witnessed changing norms when it comes to email phishing. Traditionally, the shotgun approach is more commonly employed when the hacker wants to lure as many people as possible. But attacks on enterprise security are considerably more likely to be successful when performed in a targeted manner, a technique known as spear-phishing.
Cisco claims 95% of all attacks on enterprise security networks are made possible due to spear-phishing. In a spear-phishing attack, a hacker might impersonate a real – often high-profile – member of an organization or industry in an attempt to hoodwink the receiver of the email to divulge their information.
Spear-phishing emails were taken full advantage of as the primary infection method utilized by 71% of hacker groups in 2017. The high success rate of spear-phishing is simply a result of better-disguised impersonation, luring even the more careful among us to being scammed.
Dennis Bell, an IT expert and founder of Byblos Coffee, predicts that:
In 2021, Spear phishing would be more prevalent… AI and ML can be used to identify the best targets based on what they do online. They can even gather information on who has the most access in their corporate network. Once AI and ML come up with profiles, they can start sending customized phishing materials based on the target’s vulnerabilities.
Deep Fakes and AI
The abuse of AI and the resulting development of technologies like a deep fake is another heavy blow to our hopes of a phishing-free internet. Before AI, phishers could only disguise themselves behind cleverly designed emails and websites. With AI and deep fake, they can even impersonate the face and voice of any person they choose, giving social engineering frauds a whole new dimension.
Kim Martin, VP Marketing at biometrics company ID R&D, points out:
Fraudsters are using Machine Learning and AI to conduct sophisticated phishing attacks where they impersonate real, authorized users through advances in synthetic speech. In a recent scenario involved a voice “deep fake” that tricked a CEO into transferring $243,000 to a Hungarian supplier. The CEO thought the request came from his boss. With these capabilities, fraudsters have found a new vehicle for social engineering and a way to get past biometric-based authentication if the proper protections aren’t in place.
Advancements in natural language processing open up another avenue for threat actors. Using machine learning to compose official correspondences designed to scam business personnel is a very real possibility today and almost certainly will become more prevalent in the future.
Natural Language Processing is one of the most actively researched fields in AI, capable of understanding human languages and communicate effectively using the same. As these capabilities improve over time, noticing the difference between human and machine originated language is going to be a huge challenge. As Digital Privacy Expert Attila Tomaschek highlights:
a cyber-criminal could inject a piece of malware into an existing email thread that has the ability to leverage AI and ML to analyze the language and context of the thread to learn and emulate natural human language and thereby tailor convincing, natural-sounding phishing emails to individual targets.” He also points out how AI-driven chat-bots can trick victims into clicking malicious links.
The most alarming fact amidst all these is that this isn’t a futuristic prediction that’s too far from the present day to start worrying about. These are very real capabilities that already exist to an almost frightening extent.
Machine learning can also play make phishing attacks undetectable. Over time, email can learn to bypass email filters, using more and more realistic language to appear completely legitimate. On this, Will Pearce, a Senior Security Consultant at Silent Break Security, shares
Adversarial Machine Learning has the ability to make phishing attempts undetectable – some research published in 2019 called ‘Proof-Pudding’ did just this. The Proofpoint spam filter was leaking spam prediction scores, the research collected a dataset and trained a model to output words that would ensure phishing emails went “undetected”. Machine Learning systems are a new attack surface that is generally not well understood.
Considering that simple algorithms can be used to determine even hidden pieces of information on Facebook profiles, the conjunction of deep fake and adversarial ML will significantly widen the range of attacks at the disposal of an average phisher.
Homograph Attacks
A homograph attack takes advantage of the fact that many letters in the alphabet of most modern languages are similar. For instance, the letter B is β in Greek. Knowing this, a malicious phishing website can use a domain name that looks exactly like another legitimate domain. The difference of one small character is often impossible to notice, especially on the screens of smaller handheld devices like smartphones.
For instance: https://www.theíndependent.com/ differs from the domain of The Independent in one character only: the ‘í’ for the ‘i’. These look-alike domains only add to the arsenal of techniques at the disposal of modern phishers.
