
L2TP is a mainstream tunneling protocol that’s used by almost VPN providers in USA nowadays. Though it is not as secure as OpenVPN, however, the fact that it can be configured to work on almost all internet-connected devices makes it really popular.
That being said, it is not the safest VPN protocol in USA out there. That’s because L2TP on its own offers no encryption. This is why L2TP is paired with IPsec to offer any sort of protection.
However, when paired together, the L2TP/IPSec protocol can be considered the second-best VPN protocol just after OpenVPN. The L2TP/IPSec combination is powerful enough that it can be used to prevent man-in-the-middle attacks and for data authentication.
So now that we have gotten that out of the way, there are plenty of VPN providers that offer L2TP protocol. But which one to choose? Well, in today’s guide, I’m going to list down the the best L2TP VPN in USA for 2023.
Best L2TP VPN In USA for 2023
To be honest, all premium VPN providers offer L2TP/IPSec protocol. However, since you’re here reading my blog, you have no idea which one to choose. Don’t worry though, I’ve got you covered. Here’s my list of best L2TP VPN in USA in 2023:
| VPN Providers | Price ($) | Special Deals | More Info |
|---|---|---|---|
|
Overall Best VPN

ExpressVPN
|
$12.95
$6.67
Per Month |
Exclusive Offer
Save 49% today! |
|
|
Fastest VPN Service

Surfshark
|
$12.95
$2.49
Per Month |
82% Off
2 Year Plan |
|
|
Best for Geo-Unblocking

NordVPN
|
$11.95
$3.99
Per Month |
69% Off
2 Year Plan |
|
|
Feature-rich VPN

PureVPN
|
$10.95
$3.29
Per Month |
81% Off
Exclusive 2 Year Offer |
|
|
Best for Private Browsing

CyberGhost
|
$12.99
$2.03
Per Month |
83% Off
3 Years + 4 Months Free |
How Does L2TP VPN in USA Work?
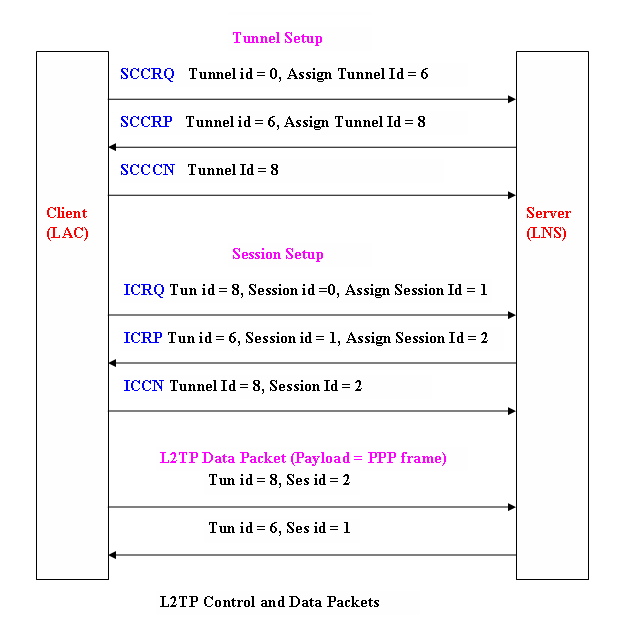
The L2TP VPN in USA essentially buffs up the PPP VPN. A traditionally functioning PPP will present a scenario in which data packets will be vulnerable during transmission from the client to the server (and vice-versa). The implementation of the L2TP VPN means that each data packet being transmitted will be subjected to an L2TP header. Upon receiving the data, the server will demultiplex the L2TP packets. This might sound like a bit of extra hard work and is known to lessen speeds, but the security it can provide in USA (in WiFi-powered internet sessions for instance) is priceless.
In tech-terms, the creation of the L2TP protocol means the combination of Cisco L2F and the Microsoft PPTP protocols. Bear in mind that L2TP VPN will weigh down on your CPU’s processing power because encapsulating data twice is a processing-intensive activity. Add the fact that 256-bit encryption is as near-mandatory addition to the L2TP VPN in USA, and you are looking at greater security at the cost of reduced speed.
Double Encapsulation in USA
Double encapsulation in USA is one of the fundamental reasons because of which L2TP VPN gained popularity over PPTP VPN in VPN use. Of course, L2TP VPN cannot stand up to the best VPN for OpenVPN in comparison, but it can take on the PPTP VPN protocol any day.
The first encapsulation of data takes place when the L2TP VPN functions much like a PPTP VPN and carried out encapsulation as if normal PPTP was in place. This is then topped off with the second encapsulation thanks to the IPSec. Encryption keys for the encapsulated data rely heavily on Data Encryption Standards if not on Triple Data Encryption Standards.
Reasons to Use a VPN Client for L2TP VPN In USA
L2TP VPN runs into complications when users in USA try to use it over routers or when excessively heavy firewalls are in place. This causes the L2TP VPN speed to fall in USA to the point that it undermines the utility of the protocol altogether. L2TP VPN can also prove to be challenging if you try to set it up and manage it yourself.
Our advice is to use the best VPN provider in USA that provides you with client software (a VPN connection manager) for your device. This will eliminate complications for you and let the software take care of all the complicated decision making and inter-software cooperation that takes place at the back end. Using a VPN client for your device will provide you with the comfort of plug and play VPN.
L2TP VPNs can prove to be somewhat irritating for individuals looking to switch servers frequently during VPN protected internet sessions. Using L2TP VPN in USA with IPSec protection (which is normal for L2TP VPN use) forces authentication to rely on your IP. Every time you switch a server, expect a connection-wide communication of your new IP to cause lag.
Using a VPN client in USA will help you gauge server traffic load for available servers and pick out servers with the right ping, upload speed and download speed for you. Doing so can help you compensate for the loss of speed you can expect to experience when you use the L2TP protocol.
Connect to a best L2TP VPN In USA by Using IPsec/L2TP VPN Protocol
The task of installing the best L2TP VPN in USA through IPsec/L2TP VPN protocol is straightforward. This is because you do not need any rocket science to complete the installation process successfully. Here is how you can do to install L2TP VPN on Windows, Mac, Android, and iOS devices.
VPN on Windows in USA Step by Step Guide
- You should right-click the network icon on the bottom right side of the screen and click “Open network and sharing center.”
- You should click on “Set up a new connection or network” option given on the “network sharing center.”
- Choose “Connect to a workplace”>Use my internet connection(VPN).
- You should open the VPN servers list and select a VPN server you wish to use.
- You should copy the DDNS hostname or IP address and paste it on “internet address.”
- Once you have pasted the internet address, check “do not disconnect now, just set up so I can connect later” option provided on the lowest part of the screen.
- Now insert ‘VPN’ on username and password fields once the username and password appears on the screen and check “remember this password” option.
- When you see “ the connection is ready to use” message on your screen, you can click “close” button however you should not click the connect now button.
- Go to “network and sharing center” > change adapter setting.
- Now right-click the icon you have to develop previously and click “properties.”
- From the properties screen, you should click the “security” tab.
- You can use the “network tab” if you have Windows XP.
- Select “layer 2 tunneling protocol with IPsec on the “Type of VPN” drop-down list.
- You should click the “advanced setting” and click on “use pre-shared key for authentication and insert VPN on the key field
- You should double click the newly established VPN connection setting and fill username and password fields automatically if you have activated password savings option in the earlier steps
- If it is not the case then you should insert “VPN” on username and password fields
- You should click on “connect” to begin the VPN connection process
- Once you have created the VPN connection, you will observe a VPN connection icon on your screen
- The VPN connection status should appear “connected.”
VPN on Mac In USA Step by Step guide
The same goes for Mac devices as you can install the L2TP/ IPsec VPN in USA on your Mac devices hassle-free. Here is how you can do to achieve your installation mission:
- From the top right side, click the network icon>open network preferences.
- You should click the + button given on the network configuration screen.
- You should choose VPN as an interface, L2TP over IPsec, as VPN Type, and click the “create” button.
- A new L2TP VPN configuration will be developed, you should specify hostname or IP address.
- You should open the VPN servers list page, click one relay server that you wish to avail.
- You must copy the DDNS hostname and or IP address and paste it to the server address.
- Once you have started the server address, you should insert “VPN” on the account name available besides the server address field.
- You should click the “authentication setting” and wait to see authentication message on your screen.
- You should insert “VPN” in the password field and on the shared secret field, after providing click OK.
- You must check the VPN status>Advanced.
- Click the “send all traffic over VPN connection”> click OK.
- You can connect to the VPN connection after clicking the “connect” option.
- The VPN connection status should appear “connected.”
VPN on Android In USA Step by Step guide
You can install the L2TP/IPsec VPN in USA on your Android devices accordingly. Here is the list of actions you should perform and these are:
- Through the “settings” application>wireless & network>more>VPN
- Click “Add VPN profile” to develop a new VPN connection setting
- Once you observe a new VPN connection screen, insert your preferred name for the VPN connection, select “L2TP/IPsec PSK” in the “type” field
- You should state the hostname along with the IP address of the public VPN relay server.
- Now open the VPN servers list then click on one VPN server you wish to use.
- Copy the DDNS hostname or IP address and scroll down the configuration screen.
- Click “Show advanced option” and specify “VPN” on the IPsec pre-shared key field.
- State “0.0.0.0/0” on the forwarding routes field and make sure to insert forwarding routes correctly.
- You must tap the “save” option then save the VPN connection setting.
- You can use the newly created VPN connection anytime from anywhere.
- From VPN connection setting, tap the settings option.
- You should insert the username and password then state “VPN” on username along with password fields and check to save account information.
- You should tap the VPN connection.
- Once you have established the VPN connection, you can see the connected VPN setting after seeing VPN activated message on your screen.
VPN on iOS In USA Step by Step guide
The iOS users in USA can install the L2TP VPN setup through the L2TP/IPsec protocol according to their own terms. Here is how you can achieve your installation objective:
- Through the iOS screen, you should go to the settings app.
- You should open VPN from General option and go to Add VPN Configuration.
- An L2TP VPN connection setting will be developed and you will see the configuration screen.
- You should specify the hostname along with IP address and open the VPN servers list.
- You should copy the DDNS hostname or IP address and specify the server field.
- You should insert the VPN to “account”, “password” and “secret” fields.
- Once you have inserted “VPN”, you should tap “save.”
- You can begin the VPN connection through a newly created VPN connection.
- You can tap the VPN to initiate VPN connection and you can see the VPN connection status on your screen.
Conclusion
At the end of the day, the best L2TP VPN in USA (for all intents and purposes), becomes an upgraded (bulked up) version of the PPTP protocol. It is the preferred (and most widely available) type of VPN protocol on account of the extensive compatibility it incorporates – as well as the heavy-duty data security it provides.
If you are looking for a VPN protocol in USA that can guarantee security and are not particularly concerned about losing a bit of speed during your internet session, then the L2TP VPN is the VPN of choice for you. It is recommended for business and pleasure applications – individuals who shop online (whether frequently or rarely) as well as those who are in the habit of making business-related financial transactions.