The Future to Come – Corona, US Elections, & Abuses of Technology
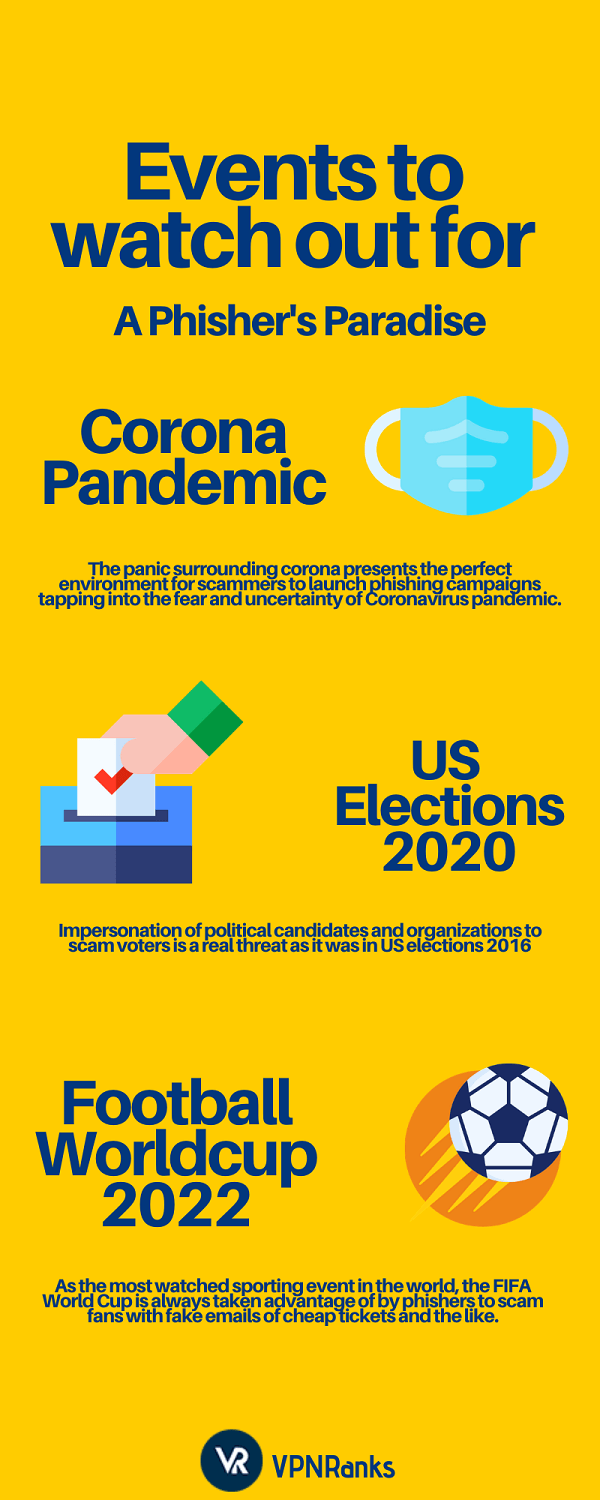
Technological capabilities represent only one area of opportunity among several that phishers are leveraging to launch increasingly devastating cyber-attacks. Capitalizing on the panic created by the mysterious coronavirus, scammers are launching phishing campaigns to deceive people into clicking malicious links and give sensitive information.
The most notable case of such phishing exploits was reported by Kaspersky where phishing emails pretending to be sent by the CDC steal your information when you click on a link asking for your Outlook login. The emails originate from a cdc-gov.org domain, though the domain of the legitimate CDC is cdc.gov.
Suffice to say, it is extremely difficult for an average user to notice this difference in the domain and suspect fraud, especially when the email is worded so convincingly with legitimate-appearing external links. Of course, there’s nothing legitimate about the whole email in reality.
These tactics draw their efficacy from the panic surrounding the situation (in this case, the coronavirus), where the prevalent uncertainty and urgency can short-circuit even a wise man’s judgment. Against real-life threats, the danger of cyber-attacks, no matter how real, is but distant and peripheral at best.
US Elections 2021 will present itself as another opportunity for phishers to go about their bad business as they did in the previous elections. As Orion Casetto, Director of Product Marketing at Exabeam, perceptively notes
Phishing is not going away anytime soon. The fervor surrounding the 2021 US presidential election provides would-be attackers the perfect environment to execute phishing and social engineering campaigns. Many people are passionate, ready to take action, and receiving a deluge of communication from new sources; this is a perfect storm that leaves ample opportunity for people to fall victim to well-crafted phishing emails disguised as communication from political organizations and candidates.
These events of importance coupled with the assistance of AI will only embolden phishers and scammers to deploy exceedingly pernicious campaigns targeted against every section of society from the individual to all sizes of organizations.
Preparing for a Phishing Outbreak
The best defense against phishing is still your plain old-fashioned judgment, intelligence, common sense, and cautiousness. Unfortunately, in a fast-paced world where people have declining attention spans and even lower patience, it is getting becoming quite a challenge to exercise care and caution before every link you click and every website you visit.
This is why anti-phishing software is also gaining in importance to assist humans with fallible judgment. Nonetheless, some common-sense tips can still save you from becoming the next phishing victim.
Share this image on your site
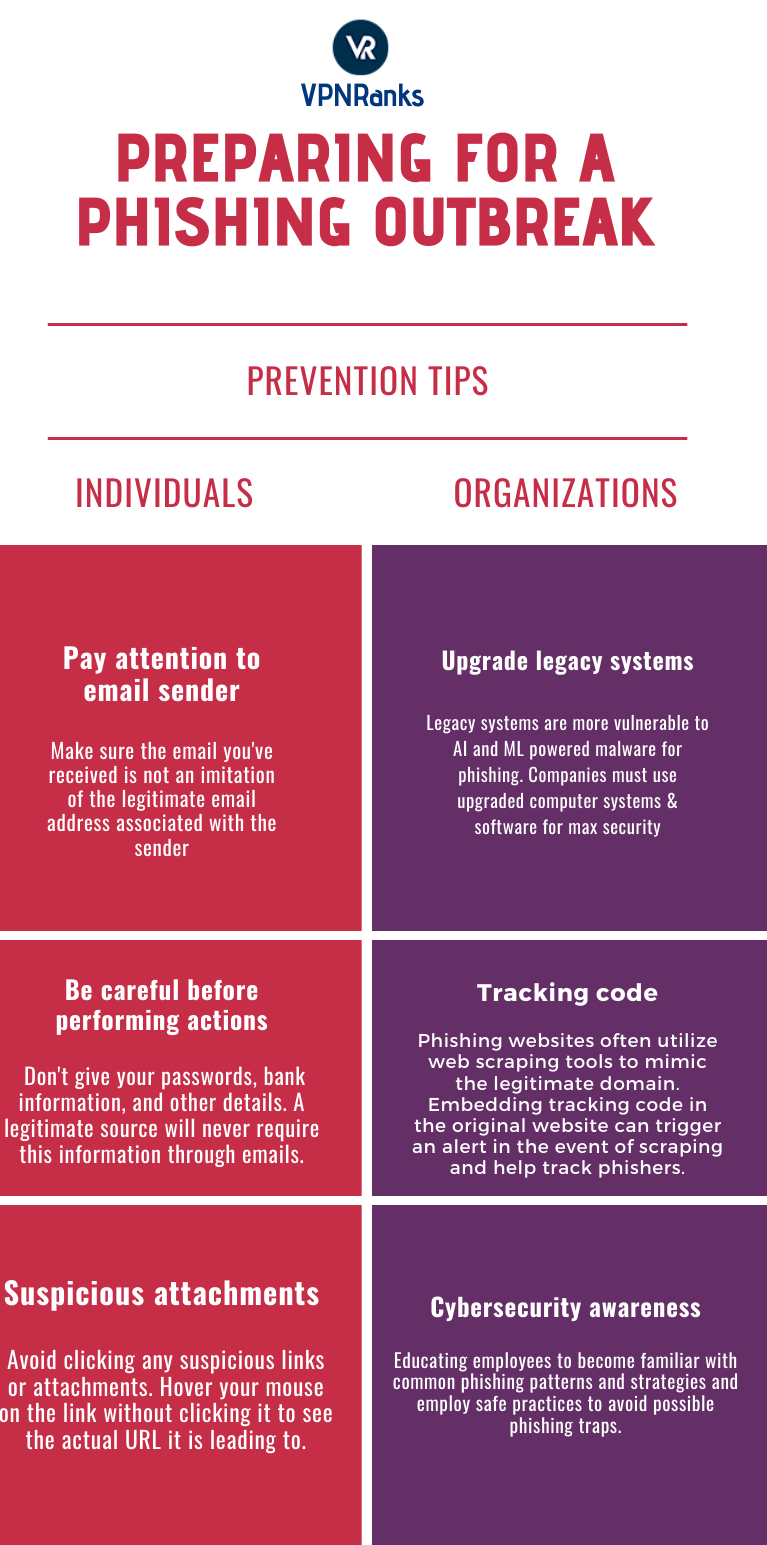
Tips for Users
- Pay attention to email sender: Always read the email addresses of senders in your inbox. Small spelling changes, characters, punctuations, etc. that indicate an impersonator are a huge red flag.
- Be very careful before performing actions: Phishing emails generally ask you to perform some action such as clicking a link and/or providing your passwords, PINs, bank account numbers, etc. Such emails must be avoided at all costs unless you are absolutely sure what you’re doing.
- Suspicious attachments: Another common characteristic of phishing emails is strange email attachments. If you see any files or links attached to an email that you’re not expecting, it’s best to avoid download or clicking anything. You can also hover your cursor over to an attachment or link for a while and check the actual URL it is pointing towards (without clicking it).
The Role of Organizations
These are some precautions you can take as a user. But there is heavier responsibility still on organizations of all kinds to tackle phishing more effectively. They can start by upgrading their vulnerable legacy computer systems to modern, updated ones as Threat Intelligence Team Leader at Skybox Security, Sivan Nir underlines
The 2019 NCSC report discovered that more than 318 public networks run on Windows XP despite Microsoft ending support for it in 2014. With companies relying on “legacy” software and cybercriminals utilizing AI and ML to mutate their malware, phishing attacks become nearly invisible to a company’s eyes and even more devastating.
Stolfo notes that most phishers often use web scraping to imitate the legitimate domain. He recommends embedding code in the original website that allows webmasters to track and detect whether their website has been scraped, taking the embedded code with it. This code then triggers an alert and gathers information about the hacker such as their geolocation to help track down the source of the problem.
While these measures are important for companies to improve their resilience against phishing attacks, there’s no substitute for user awareness as the most effective preventive strategy for tackling phishing. At its most basic, phishing is essentially an elaborate confidence trick.
It, therefore, stands to reason that users who are up to speed with current phishing trends are much better equipped for identifying a phishing attack – and correct identification is all that’s needed to stay safe from it. As the Packet Lab team notes:
The phishing trend will definitely be around for 2021 and ages to come. As Marcus Hutchins (a popular malware author) once purported, the art of reversing and making low-level malware is starting to become a lost art because phishing is just a much simpler way for adversaries and hackers to fulfill their goals. Packetlabs is a big believer of this, and often include phishing campaigns as part of our assessments to help raise cyber-security awareness and teach employees how to spot and hopefully avoid being phished
Final Word
All existing data points and future projections indicate that the threat of phishing as the most prevalent attack vector is here to stay. Indeed, phishing as a technique is rapidly evolving towards higher degrees of sophistication by leveraging the powerful capabilities of artificial intelligence.
If that weren’t enough the panic surrounding Coronavirus, the upcoming US elections, and other important events are only going to exacerbate the threat by serving as the perfect environment for insidious phishing campaigns to flourish and lure all manner of users at the individual and organizational level alike.
Despite the gravity of the current situation, it is the simplest measures that are going to be crucial if society at large is to pull through this difficult time: keep calm. But how calm can we remain facing a global pandemic that makes all other concerns – decidedly important in their own right – seem trifling in comparison?
